Asad Ijaz
NetworkUstad's lead networking architect with CCIE certification. Specializes in CCNA exam preparation and enterprise network design. Authored 2,800+ technical guides on Cisco systems, BGP routing, and network security protocols since 2018. Picture this: I'm not just someone who writes about tech; I'm a certified expert in the field. I proudly hold the titles of Cisco Certified Network Professional (CCNP) and Cisco Certified Network Associate (CCNA). So, when I talk about networking, I'm not just whistling in the dark; I know my stuff! My website is like a treasure trove of knowledge. You'll find a plethora of articles and tutorials covering a wide range of topics related to networking and cybersecurity. It's not just a website; it's a learning hub for anyone who's eager to dive into the world of bits, bytes, and secure connections. And here's a fun fact: I'm not a lone wolf in this journey. I'm a proud member and Editor of Team NetworkUstad. Together, we're on a mission to empower people with the knowledge they need to navigate the digital landscape safely and effectively. So, if you're ready to embark on a tech-savvy adventure, stick around with me, Asad Ijaz Khattak. We're going to unravel the mysteries of technology, one article at a time!"
How to Remove a Password from a PDF for Windows and MacOS
Sometimes it may happen that for security reasons we receive an encrypted file, but we want to remove security from it. If only because we open it often and entering the password every time is tedious. But how to remove the password from a PDF file? Below we will explain this process step by step...
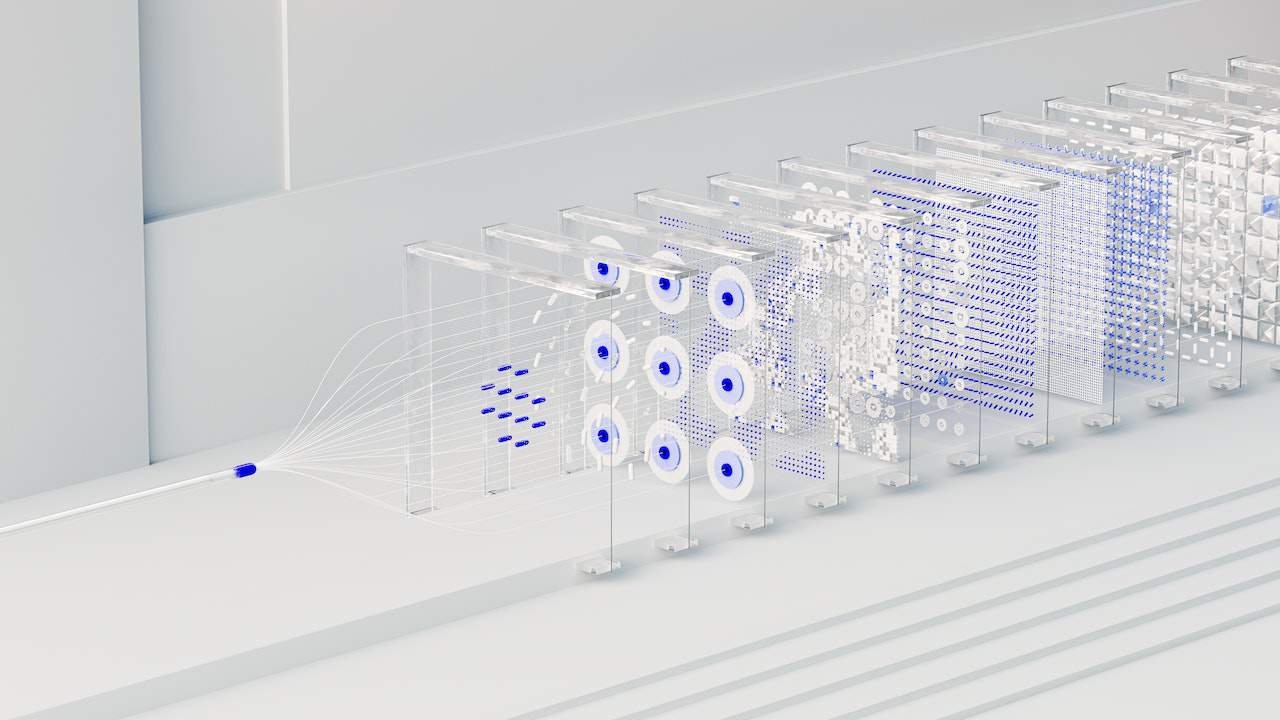
Unlock Real-time Insights with Salesforce Change Data Capture (CDC)
In today’s frenetic corporate environment, real-time data is more crucial than ever. Organizations seeking to increase productivity, enhance client experiences, and make intelligent decisions must have access to current information. Recognizing this need, SalesForce, a top customer relationship management (CRM) software, has a strong feature called Change Data Capture (CDC), which enables businesses to monitor...

Open Banking and its Transformative Impact on Enterprise Finance
The banking industry has undergone a revolutionary shift over the past few years, with digitization and financial technologies having the greatest impact. At the heart of this transformation is the concept of open banking. Primarily introduced as a mechanism to put power back into the hands of individual consumers, open banking also offers a range...

Impacting Communities Worldwide
Cryptocurrencies have taken the financial world by storm, revolutionizing the way we think about money and transactions. Beyond their potential for financial gain, cryptocurrencies have also become a powerful tool for driving social change and impacting communities worldwide. Through various initiatives and projects, individuals and organizations are leveraging the power of digital currencies to create...

Cryptocurrency in Gaming – Unlocking the Potential
The cryptocurrency market’s rapid growth has profoundly impacted various industries, and the gaming world is no exception. As the popularity of digital currencies continues to rise, game developers and players are discovering the numerous benefits and potential that cryptocurrencies bring to the gaming landscape. In this article, we will explore how cryptocurrencies are being integrated...

Rising to the Top: How SEO Link Building Solutions Elevate Your Brand
The Fundamentals of SEO Link Building In the realm of digital prominence, mastering the fundamentals of SEO link building is paramount. These intricately woven threads of connectivity hold the power to propel websites towards zeniths of search engine results. Embarking on this journey necessitates a meticulous strategy. First, content must reign supreme. Unique, shareable, and...
System and Network Defence
This article centers on the management of cybersecurity operations, encompassing activities such as designing, building, operating, and continuously enhancing an organization’s overall security capacity. The initial line of defense revolves around ensuring the physical security of network equipment. In parallel, there exist dedicated application security measures designed to safeguard software integrity. It’s crucial to acknowledge...
Defending the Digital Realm: A Comprehensive Review of OWASP
In an era where digital threats loom large and cybersecurity breaches continue to make headlines, safeguarding web applications is a paramount concern. Among the countless organizations dedicated to enhancing web application security, OWASP (Open Web Application Security Project) stands as a beacon of knowledge, collaboration, and innovation. Introduction Established in 2001, OWASP has evolved into...

Why Investing in Professional Artistry Elevates Your Custom Logo Pendants
In a world full of businesses and brands, standing out is essential. One powerful way to make a lasting impression is through a custom logo pendant. These tiny works of art can speak volumes about your brand identity, values, and style. Investing in professional artistry like Valeria Custom Jewelry for your custom logo pendants can elevate...

E-Bikes and Pedal Electric Bikes: Revolutionizing Transportation and Fitness
The world of transportation is undergoing a transformation, and at the forefront of this revolution are electric bikes, often referred to as e-bikes, and their subset, pedal electric bikes or pedelecs. These innovative machines are changing the way people move, commute, exercise, and connect with their environment. In this comprehensive guide, we will embark on...