Asad Ijaz
NetworkUstad's lead networking architect with CCIE certification. Specializes in CCNA exam preparation and enterprise network design. Authored 2,800+ technical guides on Cisco systems, BGP routing, and network security protocols since 2018. Picture this: I'm not just someone who writes about tech; I'm a certified expert in the field. I proudly hold the titles of Cisco Certified Network Professional (CCNP) and Cisco Certified Network Associate (CCNA). So, when I talk about networking, I'm not just whistling in the dark; I know my stuff! My website is like a treasure trove of knowledge. You'll find a plethora of articles and tutorials covering a wide range of topics related to networking and cybersecurity. It's not just a website; it's a learning hub for anyone who's eager to dive into the world of bits, bytes, and secure connections. And here's a fun fact: I'm not a lone wolf in this journey. I'm a proud member and Editor of Team NetworkUstad. Together, we're on a mission to empower people with the knowledge they need to navigate the digital landscape safely and effectively. So, if you're ready to embark on a tech-savvy adventure, stick around with me, Asad Ijaz Khattak. We're going to unravel the mysteries of technology, one article at a time!"
Wave Plastic Surgery Arcadia Review: Costs, Services & Patient Experience
Wave Plastic Surgery Arcadia has gained attention as a cosmetic surgery provider in Southern California, attracting patients seeking modern aesthetic procedures in a professional setting. Known for offering a range of surgical and non-surgical treatments, Wave Plastic Surgery Arcadia serves individuals looking for facial rejuvenation, body contouring, and advanced cosmetic enhancements. Understanding costs, services, and...

Creating a Balanced Family Life Through Routine and Support
Balancing work, personal responsibilities, and family life can be overwhelming for many parents. In a world that constantly demands attention, maintaining a healthy family dynamic requires thoughtful planning and support. In 2026, these challenges have intensified due to evolving work trends like hybrid models and AI-driven productivity demands. According to ongoing insights from the U.S....

SIEM Event Correlation: Detecting Complex Attacks Faster
Most security breaches don’t announce themselves. There’s no single moment where alarms blare and screens flash red. What actually happens is far quieter. A login attempt fails a few times. Someone accesses a file they don’t usually touch. An outbound connection goes somewhere slightly odd. Each of these events sits in a log somewhere, tagged as low severity, and gets ignored That’s exactly what attackers count on. Event correlation inside a SIEM platform is the mechanism that changes this dynamic. It’s how security teams stop looking at individual data points and...

Enterprise Digital Asset Management: When You Need Virtual Data Rooms for Extra Security
Most enterprises begin their digital asset management with standard solutions like Google Workspace or Microsoft SharePoint. These tools handle collaboration and file organization effectively. But when stakes rise—during M&A negotiations, legal proceedings, or sensitive IP transfers—standard cloud storage exposes critical vulnerabilities that can cost millions or derail major transactions. Where Standard DAM Falls Short Traditional...

Understanding the New Wave of Cyberattacks
Cyberattacks have been around since before the internet, yet it seems like they’re being talked about much more in recent times. Data breaches that expose millions of people’s credentials and personal details regularly make headlines. Increasingly, so do attacks targeting individuals whose complexity wouldn’t have been possible even five years ago. How are these digital...
Top Mobile Proxies for OnlyFans Management — 4G & 5G (2026)
Managing multiple accounts on OnlyFans requires a reliable infrastructure to prevent bans because the platform monitors suspicious activity, including multiple logins from the same IP address. Thus, a high-quality mobile proxy for OnlyFans protects agencies and content creators from blocking. The best mobile proxies for OnlyFans leverage genuine mobile carrier IP addresses rather than datacenter...

Why Frontline Workers Need a Different Approach to Login Security
Frontline workers make up nearly 80% of the global workforce. They run factory floors, stock shelves, manage hospital patients, and keep warehouses moving. Yet most login security systems were built for office employees sitting at personal desks with personal devices. That disconnect creates real problems. Shared terminals, rotating shifts, and time-sensitive tasks make traditional password...

Discover the Power of Colostrum for Skin and Hair Vitality
Dermatological issues, such as acne, dry skin, and eczema, have become quite common for people. Healthy skin reflects overall well-being, which gives you a vibrant and youthful appearance that boosts confidence. Inclusion of colostrum in daily nutrition can offer the body vital nutrients needed for healthy skin and hair. However, reliable online sources for supplements...
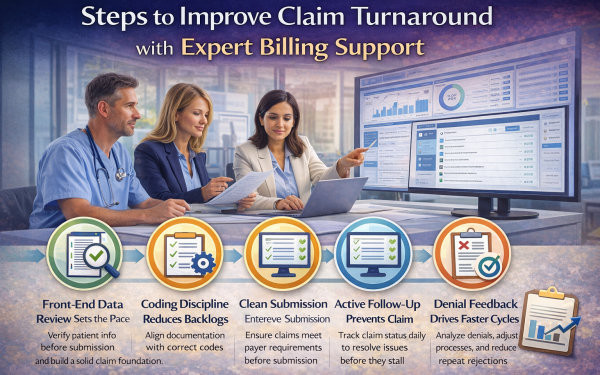
Steps To Improve Claim Turnaround With Expert Billing Support
Slow claim turnaround frustrates clinics more than almost any other billing issue. Payments stall, reports fall behind, and staff spend hours chasing updates. Even small delays can disrupt cash flow and planning. Faster turnaround depends less on speed and more on structure. This article explains practical steps that expert billing support uses to keep claims...

Non Surgical Nose Job: A Modern Alternative to Traditional Rhinoplasty
A non surgical nose job has become an increasingly popular aesthetic option for individuals seeking subtle nasal refinement without surgery. This approach uses injectable treatments to improve the shape and balance of the nose, offering immediate results with minimal downtime. As awareness grows, many patients begin researching non surgical nose job near me to find...