
Cybersecurity
Network security, VPN guides, threat detection, and data breach prevention strategies.

The Digital Wild West: Taming Cybercrime And Law Enforcement
The digital world has transformed Cybercrime and Law Enforcement, but it has also given rise to a new type of crime: cybercrime. From hacking and identity theft to online fraud and cyberbullying, the internet has created a Wild West of criminal activity that threatens individuals and organizations. Law enforcement agencies worldwide are working tirelessly to...

Maximizing Mobile Device Security: Best Practices and Tips
Mobile Device Security, such as smartphones and tablets, have become integral to our daily lives. They provide convenient access to a vast amount of information and allow us to stay connected with the world around us. However, increasing reliance on mobile devices comes with an increased risk of security threats. Hackers and cybercriminals constantly find...
Web Security: A Comprehensive Guide
In today’s digital age, the internet is an integral part of our daily lives. We rely on it for communication, entertainment, information, etc. However, with the convenience of the web comes the risk of cyber threats. Hackers and malicious actors constantly seek ways to exploit vulnerabilities and gain unauthorized access to our personal and sensitive...

From Science Fiction to Reality: The Evolution of Service Robots
Introduction Service robots are intelligent machines designed to perform human tasks or services. They can be found in various industries and settings, including healthcare, military, transportation, and manufacturing. Service robots have been explored in science fiction literature and media for decades. Early depictions of service robots often depicted them as humanoid machines capable of performing...

Keep your Business safe from Cyber threats transmitted through email.
As a business owner, protecting your company from cyber threats transmitted through email is essential. Phishing assaults, malware, and ransomware are hazards that can jeopardize your company’s sensitive data, disrupt operations, and harm your reputation. You may dramatically lower the chance of a successful cyber-attack via email by adopting robust email security measures, teaching staff...

Android cleaners app for better performance of android devices
Android devices are some of the most popular and widely used gadgets today. But, just like your computer, they accumulate junk in fragmented files and other unnecessary data over time. This can slow down their performance and cause them to become sluggish. An Android cleaner app can help improve your device’s performance by removing these...

Here’s what you should look out for while selecting a data privacy suite.
Data privacy software is all the rage nowadays, and rightly so! As stricter and stricter data privacy laws and regulations are being implemented worldwide, it has become much more critical for businesses to comply with these regulations to carry out their operations effectively and efficiently. Now, it must be pointed out that several different data...
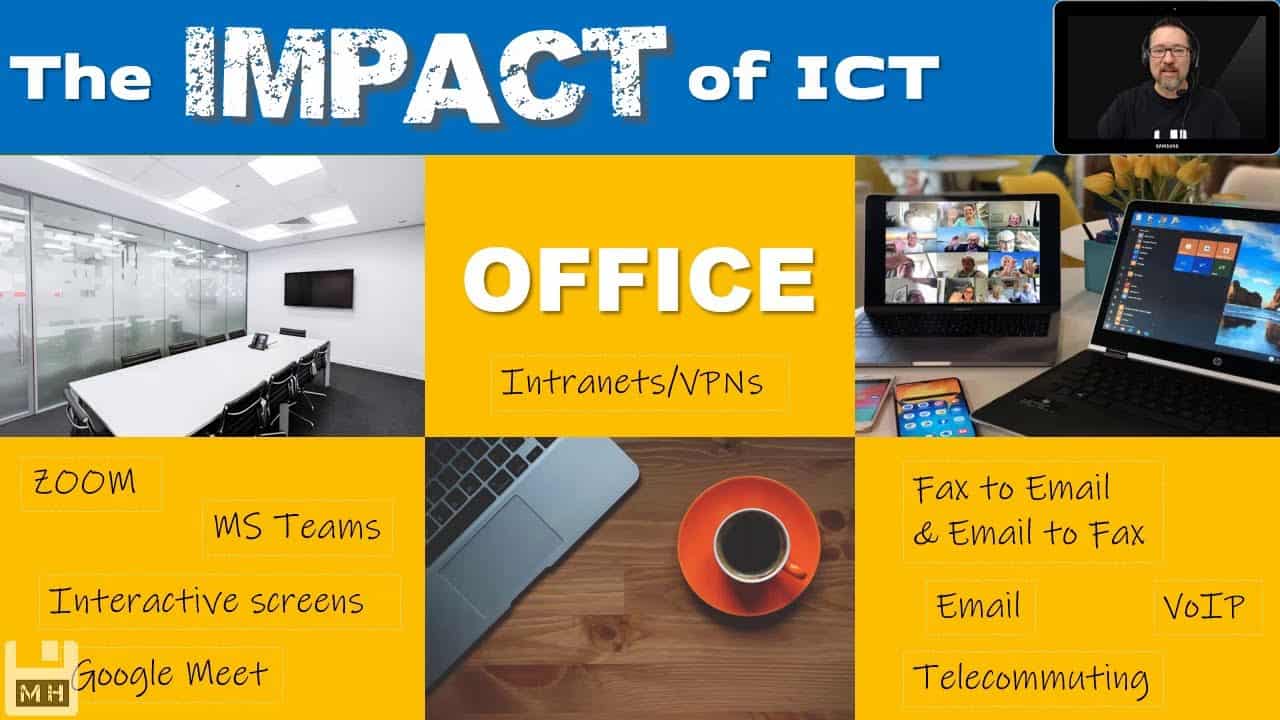
Top services provided by Impact ICT in Perth
Introduction Impact ICT is a leading IT services provider in Perth, Australia. Whether you’re looking for managed services or cloud solutions, Cyber Security providers in Perth can help you find the right technology solution to meet your needs. From remote working to cybersecurity and more, Impact ICT offers a wide range of services to help...

What Is Palo alto networks: Everything You Need to Know
Introduction to Palo Alto Networks Palo Alto Networks is a company that provides a platform for security and networking. The company was founded in 2005, and its headquarters are in Santa Clara, California. Palo Alto Networks has been profitable since 2012. In 2013, the company went public on the New York Stock Exchange. Palo Alto...

What is application security? Everything you need to know
Application security is the practice of protecting apps from unauthorized access and data breaches. It includes securing the app from external threats and safeguarding the data stored within it. Application security is important for businesses of all sizes. A data breach can result in lost customers, decreased revenue, and damage your reputation. There are many...