Updated: October 19, 2025—Includes latest threats and network defenses. Malware, or malicious software, is a program or file designed to disturb computer processes and operations or gain unauthorized entry to the computer system, often via network protocols like RDP or SMB, without the user’s knowledge or permission. Malware has become a common term for all hostile or intrusive software, computer viruses, worms, Trojan horses, ransomware, spyware, adware, scareware, and other malicious programs.
The above-mentioned malware and malicious software programs can perform a variety of functions, including stealing, encrypting, or deleting sensitive data, altering or hijacking core computing functions, and monitoring users’ computer activity without their permission. Cybercriminals target users’ end devices through the installation of malware.
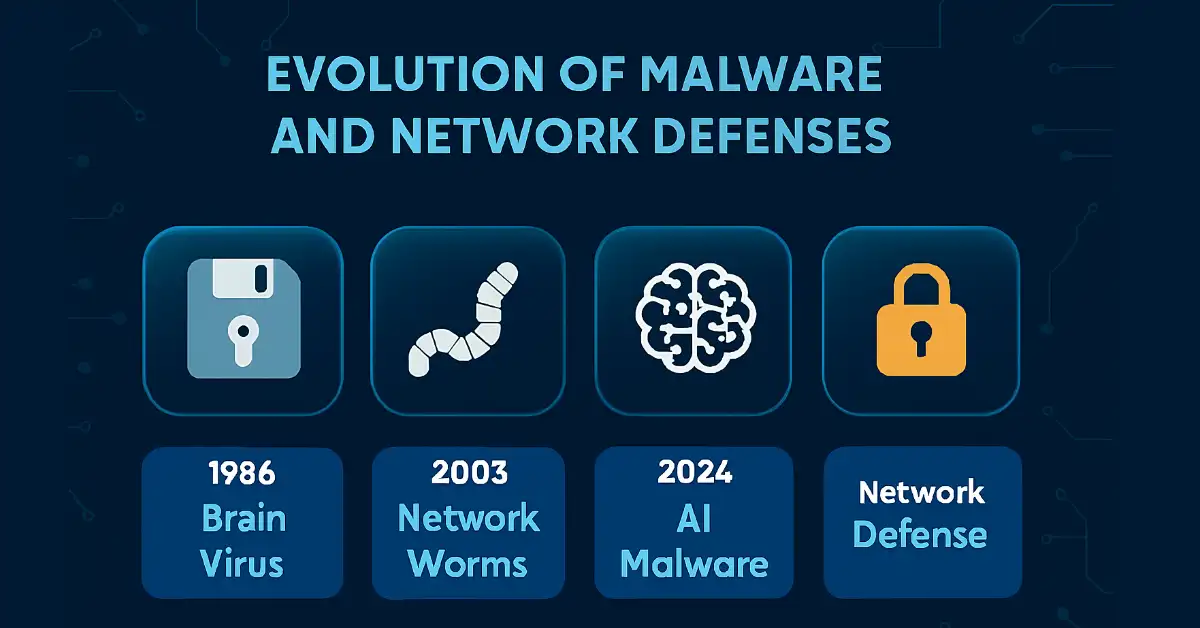
Evolution of Malware: A Network Perspective
Malware has evolved from simple file-based infections to sophisticated network-exploiting threats. Understanding this progression helps network engineers design resilient architectures.
| Year | Malware Type | Network Impact |
|---|---|---|
| 1986 | Brain Virus | Spread via floppy disks; minimal network. |
| 2001 | Code Red | Exploited IIS servers, caused DDoS-like slowdowns. |
| 2017 | WannaCry | SMB worm; global network disruption. |
| 2024 | Recent AI-driven malware | Uses ML to evade network detection. |
Viruses
A virus is an executable code attached to another executable file. Most viruses require end-user initiation and can start at a particular time or date. They generally spread in one of three ways.
- Removable media
- Downloads off the Internet
- Email attachments
Detecting a virus is not easy. The viruses can be harmless and just show a picture, or they can be destructive, such as those that change or delete data. To avoid detection, a virus changes itself into other shapes. A simple process of opening a file can trigger a virus.
While USB drives remain a vector, modern viruses often spread via network file shares exploiting protocols like SMB (e.g., EternalBlue vulnerability). A boot sector, file system, virus, or infected USB drives can reach the system’s hard disk. Executing a specific program can activate a virus program. Once the virus program is active, it will infect other computer programs or computers on the network.
Spyware
Spyware monitors network activity, keylogging credentials sent over HTTP. Defend with encrypted protocols (HTTPS).
Adware
Adware injects ads via browser hijacks, consuming bandwidth. Network fix: DNS filtering.
Scareware
Scareware fakes alerts to trick users into downloading more malware, often via malicious sites.
Worms
Worms are also malicious code, just like viruses. Worms replicate by separately exploiting vulnerabilities in networks. This generally slows down the networks. The worms run independently.
Once a worm affects a host, it spreads very quickly over the network. Worms share the same patterns. They all have an activating vulnerability, a way to spread themselves, and a payload.
Worms are responsible for some of the most devastating attacks on the Internet. For example, in 2001, the Code Red worm infected around 359,000 hosts in just 14 hours. More recently, the WannaCry worm (2017) exploited SMB vulnerabilities, affecting over 200,000 computers worldwide and causing network outages in hospitals and factories.
Logic Bombs
A logic bomb is malicious software that uses a trigger to activate the malicious code in the operating system. Different types of triggers exist, such as dates, times, other programs running, or deleting a user account. The logic bomb remains inactive until a trigger event occurs.
Once the logic bomb is activated, it performs different functions, such as corrupting or altering data, reformatting a hard drive, and deleting important files. Recent examples include the AcidRain wiper (2022), which targeted satellite modems, potentially triggering hardware failures in networked devices.
Ransomware
Ransomware restricts access to the user’s computer and files. It is a type of malware that displays a message and demands payment to remove the restriction from computers and files. It usually encrypts data in the computer with a key unknown to the user. The user must pay criminals to remove the restriction.
Some versions of ransomware use system vulnerabilities to lock down the system. The most common type of ransomware infection is an email containing a malicious attachment or a pop-up advertisement. Some ransomware propagates as a Trojan horse. Once the victim pays, the criminal sends a program that decrypts the data and files or sends an unlock code.
In 2023, LockBit ransomware targeted networks via phishing, exfiltrating data over encrypted channels before encryption, highlighting the need for network traffic monitoring.
Fileless Malware
Fileless malware lives in memory, evading disk scans. It spreads via PowerShell over networks. Detect with endpoint detection and response (EDR) tools monitoring network calls.
Backdoors and Rootkits
A backdoor is a method of accessing a computer without going through the normal access process, such as entering a name and password. It bypasses the normal authentication used to access a system. The Netbus and Back Orifice are examples of backdoor programs that allow unauthorized system users to access remotely.
The backdoor grants future access to cyber criminals even if the association fixes the original vulnerability used to attack the system. Generally, criminals have authorized users to innocently run a Trojan horse program on their machine to install the fbackdoor.
A rootkit is used to mask program files to help hackers avoid detection. It is also used to open a backdoor, allowing hackers to access a system without authentication remotely. Usually, rootkits use software vulnerabilities to perform privilege escalation and modify system files.
Rootkits modify system forensics and monitoring tools, making them very hard to detect. Generally, a user should wipe and reinstall the operating system of the infected computer with the rootkit. Modern examples include the SolarWinds Orion backdoor (2020), which compromised supply chains and allowed persistent network access.
Defending Against Malware and Malicious Software
- Antivirus Program – Most antivirus programs catch many forms of malware. However, criminals develop and set up new threats daily. Thus, keeping antivirus signatures updated is the key to a successful solution.
- Up-to-date Software –Many types of malware reach their goal by exploiting operating system and application software vulnerabilities. Earlier, operating system vulnerabilities were the primary source of problems, but now, application-level vulnerabilities create the most significant risk. Operating system vendors are more responsive to patching and updating the system. However, many application vendors lag in patching, so network engineers recommend implementing zero-trust architectures to limit lateral movement.
- Network Segmentation: Use VLANs to limit worm spread.
- Behavioral Analysis: Tools like Suricata for anomaly detection.
- Backups: Off-network air-gapped storage.
- User Training: Simulate phishing on internal networks.
- Multi-Factor Authentication: Prevents backdoor exploitation.
Case Studies in Malware Attacks
- NotPetya (2017): Masqueraded as ransomware but wiped data; spread via EternalBlue, highlighting unpatched networks.
References: NIST Cybersecurity Framework, etc.
FAQs
What is the difference between a virus and a worm?
A virus needs user action to spread, like opening a file, while a worm self-propagates over networks via vulnerabilities, slowing down systems.
How does ransomware impact networks?
Ransomware encrypts files and demands payment, often exfiltrating data over networks, as seen in LockBit 2023. Use IDS/IPS and backups to mitigate.
Can logic bombs damage hardware?
Yes, logic bombs like AcidRain (2022) can overheat components by disabling cooling systems in networked devices, causing hardware failure.
What is fileless malware and how to detect it?
Fileless malware runs in memory, evading disk scans, and spreads via PowerShell. Use EDR tools to monitor network calls for detection.
How can network engineers defend against backdoors?
Backdoors bypass authentication, enabling remote access. Use MFA, zero-trust models, and monitor SSH/RDP traffic to prevent exploitation.