Asad Ijaz
NetworkUstad's lead networking architect with CCIE certification. Specializes in CCNA exam preparation and enterprise network design. Authored 2,800+ technical guides on Cisco systems, BGP routing, and network security protocols since 2018. Picture this: I'm not just someone who writes about tech; I'm a certified expert in the field. I proudly hold the titles of Cisco Certified Network Professional (CCNP) and Cisco Certified Network Associate (CCNA). So, when I talk about networking, I'm not just whistling in the dark; I know my stuff! My website is like a treasure trove of knowledge. You'll find a plethora of articles and tutorials covering a wide range of topics related to networking and cybersecurity. It's not just a website; it's a learning hub for anyone who's eager to dive into the world of bits, bytes, and secure connections. And here's a fun fact: I'm not a lone wolf in this journey. I'm a proud member and Editor of Team NetworkUstad. Together, we're on a mission to empower people with the knowledge they need to navigate the digital landscape safely and effectively. So, if you're ready to embark on a tech-savvy adventure, stick around with me, Asad Ijaz Khattak. We're going to unravel the mysteries of technology, one article at a time!"

Your Digital Safety Net: What Every Setup Should Include
What’s the first thing you do when your Wi-Fi goes down in the middle of a video call? Panic? Restart the router? Blame the cat for stepping on something? In a world where nearly everything runs through a screen, losing your connection feels like losing control. And it’s not just about convenience anymore. From schoolwork...
When Authentication Turns Against You: Protecting Kerberos from Abuse
Many organizations depend on Kerberos every day to keep their systems secure. It’s built into most Windows environments and handles authentication for thousands of users and services. But the same mechanism that keeps networks safe can also be turned against them. Attackers have learned to exploit Kerberos in ways that give them deep, long-term access...

Mastering Crypto Prop Trading: Proven Strategies and Firm Comparisons for 2025 Success
In the rapidly evolving cryptocurrency markets, proprietary trading (prop trading) has become an increasingly popular path to substantial profits for skilled traders. Unlike traditional retail trading, prop trading allows selected traders to leverage the capital of respected firms, enabling greater buying power and risk capacity. However, succeeding in crypto prop trading requires a robust command...
Lumpsum calculator explained: A practical tool for smarter investment decisions
Every investor, at some point, wonders how their money will grow if invested all at once instead of through smaller monthly contributions. So, if you’ve just received a bonus, sold an asset, or saved over time, a one-time investment can be a powerful wealth-building move. But before you put that amount into the market, you’ll...
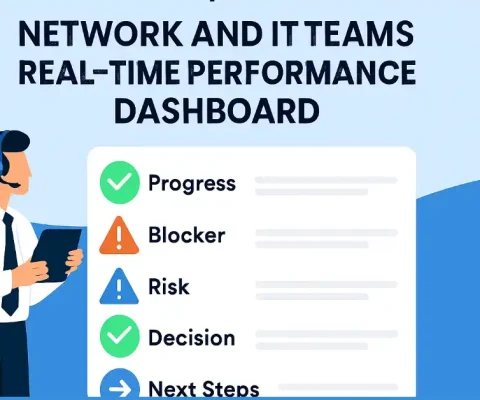
Why Every Network and IT Team Needs a Real-Time Team Performance Dashboard
If you have ever been the unlucky soul who gets pinged at 2:03 a.m. with a mysterious service issue that “only happens in production,” you already know the truth: network and IT teams do not suffer from a lack of data, they suffer from a lack of signal. Updates live in Slack threads, decisions hide...
Why Businesses Are Turning to AI-Powered Security Systems
In a world where technology evolves faster than ever, security has become smarter, faster, and more proactive. Gone are the days when a simple CCTV camera or motion sensor was enough to safeguard assets and people. Today’s businesses are shifting to AI-powered security systems — solutions that don’t just record, but think, analyze, and act...

The Role of Cybersecurity in Closing B2B SaaS Contracts
Why security decides B2B SaaS deals in 2025 Enterprise buyers are risk managers as much as technologists. They carry obligations to protect regulated data, answer to auditors, and keep systems online. If your team cannot satisfy a security questionnaire, provide recent independent test results, or show clear policies, the deal stalls or shrinks. When you...

Claude and ChatGPT 10x My Agency — From $2K to $24K Monthly in 16 Weeks
The Software Duo That Turned My Failing Agency into a $24K Machine Marcus opened his dashboard. $24,180 for November. In July, he was ready to quit at $2,400. The agency was dying. Bad clients, bad margins, bad everything. Then Claude and ChatGPT — two Language Models operating as Software business transformers — took over operations....

Tool Tracker Software: Streamlining Daily Operations
In today’s business environment, efficiency remains a top priority. Companies consistently strive to enhance efficiency by streamlining daily tasks. If you’re trying to get this job done right, tool tracking software gives you a powerful assist. Keep tabs on your equipment. This not only streamlines daily operations but also helps prevent overspending. Imagine fewer lost...

Fast & Secure Linux VPS: Boost Speed and Growth in 2025
In the digital world today, how well you do online can say a lot about your business growth. No matter if you have websites, web apps, or use tools in the cloud, speed and trust matter for the user’s time. A fast and safe VPS (Virtual Private Server) gives you a better way to get...