Search Results
Showing results for "business" (3266 articles found)

Securing Mobile Ecosystems Is Essential for Long-Term Business Stability in 2026
Mobile ecosystems have become the backbone of modern business operations. From customer engagement and digital payments to internal workflows and remote access, mobile applications now play a critical role in ensuring efficiency and growth. However, this widespread adoption has also expanded the attack surface for cybercriminals. Mobile malware, data leaks, app tampering, and unauthorized access...
Why Outsourced IT Support Is Becoming Essential for Growing Businesses
As businesses grow, technology becomes more complex and more critical to daily operations. What once worked for a small team often struggles to keep up as organizations expand, add staff, and rely more heavily on digital tools. This is why many companies are turning to outsourced IT support for growing businesses as a strategic solution...

Best B2C Payout Solutions for Global Businesses
As businesses expand globally, the way they send money to customers has become just as important as how they accept payments. Whether it’s a marketplace paying sellers, a fintech app distributing rewards, or a platform handling refunds and withdrawals, B2C payouts need to be fast, reliable, and easy to manage across borders. Relying on traditional...

Top Benefits of Vehicle Wraps for Walnut Creek Businesses
Vehicle wraps offer Walnut Creek businesses a high-impact way to build brand awareness without a massive monthly price tag. The top benefits include cost-effective local advertising, protection for your car’s paint, and a professional look that builds trust with customers. Unlike digital ads that disappear when you stop paying, a wrap works for you 24/7...

Expanding Into New Markets – How Businesses Should Handle SEO
Expanding into a new market changes how a business shows up in search in ways that are easy to underestimate. Geography adds a new element to how search engines interpret relevance, authority, and intent. What worked well in one region does not automatically carry the same weight in another. Search visibility becomes tied to location...
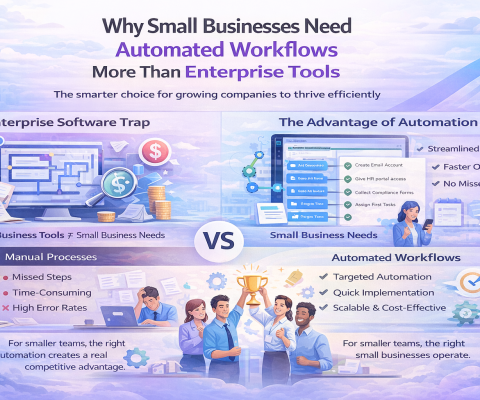
Why Small Businesses Need Automated Workflows More Than Enterprise Tools
There’s a pattern that repeats across growing companies. They hit a point where manual processes start breaking. Tasks get missed. Information lives in too many places. People spend more time coordinating than actually working. The instinct is to buy enterprise software. Big platforms with endless features that promise to solve everything. It rarely works out...

Why AI Apps Fail Without Strong UX and the Strategic Shift Business Leaders Must Make
AI adoption continues to accelerate across enterprises, yet a large share of AI-powered applications fail to reach sustained usage. Organizations invest heavily in AI app development, but many products struggle to justify the AI app development cost after launch. The issue rarely stems from weak models or infrastructure. It stems from poor UI UX design...

Why Local Businesses Should Invest in Digital Marketing
Local commerce runs on visibility, trust, and timing. When neighbors need a service, they reach for a phone, check a map listing, scan reviews, and compare a few websites before they call. Digital marketing turns those quick checks into steady inquiries by placing your business in the right place, with the right message, at the...

Top 7 AI Programs Business Professionals Should Consider in 2026
Artificial Intelligence continues to reshape how companies plan, execute, and scale. From decisions and forecasting to automation and customer experience, the skill gap is widening fast. If you are an executive, product owner, or mid-career technologist, the following programs emphasize practical, real-world application so you can translate AI talk into measurable business outcomes in 2026....

Cybersecurity Management for E-Commerce Businesses: A Complete Guide
As online shopping continues to expand, cybersecurity has become one of the most critical responsibilities for every e-commerce business. Whether you run a large digital storefront or a small boutique, protecting customer data and maintaining platform integrity are essential to long-term success. Modern cyber threats are sophisticated, and a single vulnerability can damage your reputation,...