Search Results
Showing results for "business" (3309 articles found)

AISURU/Kimwolf Botnet Launches Record-Setting 31.4 Tbps DDoS Attack
In the fast-evolving landscape of cybersecurity threats in 2026, Distributed Denial of Service (DDoS) attacks have escalated to unprecedented scales, disrupting global operations and costing enterprises billions. The recent assault by the AISURU/Kimwolf botnet, clocking in at a staggering 31.4 terabits per second (Tbps), marks the largest DDoS event on record, surpassing previous benchmarks like...

Claude Opus 4.6 Finds 500+ High-Severity Flaws Across Major Open-Source Libraries
In the fast-evolving landscape of 2026, where open-source software powers over 90% of enterprise applications, vulnerabilities in these foundational libraries pose existential threats to global cybersecurity. Enter Claude Opus 4.6, the latest iteration of Anthropic’s AI-driven code analysis tool, which has just uncovered more than 500 high-severity flaws across major open-source libraries like Apache Commons,...

Infy Hackers Resume Operations with New C2 Servers After Iran Internet Blackout Ends
In the ever-evolving landscape of cybersecurity threats in 2026, the resurgence of state-affiliated hacker groups like Infy underscores a critical vulnerability for global networks. As geopolitical tensions simmer, particularly in the Middle East, the end of Iran’s nationwide internet blackout—triggered by civil unrest in late 2025—has allowed these actors to reboot operations swiftly. This isn’t...

How Samsung Knox Helps Stop Your Network Security Breach
In the fast-evolving landscape of 2026, where cyber threats have surged by 45% year-over-year according to cybersecurity reports, network security breaches are no longer rare anomalies but daily battles for enterprises. With remote workforces expanding and IoT devices proliferating, a single vulnerability can cascade into multimillion-dollar losses. For network engineers, IT professionals, and business leaders,...

Compromised dYdX npm and PyPI Packages Deliver Wallet Stealers and RAT Malware
In the fast-evolving landscape of 2026, where decentralized finance (DeFi) platforms like dYdX handle billions in daily transactions, supply chain attacks on open-source repositories have surged as a top cybersecurity threat. Recent incidents reveal how attackers compromised npm and PyPI packages associated with dYdX, injecting wallet stealers and remote access trojans (RATs) that siphon cryptocurrency...
Understanding Divorce Proceedings: What to Expect When Marriage Ends
Divorce represents one of life’s most challenging transitions, affecting not just the couple involved but often children, extended family, and financial futures. Understanding the legal process can help individuals navigate this difficult period with greater confidence and clarity. The Legal Framework of Divorce Every state maintains its own divorce laws, creating significant variations in how...

Why Do Hardware Quality and Data Safety Define Modern Cloud Hosting?
Your server is the heartbeat of your operation. Whether you are running a critical database, a corporate VPN, or a high-traffic e-commerce site, downtime or data corruption is not just an inconvenience—it is a reputation killer. While the market is flooded with hosting offers, seasoned administrators know that the real value lies not in the...
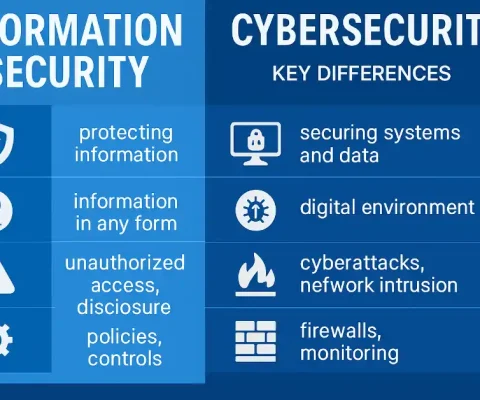
Common Gaps Between Security Policies and Real Threats
Security policies help define how organizations are expected to protect their systems and data. While these rules often reflect best practices and regulatory requirements, real attackers rarely behave as policies assume they do. They adapt quickly, exploit overlooked weaknesses, and take advantage of gaps between documented controls and real-world behavior. To better understand this gap,...

Malicious NGINX Configurations Enable Large-Scale Web Traffic Hijacking Campaign
In the rapidly evolving cybersecurity landscape of 2026, web traffic hijacking has emerged as a formidable threat, disrupting digital ecosystems and costing enterprises billions. As organizations increasingly rely on NGINX for its high-performance web serving capabilities—powering over 40% of the world’s busiest websites—a new wave of malicious configurations is enabling attackers to redirect traffic at...
Critical n8n Flaw CVE-2026-25049 Enables System Command Execution via Malicious Workflows
In the fast-evolving landscape of 2026, where automation tools are integral to enterprise operations, a critical vulnerability in n8n, the popular open-source workflow automation platform, has sent shockwaves through the cybersecurity community. Dubbed CVE-2026-25049, this flaw allows attackers to execute arbitrary system commands via malicious workflows, potentially compromising entire networks. With over 70% of enterprises...