Asad Ijaz
NetworkUstad's lead networking architect with CCIE certification. Specializes in CCNA exam preparation and enterprise network design. Authored 2,800+ technical guides on Cisco systems, BGP routing, and network security protocols since 2018. Picture this: I'm not just someone who writes about tech; I'm a certified expert in the field. I proudly hold the titles of Cisco Certified Network Professional (CCNP) and Cisco Certified Network Associate (CCNA). So, when I talk about networking, I'm not just whistling in the dark; I know my stuff! My website is like a treasure trove of knowledge. You'll find a plethora of articles and tutorials covering a wide range of topics related to networking and cybersecurity. It's not just a website; it's a learning hub for anyone who's eager to dive into the world of bits, bytes, and secure connections. And here's a fun fact: I'm not a lone wolf in this journey. I'm a proud member and Editor of Team NetworkUstad. Together, we're on a mission to empower people with the knowledge they need to navigate the digital landscape safely and effectively. So, if you're ready to embark on a tech-savvy adventure, stick around with me, Asad Ijaz Khattak. We're going to unravel the mysteries of technology, one article at a time!"

What Great Hybrid Offices Have That Average Ones Miss in 2025
In the hybrid working age, organisations across all sectors are reconsidering how their physical premises can facilitate productivity, flexibility, and employee well-being. While it is true that many companies have adjusted to this new working world with varying success, their offices are divided between those that make it work and those that genuinely enable hybrid...

Beating the Hackers: Top Cybersecurity Innovations to Secure Your Business in 2025
As a cybersecurity expert with over 10 years in the trenches—defending everything from Fortune 500 networks to critical infrastructure—I’ve seen hackers evolve from script kiddies to state-sponsored maestros of digital chaos. But in 2025, the tide is turning. Cyber threats are more insidious than ever, with ransomware payouts dipping to $813.55 million in 2024, yet...

Virtual Try-On Help You Pick the Perfect Watch?
Finding the perfect watch has traditionally meant visiting multiple stores, trying on different models, and spending hours comparing styles. Today, virtual try-on watches powered by AI watch try-on and AR watch try-on tools are transforming the process. With a smartphone or computer, shoppers can now see how a timepiece looks on their wrist in real...

The Ultimate Guide to Buying a USA eSIM
The way we stay connected has evolved — and eSIM technology is leading the charge. Whether you’re a tourist exploring New York, a digital nomad in San Francisco, or a local switching carriers, this ultimate guide to buying a USA eSIM in 2025 gives you everything: compatibility, top providers, activation steps, coverage maps, and cost...

The Marathon OSAR-D: A Watch Forged for the Harshest Frontiers
When the environment turns unforgiving, gear becomes more than equipment — it becomes survival. This principle has guided Marathon Watch for decades, and it is exemplified in one of their most rugged and purpose-built models: the Marathon OSAR-D. Designed with Arctic search and rescue conditions in mind, the OSAR-D embodies durability, precision, and a level of trustworthiness that...

Affordable Software Development Solutions: A Smart Choice for Businesses in 2025
Today’s fast paced digital world businesses off all sizes are looking for ways to innovative without overspending from startups launching their first app to established companies upgrading their system affordable software development solutions are making it possible to achieve big goal without breaking the bank, the right approach combines cost effectiveness with quality ensuring that...
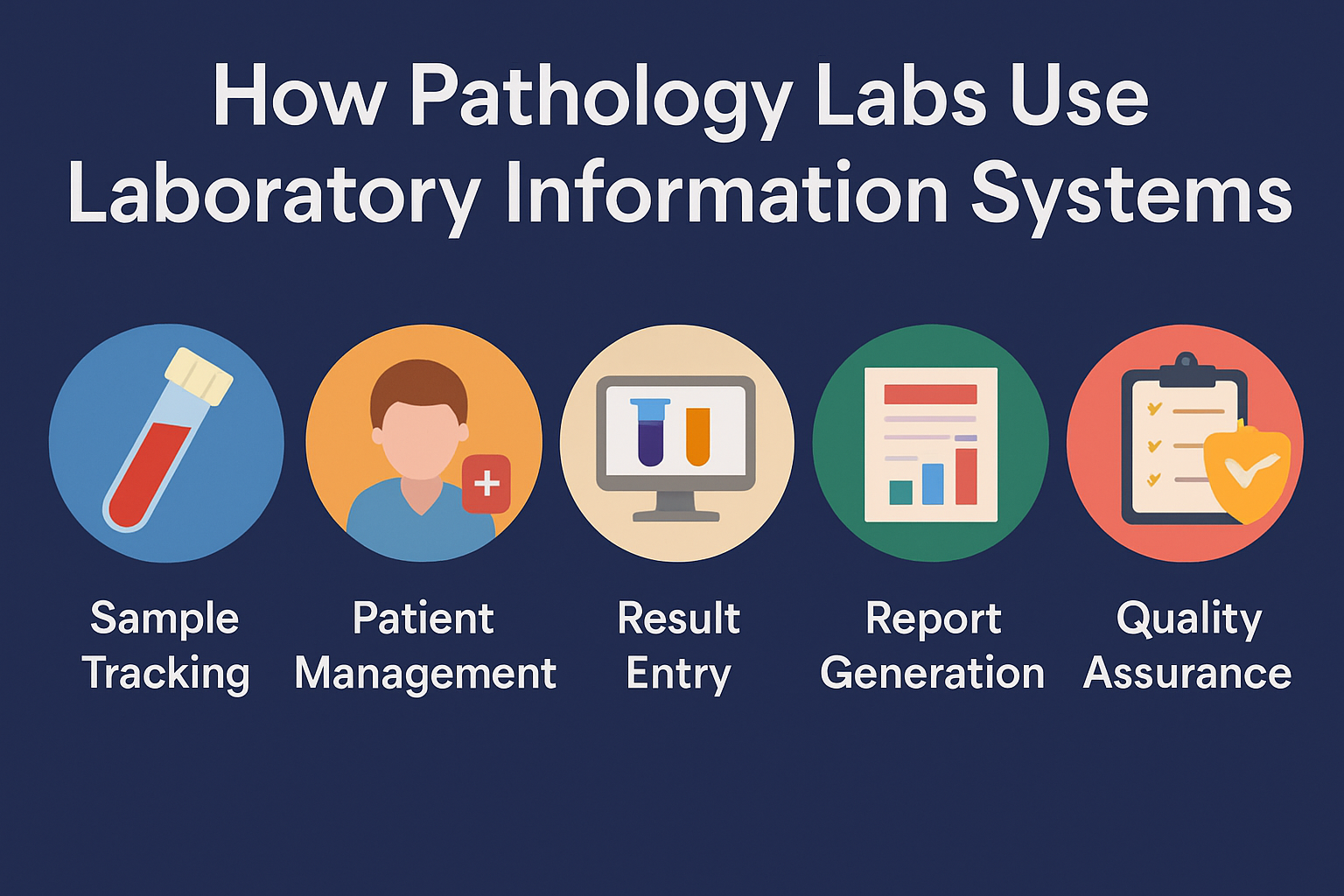
How Pathology Labs Use Laboratory Information Systems
Pathology labs handle some of the most sensitive and complex diagnostic work in healthcare. Every day, these labs manage hundreds or thousands of tissue and fluid samples, trying to produce accurate diagnoses as quickly as possible. There’s very little room for error, and even less time to waste. That’s where Laboratory Information Systems come in....

Beyond Clicks and Carts: Next-Gen Customer Experience in the Metaverse
The customer journey is undergoing its boldest reinvention since the birth of the smartphone. We’re moving from flat, scroll-based pages to spatial, story-driven worlds where people browse, compare, and commit inside living environments. In this shift, brands are learning that “presence” beats pixels: giving buyers a sense of space and agency leads to faster, more...

California Auto Transport Guide: How to Ship a Car from California to Florida, Texas, or New York
Looking to ship a car out of California? Whether you’re moving, buying a vehicle, or relocating for work or school, California auto transport services can help you move your vehicle safely and efficiently. At Navi Auto Transport, we make the process easy — and fast. In this guide, we’ll break down how to ship a car from California to top...

Cybersecurity in 2025: Why Proactive Defense Matters More Than Ever
In today’s interconnected digital landscape, cybersecurity has become a critical priority for individuals, businesses, and governments alike. With the rise of remote work, IoT, and AI-driven automation, the threat surface has expanded rapidly — and so have the risks. From ransomware attacks on hospitals to sophisticated phishing campaigns targeting employees, cyber threats are no longer...