Month: May 2024

What is Testing in Zillexit Software: A Comprehensive Guide
Zillexit Software, a leader in innovative solutions, recognizes that delivering high-quality products hinges on a robust testing process. Beyond identifying bugs, testing at Zillexit is about understanding user needs, mitigating risks, and ensuring customer satisfaction. This article delves into the intricacies of Zillexit’s testing methodologies, highlighting its commitment to quality and continuous improvement. Unlock the...
Unveiling the Best Deals: Explore the Ultimate As Seen on TV Store
Welcome to the ultimate TV store, where the best deals on innovative products are waiting to be discovered. With a wide range of products designed to make your life easier, this store is a treasure trove of the latest and greatest gadgets, gizmos, and must-have items. Step into our virtual aisles and prepare to be...

Capturing Memories: Photography Vintage Magic with the Perfect Camera
Step into the world of nostalgia and relive the magic of days gone by with the perfect vintage camera. In a world obsessed with digital images and instant gratification, there is something special about capturing moments on film. Whether you’re a seasoned photography or a passionate amateur, the allure of vintage cameras cannot be denied....

Anonymity and Identity Online: A Case Study of “Iamnobody89757”
Introduction The name “Iamnobody89757” has been seen all over the internet. People want to know what it means. This report will talk about “Iamnobody89757” in a fair way. It will look at where it came from, what it could mean, and how it has affected things. But it will also say if there is insufficient...

Cowordle: A Daily Word Puzzle Challenge and Beyond
The Cowordle word game is a fantastic game you can play in the world of word games inspired by Wordle. This daily puzzle allows players to guess a five-letter word within six chances while getting a colour-coded hint for each try. Cowordle, with its simple interface and entertaining gameplay, is the favourite among the word...

PCI DSS: Safeguarding Payment Card Data in a Dynamic Landscape
Introduction to PCI DSS The Payment Card Industry Data Security Standard (PCI DSS) stands as a set of necessary security rules that sets a secure environment for all the companies that handle credit card details. Since its establishment in 2006, PCI DSS has garnered strong public recognition as a managing body that has standardised requirements...
8 Mind-Blowing Cool Math Games That Will Sharpen Your Skills
Are you ready to discover a new way to sharpen your math skills? Look no further! In this article, we have compiled a list of 8 mind-blowingly cool math games that are not only educational but also incredibly fun. Whether you’re a math enthusiast or simply looking for a way to boost your problem-solving abilities,...

MeridianLink Data Breach: A Refined Analysis
MeridianLink is a big company. They helps banks and other money places with digital stuff. But on November 7th, bad people broke into their systems. These bad people are called ALPHV/BlackCat group. They used ransomware to get into MeridianLink’s computers. Ransomware is a form of malware that locks up data. The bad guys might have...
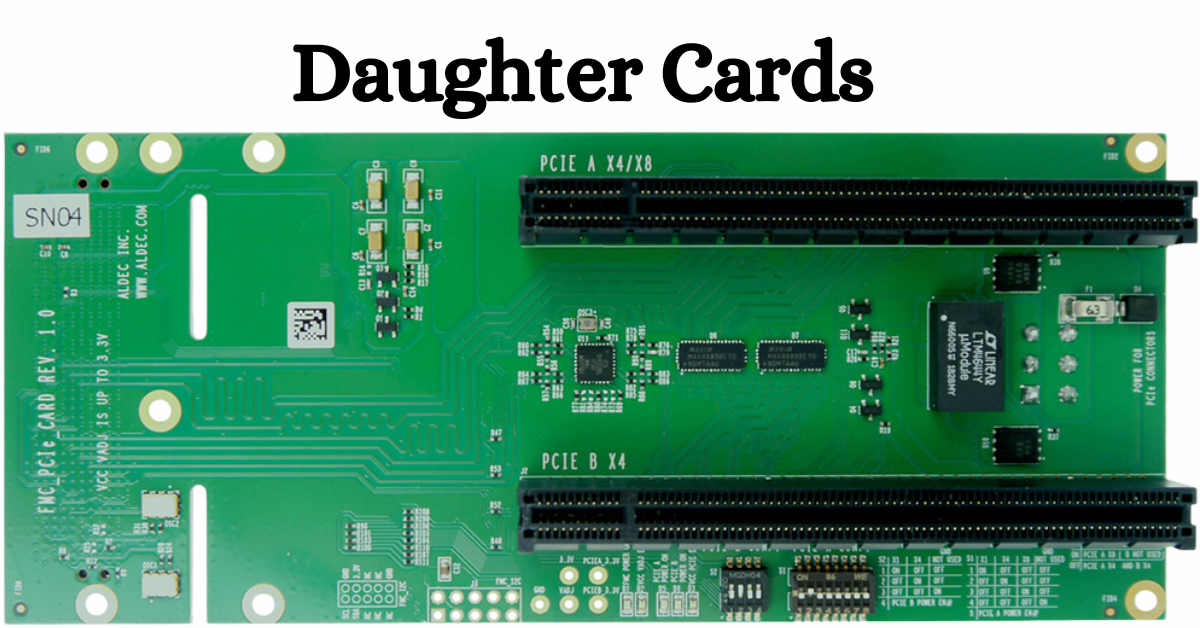
Daughter Cards: Expanding the Horizons of Your Computer
Daughter cards, also known as daughterboards or expansion cards, graft small circuit boards onto the computer’s motherboard, thereby expanding or enhancing its functionalities. They provide a user-friendly solution to upgrade your laptop in terms of hardware and price without purchasing the whole motherboard. Be it a gamer, a professional, or just a person who wants...

Demystifying the Cold Shoe: Everything You Need to Know
Are you new to photography or videography and are puzzled by the term “cold shoe”? Well, you’re not alone. The cold shoe is a simple yet essential accessory that often mystifies beginners in the field. This article will demystify the cold shoe and provide you with everything you need to know about it. From its...