
Technology
AI, cloud computing, blockchain, and emerging technologies shaping the IT landscape.

6 Quantum-Proof Blockchain Infrastructure Providers for the Post-Quantum Era
Quantum computers threaten current encryption. We evaluated dozens of blockchain infrastructure providers for NIST compliance, integration ease, and performance, selecting the top 6 that are truly quantum-proof. These providers ensure your blockchain remains secure in the post-quantum era.

Why Facebook Runs BGP Everywhere — Even Inside Its Data Centers
An in-depth technical look at Facebook's network infrastructure, including routing protocols, open-source switching, and security architecture, with practical insights for network engineers.

A Look at the Top 5 Best Crypto Recovery Companies in 2026 for Fraud Investigation and Asset Tracing
As cryptocurrency fraud rises, specialized investigation firms help victims trace stolen assets. This review ranks the best crypto recovery companies in 2026 by forensic ability, compliance support, and victim assistance.

What is the best crypto payment provider in 2026?
There is no single best crypto payment provider in 2026—the right choice depends on a business's specific model. Criteria like deployment model, settlement, compliance, and coverage matter more than feature lists. Match provider to control needs, risk appetite, and branding for smooth operations.

How to Build Edge Network: Complete 2026 Guide
Master building edge networks with step-by-step instructions, case studies, and 2026 stats. Reduce latency by 60% and scale for IoT success.

Edge Computing vs Cloud 2026: Ultimate Comparison Guide
Discover edge computing vs cloud 2026 differences with stats, case studies, and trends. Optimize your infrastructure for low latency and scalability in hybrid models.
Why Networking Companies Need a Logo That Communicates Technical Reliability
Expert guide to logo design for networking and IT companies covering trust signals, color psychology, and vendor examples.

The Persistent Dominance of Petroleum in Transportation
An in-depth analysis of petroleum products and government policies in 2026, focusing on energy security, sustainability, and global trends.

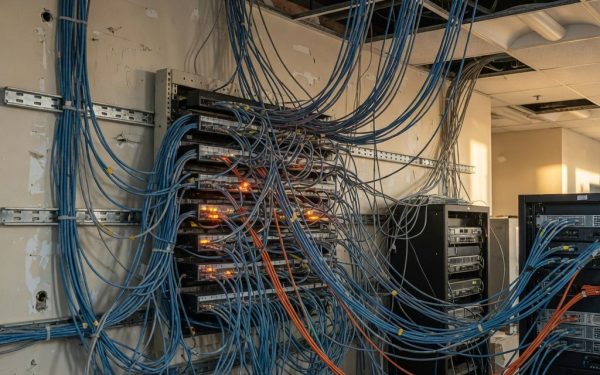
How Delay Metrics Dictate Traffic Flow in Modern Networks
Delay metrics determine traffic flow more than bandwidth in modern networks—here’s how to configure them correctly in 2026 environments.
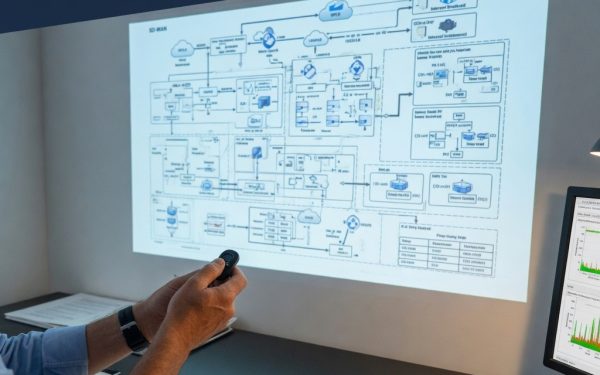
Why Hub-and-Spoke Topologies No Longer Serve Distributed Office Networks
A technical guide to office network architecture covering VLAN design, SD-WAN tradeoffs, ZTNA deployment, and QoS configuration for modern workspaces.