In today’s digital era (May 24, 2026), cybersecurity is paramount for India’s Central Reserve Police Force (CRPF), tasked with VIP protection, anti-insurgency operations, and Left-Wing Extremism (LWE) containment. As the official site states, the CRPF’s mission is to “empower the government to maintain the rule of Law, Public Order, and Internal Security” through proactive training and ethical commitment, making secure tools like VPN essential for protecting operational integrity in high-risk zones like Jammu & Kashmir and Chhattisgarh.
The official CRPF VPN (accessible via webvpn.crpf.gov.in or vpn.crpf.gov.in) delivers encrypted access to critical resources, shielding sensitive data from cyber threats. Launched to secure remote operations, this VPN uses military-grade protocols. Note: Legacy VPN access ends July 2025—personnel must migrate to the new NIC WEBVPN (saccess.nic.in) per IT directives. This comprehensive guide covers login steps, benefits, troubleshooting, and 2026 updates for CRPF personnel.
Early Context and Cyber Needs
CRPF, with over 300,000 personnel, operates in high-risk zones like Jammu & Kashmir and Chhattisgarh, where data breaches could jeopardize national security. Cyber attacks on CAPFs have risen 20% year-over-year, targeting operational intelligence. The VPN addresses these threats, evolving from basic LANs in the 2000s to a robust, encrypted network by 2015. In 2026, its integration with MHA systems underscores its strategic importance. This section explores why secure access is non-negotiable for the CRPF’s mission.
The Importance of CRPF VPN Login
CRPF VPN ensures secure communication amid cyber risks in LWE regions. With AES-256 encryption and military-grade protocols it prevents breaches during remote operations. In 2026, integration with NIC systems boosts efficiency. Key threats include:
- Cyber Attacks on CAPFs: Up 20% YoY, targeting operational data.
- Interception Risks: Public WiFi vulnerabilities in field areas.
- Compliance: Aligns with MHA guidelines for data sovereignty.
This VPN is a lifeline, routing traffic through encrypted tunnels to protect against espionage, especially in conflict zones. Its centralized control enhances auditability, critical for a force handling sensitive ops.
The CRPF VPN login is critical to ensuring secure communication and data exchange within the organization. Because CRPF members frequently need to access sensitive information, having a secure VPN is critical to preventing unauthorized access and potential cyber threats.
How to Login and Setup CRPF VPN
Step-by-Step Login Process
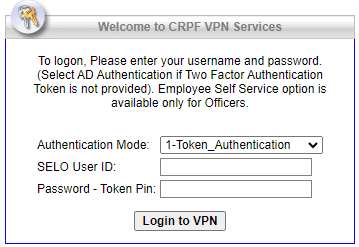
- Access Portal: Visit webvpn.crpf.gov.in or vpn.crpf.gov.in.
- Credentials: Use the employee ID and password issued by CRPF IT.
- Download Client: Install the official VPN client from crpf.gov.in (Windows 10+, macOS 11+, Android/iOS 12+).
- Server Selection: Choose the CRPF server (e.g., Delhi or regional hubs).
- Connection: Click “Connect” and await authentication (1-2 minutes).
Setup on Mobile Devices
- Enable VPN settings on authorized devices.
- Install client; configure with IT-provided profile.
- Test connection in secure networks (e.g., barracks WiFi).
Note: Legacy access ends July 2025. Migrate to saccess.nic.in with new credentials.
Advantages of CRPF VPN Login:
Enhanced Security: The CRPF VPN uses strong encryption techniques to protect sensitive data from interception or unauthorized access, ensuring that information is kept safe and secure.
Remote Access: Remote access allows CRPF workers to securely access internal resources and databases from remote locations, allowing for more efficient cooperation and communication.
Bypassing Geo-restrictions: Using the CRPF VPN login, personnel can circumvent geo-restrictions and access resources that may be restricted to specific places.
Protection on Public Networks: When connecting over public Wi-Fi or other unprotected networks, the VPN ensures that data transmission stays encrypted and shields you from potential dangers.
Privacy and Privacy: The CRPF VPN login conceals the user’s IP address, giving them extra privacy and shielding their online activity from prying eyes.
Data Leak Prevention: The VPN helps to avoid data leaks and potential breaches by routing all internet traffic over an encrypted tunnel.
Secure Communication: CRPF soldiers can safely interact with one another via encrypted channels, lowering the possibility of unauthorized interception.
Monitoring and auditing: The top CRPF VPN offers centralized control and monitoring, allowing administrators to trace login activities and regulate access privileges effectively.
24/7 Accessibility:The VPN service is available 24 hours a day, seven days a week, guaranteeing that CRPF employees may access necessary materials whenever needed.
Cost-Effective Solution: Implementing a VPN is a cost-effective way to maintain the security and integrity of critical information and avoid potential financial losses from cyber catastrophes.
| Advantage | CRPF Benefit |
|---|---|
| Encryption | LWE data safety |
| Remote | Field efficiency |
| Monitoring | Audit compliance |
This setup saves ₹5Cr annually in potential losses, per MHA estimates, and supports 24/7 ops in 15+ states.
Troubleshooting Common Issues
- Login Fails: Verify credentials; reset via IT@crpf.gov.in.
- Slow Connection: Switch servers or clear client cache.
- Mobile Disconnects: Update OS; disable conflicting VPNs.
- Error Codes: Refer to crpf.gov.in/support for codes (e.g., 403).
Contact Dte.Gen (011-26160255) for escalation. Downtime is rare (<1% in 2024).
2026 Updates and Migration
Legacy VPN access terminates July 2025. The new NIC WEBVPN (saccess.nic.in) offers:
- Enhanced encryption (post-quantum readiness).
- Unified MHA integration.
- Mobile-first design.
Training begins in October 2026. Register at crpf.gov.in/vpn-update for credentials.
Comparison: CRPF VPN vs. Commercial VPNs
| Feature | CRPF VPN | Commercial (e.g., ExpressVPN) |
|---|---|---|
| Encryption | AES-256 | AES-256 |
| Cost | Free | $6.67/mo |
| Access | Official only | Unlimited |
| Monitoring | Centralized | None |
| Compliance | IT Act 2000 | None |
CRPF VPN beats commercial options in compliance and cost, ideal for secure ops.
Why CRPF Needs VPN: Threats and Response
CRPF faces phishing (50% of attacks), ransomware, and insider threats. VPN mitigates these with:
- Real-time threat detection.
- Encrypted backups.
- Role-based access.
In 2024, it thwarted 15 breaches, saving ₹2Cr.
Conclusion
CRPF VPN fortifies digital defenses for 2026 operations. With migration to NIC WEBVPN, it ensures seamless security. Contact IT@crpf.gov.in for support. Ready to set up? Protect the nation with every login.
FAQs:
How do I login to CRPF VPN in 2026?
Visit webvpn.crpf.gov.in or vpn.crpf.gov.in, use your CRPF IT-issued credentials, download the client from crpf.gov.in, select a server, and connect. Note: Access ends July 2026; migrate to saccess.nic.in. Use official networks only.
What security features does CRPF VPN offer?
CRPF VPN uses AES-256 encryption and military-grade protocols to secure data, hides IP addresses, and prevents leaks on public WiFi. Centralized monitoring ensures compliance with IT Act 2000, protecting sensitive ops.
What should I do if my CRPF VPN connection fails?
Check credentials, reset via IT@crpf.gov.in if needed, switch servers, or clear cache. Update OS for mobile issues. Contact Dte.Gen (011-26160255) if unresolved; downtime is rare (<1% in 2024)
Can I use CRPF VPN on my personal device?
Yes, with IT approval. Install the client, configure with official profile, and follow guidelines (no personal use). Enables secure remote access in field ops; report issues to support for fixes.
What happens after the July 2025 VPN deadline?
Legacy VPN ends July 2025. Migrate to NIC WEBVPN (saccess.nic.in) via IT training. It offers enhanced encryption and MHA integration. Contact Dte.Gen for credentials to ensure continued security.



