Network Security

How to Implement Zero Trust Architecture: A Complete Guide
Discover a step-by-step approach to implementing Zero Trust Architecture, backed by stats and expert insights, to strengthen your cybersecurity defenses against modern threats.

Network Mastery in the Age of Digital Intelligence
In today’s interconnected world, networks are more than cables and routers—they are ecosystems of people, data, and digital identities. From cybersecurity specialists to business owners and IT administrators, everyone depends on reliable information to protect infrastructure and make informed decisions. However, one of the most overlooked elements of network security is identity verification. Suspicious emails,...

Adaptive Network Control: Guide to Dynamic Management in 2026
Explore adaptive network control's evolution, benefits, and 2026 trends for optimizing IT infrastructure with AI-driven efficiency and security insights.

Managed SOC Solutions: 4 Reasons for Real-Time Threat Protection in 2026
The cybersecurity landscape is evolving at an astonishing pace, driven by the relentless advances of technology and the innovative tactics of cyber adversaries. As a consequence, businesses need to be ever more vigilant and proactive in their security approach. Enter the managed SOC solutions, a robust way to counteract the myriad of threats that organisations...

SIEM Event Correlation: Detecting Complex Attacks Faster
Most security breaches don’t announce themselves. There’s no single moment where alarms blare and screens flash red. What actually happens is far quieter. A login attempt fails a few times. Someone accesses a file they don’t usually touch. An outbound connection goes somewhere slightly odd. Each of these events sits in a log somewhere, tagged as low severity, and gets ignored That’s exactly what attackers count on. Event correlation inside a SIEM platform is the mechanism that changes this dynamic. It’s how security teams stop looking at individual data points and...

Voice AI and Network Security: Protecting Real Estate Data in a Connected World
The Hidden Risks of Voice AI in Real Estate In the fast-paced world of real estate, where every client detail can clinch a deal, voice AI emerges as a quiet revolution. Picture an agent weaving through city traffic, fresh from a property showing. A quick spoken note captures the buyer’s thoughts—”loved the spacious kitchen, but...
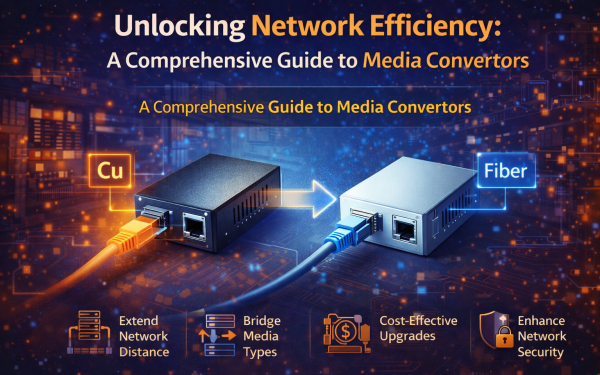
Unlocking Network Efficiency: A Comprehensive Guide to Media Convertors
In the realm of networking, efficiency and adaptability are paramount. One way to enhance both is through the use of a media convertor. These devices play a crucial role in the integration of various media formats within a single network infrastructure. Understanding Media Convertor Media convertors are devices that enable the conversion between different types...

Understanding the CIA Triad: Confidentiality, Integrity, and Availability
Every day, billions of pieces of data travel across networks worldwide—from personal emails and banking transactions to corporate secrets and government intelligence. But what keeps this information safe? What prevents hackers from reading your private messages, altering your bank balance, or shutting down critical systems? The answer lies in three fundamental principles that form the...

Master Cybersecurity Threats and Protections: Safeguarding Personal Records and Internet Services in 2025
In the realm of cybersecurity threats and protections, innovators develop cutting-edge tools and protocols, while visionaries craft long-term strategies to secure cyber domains like network infrastructure and cloud ecosystems. As a network engineer, I observe these experts leveraging data through secure binding techniques, such as encryption and API integrations, to counter cybersecurity threats and protections....

The Role of Market Research in Direct-to-Consumer Furniture Brands
The furniture industry has evolved dramatically as DTC (direct-to-consumer) brands have advanced on the scene and begun to flourish. DTC brands utilize digital platforms to directly sell to their consumers and have ultimately redefined the traditional retail furniture models, enhancing the consumer experience with improved convenience, transparency, and often more value. However, with progress comes...