Asad Ijaz
NetworkUstad's lead networking architect with CCIE certification. Specializes in CCNA exam preparation and enterprise network design. Authored 2,800+ technical guides on Cisco systems, BGP routing, and network security protocols since 2018. Picture this: I'm not just someone who writes about tech; I'm a certified expert in the field. I proudly hold the titles of Cisco Certified Network Professional (CCNP) and Cisco Certified Network Associate (CCNA). So, when I talk about networking, I'm not just whistling in the dark; I know my stuff! My website is like a treasure trove of knowledge. You'll find a plethora of articles and tutorials covering a wide range of topics related to networking and cybersecurity. It's not just a website; it's a learning hub for anyone who's eager to dive into the world of bits, bytes, and secure connections. And here's a fun fact: I'm not a lone wolf in this journey. I'm a proud member and Editor of Team NetworkUstad. Together, we're on a mission to empower people with the knowledge they need to navigate the digital landscape safely and effectively. So, if you're ready to embark on a tech-savvy adventure, stick around with me, Asad Ijaz Khattak. We're going to unravel the mysteries of technology, one article at a time!"
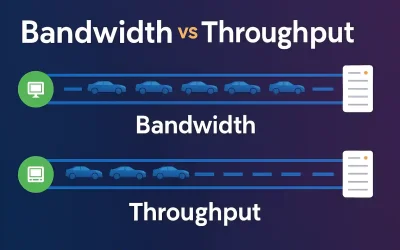
Bandwidth vs Throughput: Understanding the Key Differences in Networking
In today’s digital world, terms like bandwidth and throughput are frequently used in networking, but they’re often misunderstood or used interchangeably. Whether you’re streaming a 4K video, managing a cloud-based application, or setting up a local network, understanding the distinction between bandwidth and throughput is crucial for optimizing performance. This article dives deep into their...

Why Internet Connectivity is the Backbone of Live Experiences in 2025
When you think about what makes and breaks a mass event—be it a full trade show, a full tech conference, or a music festival outside—the most obvious things readily spring to mind: the speakers, the lights, the visitors, maybe even the food vans. But talk to any event operations manager in 2025, and you’ll hear...

What Should You Look for in a Wholesale Vape Partner?
A properly selected wholesale supplier will either create or destroy your business if you run the Vapor Shoppe or intend to enter the turning market. A reliable friend guarantees constant product accessibility, a reasonable price range, and first-class customer service. When choosing a wholesale vape partner, you can detect steamships, which are known for their...
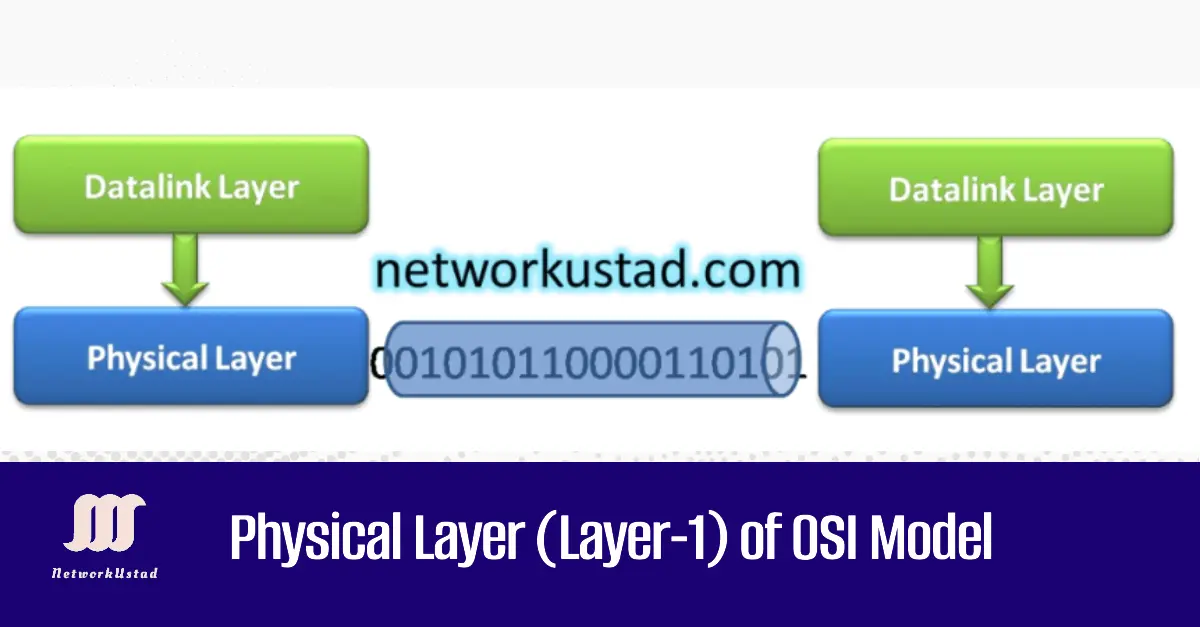
Physical Layer (Layer-1) of OSI Model
The Physical Layer is the lowest layer of the OSI Model. It provides the resources to transport the bits that comprise a data link layer frame across the network media. This layer accepts a complete frame from the data link layer and encodes it as a series of signals transmitted to the local press, as shown...
Comparison between TCP/IP and OSI Model
Comparison between TCP/IP and OSI models is critical because protocols that make up the TCP IP protocol suite can also be described in terms of the OSI reference model. The network access layer and application layer of the TCP IP models are further divided, and the OSI model describes discrete functions that must occur at...

Common Types of Cloud Malware in 2025: Prevention Guide & Best Practices
Whether it’s a private, public, or hybrid cloud, you love just about every aspect. Your cloud solution is saving your business time and money so what’s not to love? Unfortunately, the cloud can have a downside and it’s not one you want to ignore. Hackers frequently target the cloud and this can be disastrous. To...
Faxing Reimagined: How Modern Technology is Revolutionizing the Classic Process
Faxing, once regarded as an essential tool for communication, has seen a resurgence in the digital age. While many believed faxing was on its way out, modern technology has breathed new life into this old process. With advancements in cloud computing, mobile apps, and security innovations, faxing has evolved from its analog roots into a...
Enhancing Estimation Accuracy with Advanced Construction Software Tools
Ask any builder what keeps them up at night, and you’ll likely hear the same answer—cost blowouts. Whether it’s underpriced labour, missed items in a quote, or supplier price changes, inaccurate estimates can quickly erode margins and damage client relationships. For residential builders working across multiple projects, getting the numbers right from the start is...

Alternative Solutions to Payday Loans: What Are Your Options?
Many Americans feel compelled to use expensive payday loans when faced with a financial emergency. These short-term loans promise fast relief but sometimes come with exorbitant fees and interest charges, trapping clients in debt cycles. Fortunately, there are safer and more sustainable choices accessible today, such as the albert $250 cash advance, which allows you...

Swimming with Manta Rays in the Maldives: Everything They Don’t Tell You
The Maldives, known for its pristine beaches and luxurious resorts, is also home to some of the most incredible marine life on the planet. One of the most exhilarating experiences you can have while visiting this tropical paradise is swimming with manta rays. These majestic creatures are known for their graceful movements and massive wingspans,...