Networking
Network architecture and protocol deep dives
Shielding Delicate Data: The Basic Significance of Information Security
In our undeniably digitized world, Information Security has become a vital worry for people, associations, and states. The expression “information security” includes a wide scope of measures and practices pointed toward safeguarding delicate data from unapproved access, breaks, and information burglary. As innovation progresses and information becomes more important than at any time in recent...
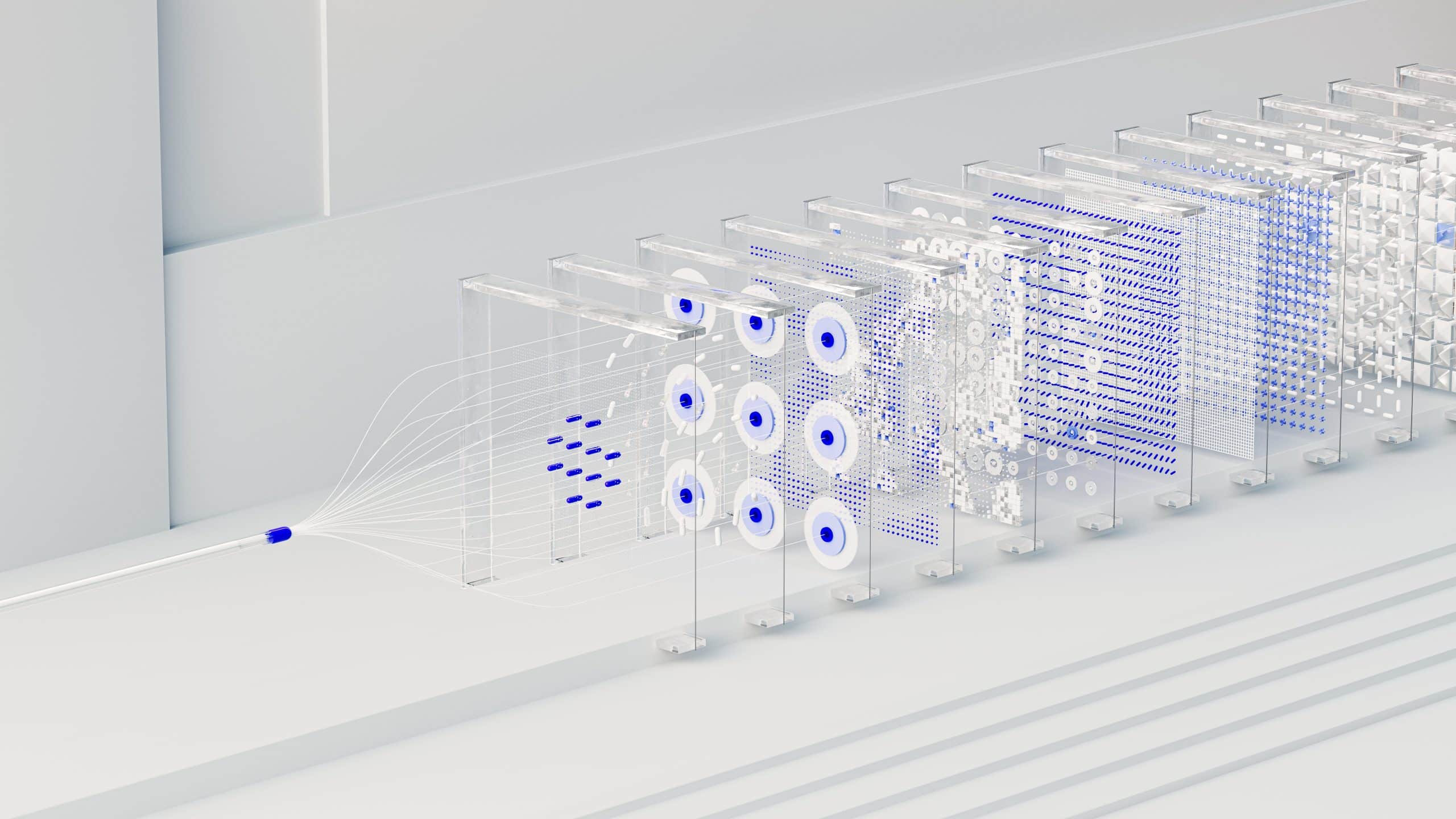
The Force of CIDR: A Major Justification behind Its Significance in Current System administration
In the consistently advancing universe of systems administration, productivity and versatility are principal. As our advanced scene keeps on extending, the requirement for more hearty and adaptable tending to plans turns out to be progressively basic. The Tactless Between Space Steering (CIDR) framework has arisen as a central participant in present day organizing, working on...

Effective PHP Web Development Tips For Improved Performance
Web Development, Despite its time in the market, PHP remains one of the leading languages used for website development. In fact, over 89,274,919 websites in the data are developed using PHP, including some popular names like Facebook, Wikipedia, and Etsy. Despite the meteoric rise of new development languages, businesses continue to rely on PHP for...
Mastering the Art of Safeguarding Controlled Unclassified Information (CUI)
Hey there, fellow digital guardians! In today’s tech-driven world, where sensitive data is the crown jewel, there’s a buzz about Controlled Unclassified Information (CUI) – and for good reason. CUI is like the secret sauce in your grandma’s recipe, and safeguarding it is our top priority. Picture this: You’ve got the digital fortress to protect...

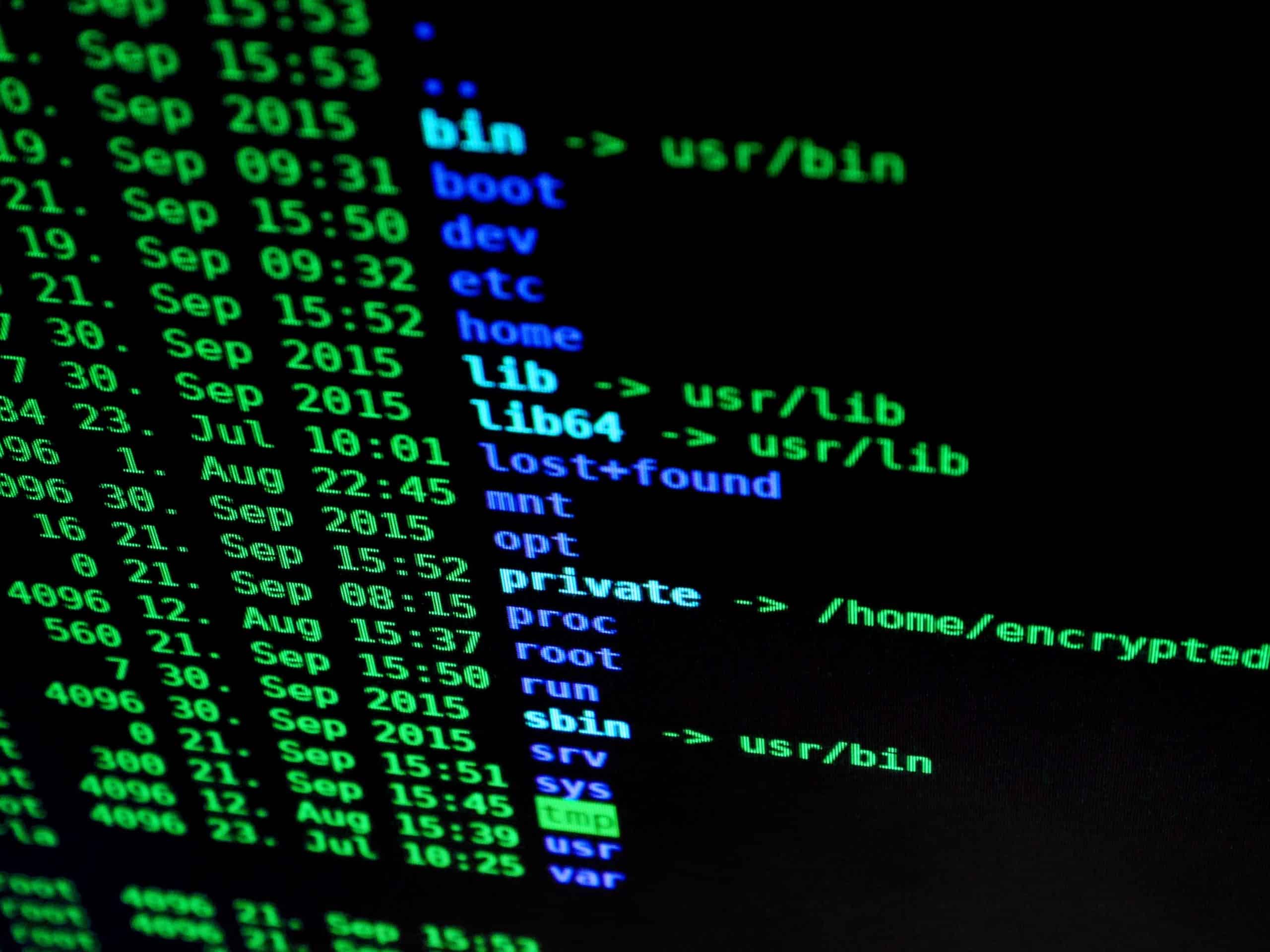
Navigating the Cybersecurity Universe with Parrot Security OS
In today’s fast-paced digital era, the cyber world is a realm fraught with danger and opportunity. As technology leaps forward, the threats to our digital lives grow in parallel. In this evolving digital landscape, your choice of operating system becomes paramount. Enter Parrot Security OS, the intrepid knight of the digital realm. In this engaging...

Demystifying Ethical Hacking: A Thrilling Journey into the World of White-Hat Wizards
Introduction In our fast-paced, technology-driven world, a hidden league of digital heroes toils away in the shadows, defending our virtual realm from the forces of darkness. These are the ethical hackers, the unsung guardians of our digital universe. In this exhilarating exploration, we invite you to join us on a gripping journey through the enigmatic...

Bolstering Your Website’s Defenses: The Epic Quest for Web Security
In the digital realm, your website is your fortress, your virtual stronghold. Whether you’re running a bustling e-commerce emporium, a vibrant blog kingdom, or a corporate citadel, safeguarding your digital realm is nothing short of an epic quest. For a breach in your web security is akin to a dragon lurking in the shadows, ready...

The Top 3 Advantages of Networking Tech for Restaurants
Technology has permeated nearly every facet of our lives, changing how we interact, work, and even dine. Ever reliant on delivering superior customer experiences and maintaining operational efficiency, the restaurant industry has found an invaluable ally in technology. As restaurants have come to recognize the power and potential of leveraging technological advancements, one particularly transformative...

Google Scholar Your Gateway to Scholarly Research
Google Scholar is like that trusty friend who opens up a world of knowledge for you. It’s an online platform that has completely transformed the way we dive into scholarly research. With a vast database at its core, it offers scholarly articles, theses, books, and conference papers across diverse academic disciplines. In this article, we’re...
Hierarchical Network Design
Physical and Logical Addresses A person’s name is typically a constant identifier, much like a MAC address in computer networking. A MAC address is a unique, hardware-based identifier assigned to a network interface card (NIC) and remains unchanged regardless of where the host is connected on the network. It serves as the host’s physical address,...