Cybersecurity
Welcome to NetworkUstad’s Cybersecurity Hub – your comprehensive resource for staying secure in an increasingly connected world. In today’s digital landscape, cyber threats evolve faster than ever. From sophisticated ransomware attacks to simple phishing scams, businesses and individuals face constant risks. Our cybersecurity section delivers practical, actionable insights to help you build robust defenses and protect what matters most. Whether you’re a security professional, IT administrator, business owner, or someone concerned about digital privacy, you’ll find expert guidance covering everything from fundamental security principles to advanced threat protection strategies. What You’ll Discover: 🔐 Security Fundamentals – Master the CIA Triad, understand information security basics, and build a strong foundation in cybersecurity principles. 🛡️ Threat Intelligence – Learn about different attack vectors, hacker types, malware categories, and emerging cyber threats targeting organizations worldwide. 🔒 Protection Strategies – Explore practical defense mechanisms including encryption, multi-factor authentication, network security, endpoint protection, and access controls. 📊 Compliance & Governance – Navigate regulatory requirements like GDPR, HIPAA, PCI DSS, and industry frameworks such as NIST and ISO 27001. ⚡ Incident Response – Prepare for the inevitable with comprehensive guides on breach detection, containment, recovery, and forensic analysis. 🚀 Emerging Technologies – Stay ahead with insights on AI security, cloud protection, IoT vulnerabilities, blockchain security, and quantum computing threats. 💼 Enterprise Security – Discover strategies for securing hybrid workforces, protecting corporate data, managing third-party risks, and building security-aware cultures. 🎓 Career Development – Explore ethical hacking careers, certification paths (CEH, CISSP, OSCP), and skill development resources. Our articles combine technical depth with practical applicability. We break down complex security concepts into digestible insights, provide real-world examples, and offer step-by-step implementation guides. No unnecessary jargon—just clear, actionable cybersecurity knowledge you can use immediately. From understanding basic threats to implementing enterprise-grade security architectures, NetworkUstad’s cybersecurity content empowers you to make informed decisions and take meaningful action. We cover the full spectrum: network security, application security, data protection, cloud security, mobile security, and everything in between. Security isn’t a one-time project—it’s an ongoing journey. Join thousands of readers who trust NetworkUstad to keep them informed about the latest threats, best practices, and innovative solutions in cybersecurity. Protect your network. Secure your future. Start exploring our cybersecurity resources today.

The Role of Cybersecurity in Internet Protocols
As the digital world keeps changing, cybersecurity has become really important in making sure the internet works properly and safely. Just as we are concerned about the legitimacy of online security solutions, such as wondering Is Guardio legitimate?, it’s equally critical to understand the security measures ingrained in the very frameworks that facilitate our online...
The Security Features of Holo (HOT) and Why They Matter in the Age of Cyber Threats
The world of cryptocurrencies and blockchain technology is evolving at an unprecedented pace, and so is the threat of cyber attacks. In this age of cyber threats, security is of paramount importance, and Holo (HOT) is one such cryptocurrency that takes Security Features very seriously. In this article, we will explore the security features of...

Exploring Flutter’s Widget Catalog: A Guide for Developers
Want to know about Flutter’s Widget? Looking to dive deep into Flutter App Development? If so, then you are at the right place! This blog is surely worth reading if you want to learn about Flutter. Nowadays, we’re gonna talk about widgets in Flutter! By the end of this blog, you’ll have a comprehensive understanding...

Strengthening DNS Security Strategy against Ransomware Attacks
Ransomware attacks are a danger to businesses of all kinds in the linked digital world of today. These malicious assaults encrypt priceless data and demand a ransom in exchange for its decryption, resulting in monetary loss, reputational harm, and operational difficulties. Organizations must put strong security measures in place to reduce the danger of ransomware...

Moonbeam’s Approach to Security: A Detailed Review
At Moonbeam, we take security very seriously. We understand that security is paramount for our users, and we are committed to providing the highest level of security possible. In this article, we will provide a detailed review of our security approach, including the measures we take to protect your data and ensure the safety of...

A Step-by-Step Guide To Become A Cyber Security Architect:
Who is a Cyber Security Architect? A cyber security architect is a professional who designs and implements security solutions to protect an organization’s digital assets. They are responsible for analyzing the security risks and vulnerabilities, developing security frameworks, and creating strategies to mitigate potential cyber attacks. Cybersecurity architects typically have a strong background in information...
How to Integrate Fortinet with Your Systems
In today’s world, cybersecurity is a top priority for any business, big or small. Fortinet is a leading provider of cybersecurity solutions that help businesses protect their networks, devices, and data from cyber threats. Fortinet offers a wide range of products and services that cater to different cybersecurity needs, including firewall, VPN, antivirus, and more....

Advantages of security license plate recognition
Installing security cameras is the most effective method for monitoring your home, company, and workplace while you are absent. The purpose of security camera installation should always be to deter criminal activity and increase safety by preventing thefts, break-ins, and damage. The residential camera installation provides peace of mind knowing that your property is being...
Benefits of Using an IP Information Tool for Increasing Online Security
Do you worry about the safety of your online accounts? It’s not surprising that many people are looking at methods of digital identity protection in light of the rising number of cyber threats. An internet protocol information tool might be helpful in this endeavor. Using this technology, you can learn crucial information about your network...

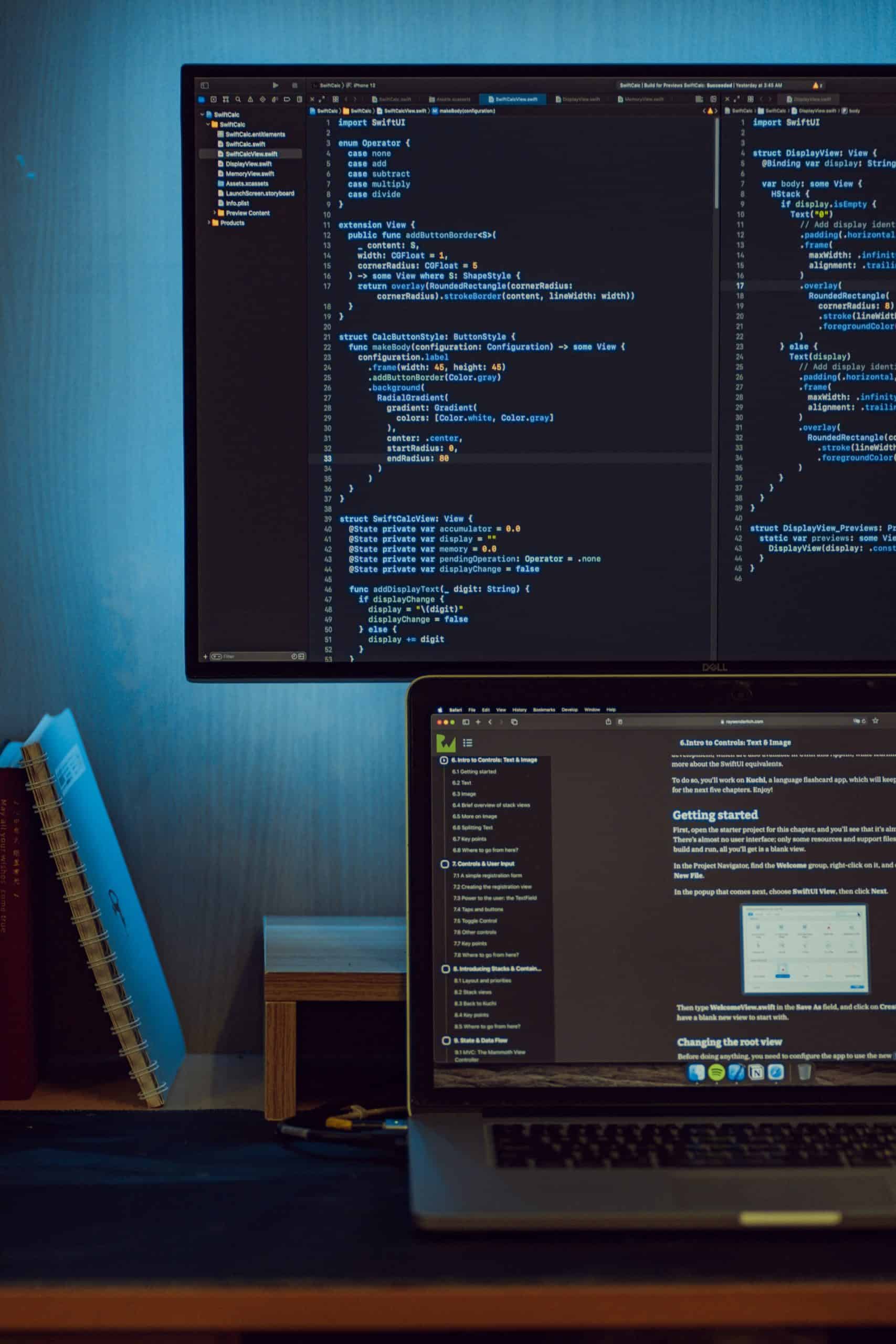
Best 5 Coding Platforms for Engineers
Engineers use coding platforms to develop, compile, and deploy applications. These platforms provide the tools necessary for engineers to create software, webpages, and other digital products. The platforms discussed in this article typically include support for multiple programming languages as well as additional resources such as text editors and debugging tools. With the right platform,...