Cybersecurity

Anonymity and Identity Online: A Case Study of “Iamnobody89757”
Introduction The name “Iamnobody89757” has been seen all over the internet. People want to know what it means. This report will talk about “Iamnobody89757” in a fair way. It will look at where it came from, what it could mean, and how it has affected things. But it will also say if there is insufficient...

MeridianLink Data Breach: A Refined Analysis
MeridianLink is a big company. They helps banks and other money places with digital stuff. But on November 7th, bad people broke into their systems. These bad people are called ALPHV/BlackCat group. They used ransomware to get into MeridianLink’s computers. Ransomware is a form of malware that locks up data. The bad guys might have...

Building Blocks of Cybersecurity: Why IT Infrastructure Security Matters
The Importance of IT Infrastructure Security You know how important it is to keep your physical home secure, right? You lock your doors and windows, maybe even have an alarm system. Well, the same goes for your digital home. Your IT infrastructure security is just as crucial to protect. After all, it houses everything from...
The Role of Payment Facilitators in Enhancing Cybersecurity for Online Transactions
Online transactions have become a cornerstone of our daily activities in the fast-paced digital world. However, with this convenience comes the increased risk of cyber threats. As more consumers and businesses engage in digital commerce, the importance of cybersecurity in online transactions has escalated significantly. This is where Payment Facilitators (PayFacs) play a crucial role....
Top Cybersecurity Threats and Trends In 2024
As we move into the ever-evolving landscape of 2024, the digital realm remains a battleground for cyber threats that are constantly evolving in complexity and sophistication. Organizations and individuals must stay ahead of the curve to protect themselves from emerging dangers. In this blog post, with Vitaliy Klymenko, Editor-in-Chief in Slotamia and cybersecurity specialist, we...

Can AI Solve Current Challenges in FinTech Cybersecurity?
The fast evolution of financial technology (FinTech) has undoubtedly revolutionized and streamlined financial processes. From seamless transactions to personalized financial advice, it provides consumers and businesses with convenience and accessibility. However, it doesn’t come without challenges, and perhaps the most pressing among them is the escalating concern surrounding cybersecurity. The more financial systems digitize and...
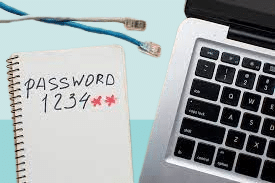
Mystery of SLAM in Cybersecurity
Maintaining a proactive defense against malicious actors is imperative in the rapidly evolving realm of cybersecurity. One term frequently surfacing in discussions about bolstering cybersecurity strategies is SLAM – a formidable tool within the cybersecurity arsenal. In this article, we’ll unravel the complexities of SLAM, exploring its pivotal role in reinforcing digital defenses and elucidating...

Navigating the Cybersecurity Universe with Parrot Security OS
In today’s fast-paced digital era, the cyber world is a realm fraught with danger and opportunity. As technology leaps forward, the threats to our digital lives grow in parallel. In this evolving digital landscape, your choice of operating system becomes paramount. Enter Parrot Security OS, the intrepid knight of the digital realm. In this engaging...

Kali Linux Unveiled: The Ultimate Cybersecurity Superhero
Picture a world where cybersecurity is a battlefield, and hackers and defenders wage a constant war. In this digital arena, one name reigns supreme as the ultimate ally for the good guys – Kali Linux. So, what’s the deal with Kali Linux, and why is it the hottest superhero in the cybersecurity universe? Hold on...

Cutting Edge AI Threat Detection Technology Transforming Cybersecurity
It is critical to stay ahead of the curve in the current digital AI and Machine Learning in Security landscape, as cyber threats are evolving at an alarming rate. “Advanced AI Threat Detection Solutions” are leading the cybersecurity revolution. This article examines how advanced AI and machine learning methods change threat detection and provides professional...