
Networking
CCNA tutorials, Cisco guides, and enterprise networking insights for IT professionals.

How to Build Edge Network: Complete 2026 Guide
Master building edge networks with step-by-step instructions, case studies, and 2026 stats. Reduce latency by 60% and scale for IoT success.
Why Networking Companies Need a Logo That Communicates Technical Reliability
Expert guide to logo design for networking and IT companies covering trust signals, color psychology, and vendor examples.

How Delay Metrics Dictate Traffic Flow in Modern Networks
Delay metrics determine traffic flow more than bandwidth in modern networks—here’s how to configure them correctly in 2026 environments.

How Multiaccess Reduces Latency Without Additional Bandwidth
Multiaccess architectures reduce latency by 22% through dynamic path selection and QoS-aware transport—here’s how to implement them without instability.
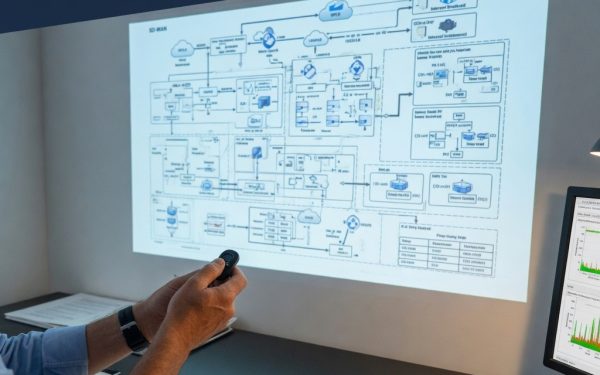
Why Hub-and-Spoke Topologies No Longer Serve Distributed Office Networks
A technical guide to office network architecture covering VLAN design, SD-WAN tradeoffs, ZTNA deployment, and QoS configuration for modern workspaces.

The Anatomy of a Networking Halfway House: Where Layer 2 Meets Layer 3
Halfway house configurations occur when network devices operate between Layer 2 and Layer 3 functions, creating instability and security risks.

How Smart Blinds Connect to Your Network: Protocols and Topologies
A network engineer's guide to deploying smart Windows Blinds: VLAN isolation, QoS policies, and security considerations.

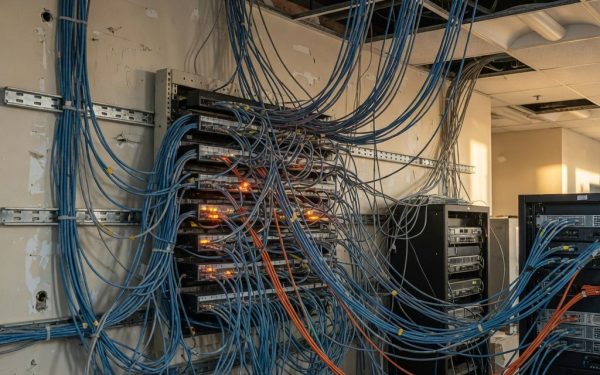
Private LTE/5G vs Wi-Fi for Industrial Sites: A Networking Perspective
A modern mine, refinery, or factory floor runs on data, and connectivity is now a production input. This guide compares private LTE/5G and industrial Wi-Fi across coverage, mobility, reliability, security, cost, and scalability to help planners choose the right network.

Network Architecture Essentials: Subnets, IP Whitelisting, and Managing Commercial IP Pools
This article explores how subnets, IP whitelisting, and commercial IP pools enable teams to build a controlled network layer for reliable web testing and data collection. It covers the importance of subnet separation, security policy simplification, and practical benefits for projects.

The Hidden Financial Benefits of Learning Networking Skills
Learning networking skills can lead to better job opportunities, higher earnings, and a more stable career in IT. Discover the hidden financial benefits.