zero-trust architecture

Master Cybersecurity Threats and Protections: Safeguarding Personal Records and Internet Services in 2025
In the realm of cybersecurity threats and protections, innovators develop cutting-edge tools and protocols, while visionaries craft long-term strategies to secure cyber domains like network infrastructure and cloud ecosystems. As a network engineer, I observe these experts leveraging data through secure binding techniques, such as encryption and API integrations, to counter cybersecurity threats and protections....
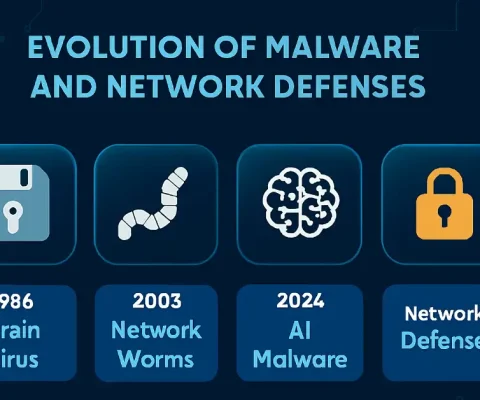
What is Malware and Malicious Software? (Updated 2025)
Updated: October 19, 2025—Includes latest threats and network defenses. Malware, or malicious software, is a program or file designed to disturb computer processes and operations or gain unauthorized entry to the computer system, often via network protocols like RDP or SMB, without the user’s knowledge or permission. Malware has become a common term for all...