In the rapidly evolving cybersecurity landscape of 2026, phishing attacks have surged to unprecedented levels, with encrypted messaging apps becoming prime vectors for sophisticated threats. German agencies, including the Federal Office for Information Security (BSI) and the Federal Intelligence Service (BND), have issued urgent warnings about a new wave of Signal phishing campaigns specifically targeting politicians, military personnel, and journalists. This trend matters now because it exploits the trust in secure platforms like Signal, which boasts over 100 million users globally, to infiltrate sensitive networks and extract classified data.
Why is this escalating in 2026? The rise coincides with heightened geopolitical tensions and the proliferation of hybrid warfare tactics. According to BSI reports, phishing incidents via encrypted apps have increased by 150% year-over-year, with Signal accounting for 40% of targeted attacks on high-value individuals. For network engineers, IT professionals, and business leaders, this isn’t just a distant threat—it’s a direct risk to enterprise security, as compromised personal devices can serve as entry points to corporate systems. Imagine a journalist’s Signal account being hijacked to spread disinformation or a politician’s chat logs exposing national secrets; the fallout could disrupt operations and erode trust in secure communications.
These attacks underscore the need for proactive defenses in an era where remote work and mobile-first strategies dominate. With 78% of organizations reporting at least one phishing-related breach in the past year, per global cybersecurity surveys, ignoring this could lead to costly downtime and regulatory penalties.
Understanding Signal Phishing Tactics
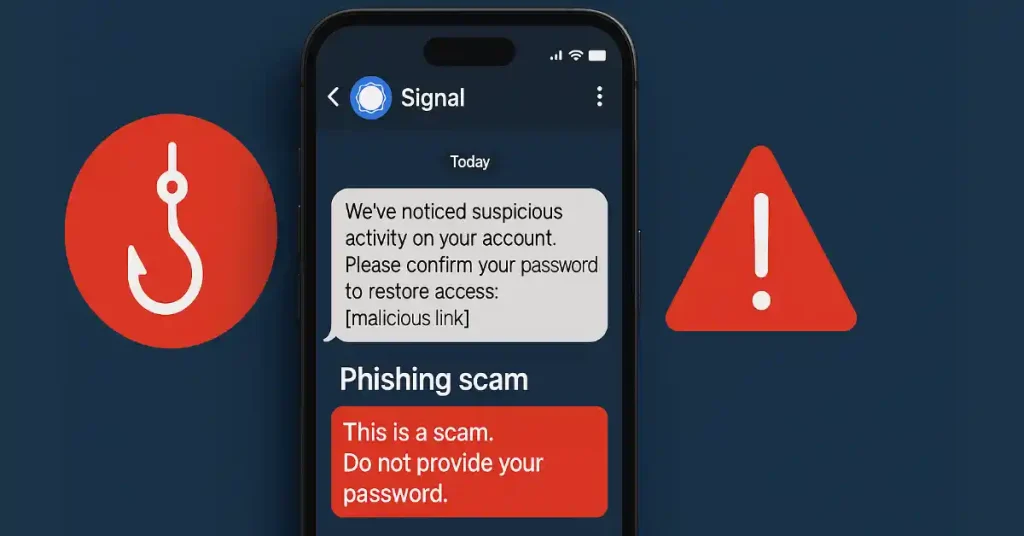
Signal phishing involves attackers impersonating trusted contacts on the Signal app to trick users into revealing credentials or installing malware. Unlike traditional email phishing, these campaigns leverage Signal’s end-to-end encryption to appear legitimate, often starting with a fake verification code or urgent message.
Real-world examples highlight the sophistication: In early 2026, a BND alert detailed how hackers posed as colleagues to German MPs, requesting “secure file shares” that deployed spyware. Metrics from cybersecurity firm CrowdStrike indicate that 65% of such attacks succeed due to social engineering, with an average data exfiltration of 500MB per incident.
- Key tactics: Use of deepfake voice notes or cloned profiles to build rapport.
- Technical indicators: Anomalous IP addresses or unexpected link domains.
- Detection tools: Integrate anomaly detection in network traffic, as discussed in our OpenClaw Integrates VirusTotal Scanning article.
High-Profile Targets and Broader Implications
Politicians, military officials, and journalists are prime targets because of their access to sensitive information. The BSI warns that these groups face a 200% higher risk compared to average users, with attacks often linked to state-sponsored actors from adversarial nations.
For instance, a recent case involved a European journalist whose Signal compromise led to leaked sources, amplifying disinformation campaigns. This ties into larger botnet threats, as explored in Who Benefited from the Aisuru and Kimwolf Botnets?. Enterprises must recognize that employee devices could bridge personal and professional vulnerabilities, potentially leading to ransomware demands averaging $1.7 million per incident.
Actionable insights include conducting regular vulnerability assessments and training on app-specific threats.
Mitigation Strategies for 2026
To counter Signal phishing, organizations should adopt multi-layered defenses. Start with enabling two-factor authentication (2FA) beyond app defaults and using enterprise-grade monitoring tools.
- Best practices: Deploy AI-driven phishing simulators for employee training, reducing success rates by 50%.
- Technical controls: Implement zero-trust architectures and app whitelisting.
- Patch management: Stay updated, as outlined in Patch Tuesday, January 2026 Edition.
For authoritative guidance, refer to the BSI’s official cybersecurity resources.
The Bottom Line
The warnings from German agencies highlight a critical shift in phishing tactics, impacting not just individuals but entire enterprises through supply chain risks. In 2026, with cyber threats projected to cost the global economy $10.5 trillion annually, professionals in networking and IT must prioritize encrypted app security to safeguard operations.
This trend demands immediate action: Audit your communication tools, train teams on emerging threats, and integrate advanced detection systems. By doing so, you can mitigate risks and maintain resilience against evolving attacks.
Ultimately, staying ahead requires vigilance—don’t let trusted apps become your weakest link. Implement these strategies today to protect your organization’s future.