Ahmad Farooq
Hi! my name is Ahmad. As a tech writer, I am specialized in making the complex world of technology accessible to everyone. Through in-depth reviews, helpful troubleshooting guides, and engaging articles, I break down the latest gadgets and software into clear, easy-to-understand language. My passion lies in empowering readers to get the most out of their devices and stay ahead of the curve in our ever-evolving digital era.
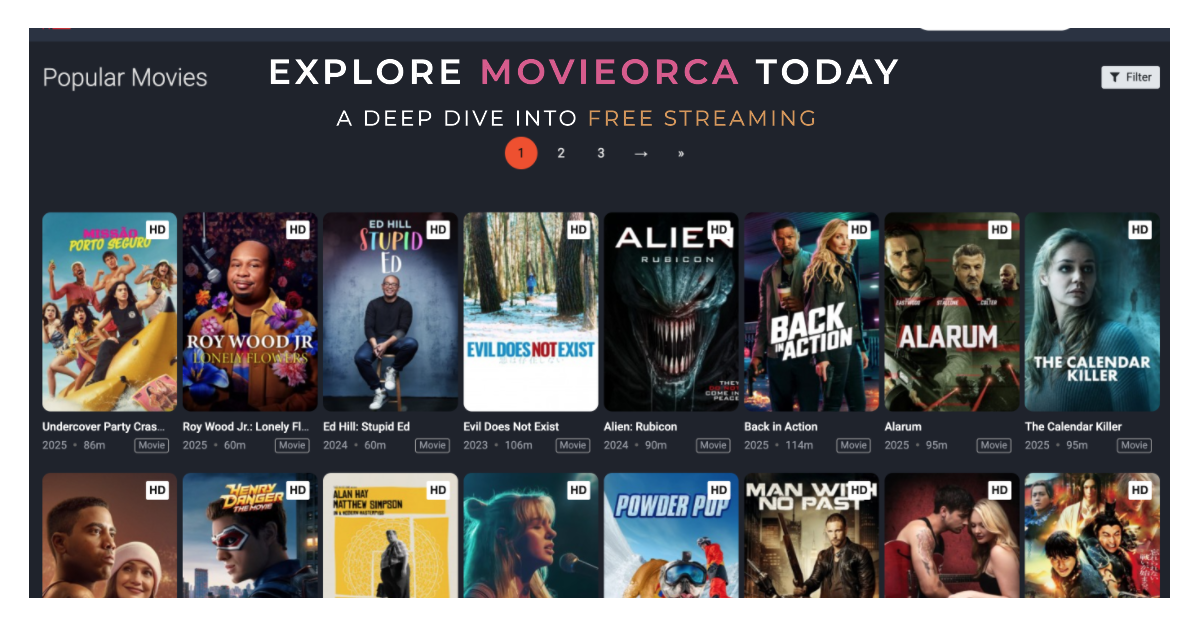
MovieOrca: A Thorough Analysis of the Free Streaming Service
The online streaming industry has skyrocketed, reaching dazzling new heights. It offers a treasure chest of films and TV gems in just a decade. Viewers are swept away in a sea of choices, finding something for every taste. Endless options await those craving drama, comedy, or adventure. Each click is a new journey. No matter...

Exploring Ring Network: A Journey from Token Passing to Modern Applications
Imagine a group of friends passing a ball around in a circle. Each person receives the ball, does something with it, and then passes it to the next person. This simple idea mirrors the basic principle of a ring network in computer science. A ring network is a type of network topology where devices are...

ACCA vs CMA: Which Qualification Will Boost Your Career?
Many professionals face whether to choose ACCA or CMA when looking to advance their careers in accounting and finance. The Association of Chartered Certified Accountants, the ACCA, and the Certified Management Accountant or CMA certifications offer global appeal and career options yet designed for different purposes and target different spheres of finance. This article aims...

5 Advantages to Leasing Office Space in Keppel Bay Tower, Singapore
Leasing office space in Singapore is a massive step for any business. Singapore has earned a reputation for a robust economy, strategic location, and unsurpassed infrastructure—all qualities inherent in every significant business. Among the many options, leasing an office space in Keppel Bay Tower, Singapore, could be one of the wisest decisions. It is a...

How do I Choose the best type of life insurance plan?
Choosing the right term life insurance plan might be difficult, but it is also a critical decision for both you and your family because it allows you to safeguard your loved ones from life’s uncertainties. You may still be unaware of the many types of life insurance policies available in India and how they affect...

Exploring the Impact of Brrrr Real Estate Strategy on Investment Returns in 2024
The landscape of real estate investing continues to evolve, and one strategy that has gained increased attention in recent years is the BRRRR method. Standing for Buy, Rehab, Rent, Refinance, and Repeat, this approach has shown promise for investors looking to maximize returns. In 2024, various factors are influencing the effectiveness of the BRRRR real...

Backlink Metrics and SEO Growth
Backlinks are the backbone of search engine optimization (SEO). They serve as a vote of confidence from one site to another, indicating to search engines the value and relevance of your content. However, as the SEO landscape evolves, so do the metrics that dictate the effectiveness of backlinks. Establishing the ideal quantity of backlinks for...

Enhancing Business Intelligence Through Effective Customer Data Integration Strategies
In today’s fast-paced digital landscape, businesses have access to an unprecedented amount of data. Leveraging this data effectively can set companies apart from their competitors. One of the most critical aspects of utilizing data is through business intelligence (BI) — the process of analyzing data to make informed business decisions. A crucial component of this...

Understanding Botnets: A Comprehensive Guide
Botnets are networks of compromised devices controlled by cybercriminals to perform malicious activities like DDoS attacks, spamming, and data theft.

How to Use Butt Connectors: A Comprehensive Guide
Butt connectors are cylindrical metal parts. They connect two wires end to end. Copper or aluminum forms these connectors, forging lasting bonds between wires. Their grip ranges from unbreakable to semi-permanent. They ensure reliable connections in various applications. Electricity flows through uninterrupted. An insulated sleeve encases these connectors. It protects the wire connections from the...