encrypted communication
Telnet vs. SSH: A Comprehensive Comparison of Remote Access Protocols 2025
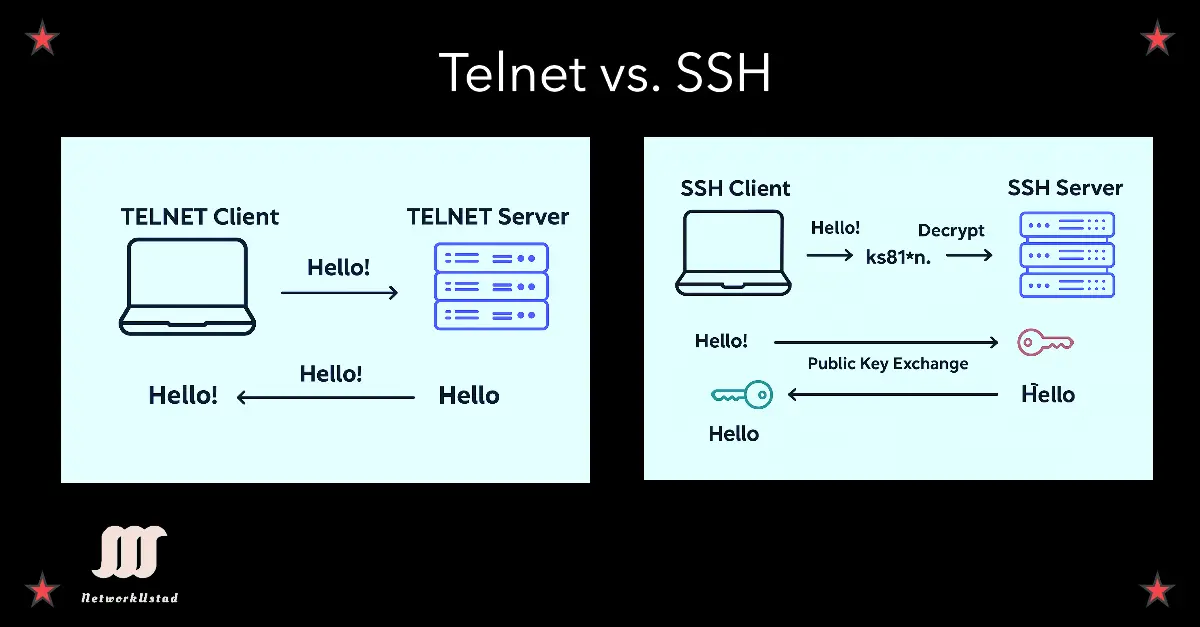
This article explores Telnet vs. SSH, two protocols for remote access to devices and systems, comparing their security, functionality, and modern relevance. Whether you’re managing network devices, debugging services, or securing remote connections, understanding these protocols is essential. Use the table of contents below to navigate to specific sections. Telnet Protocol Overview Telnet is a...

CRPF VPN Login Exclusive: Secure Access for Central Reserve Police Force Personnel (Updated 2025)
In today’s digital era (September 21, 2025), cybersecurity is paramount for India’s Central Reserve Police Force (CRPF), tasked with VIP protection, anti-insurgency operations, and Left-Wing Extremism (LWE) containment. As the official site states, the CRPF’s mission is to “empower the government to maintain the rule of Law, Public Order, and Internal Security” through proactive training...