
CCNA
Cisco Certified Network Associate certification resources

The Anatomy of a Networking Halfway House: Where Layer 2 Meets Layer 3
Halfway house configurations occur when network devices operate between Layer 2 and Layer 3 functions, creating instability and security risks.

How to Pass CCNA Faster: Study Strategies That Actually Work
Passing the CCNA is often seen as a rite of passage in the networking world. It is the moment where theory meets reality. However, many people find themselves stuck in a loop of endless reading without actually making progress. If you want to earn your certification without spending six months buried in a textbook, you...

The Invisible Handshake: A Deep Dive into Network Control Protocols (NCP)
Imagine you are in a room filled with people speaking different languages. For any meaningful conversation to happen, everyone must first agree on a common language. In the world of networking, this is the role of protocols. However, before a web browser can speak HTTP (the language of the web) or an email client can...

Comprehensive Guide to Access Control Lists (ACLs) in Cisco Networking: Concepts, Types, Operations, Wildcard Masking, Creating, Placemnet and Differences (2025)
An Access Control List (ACL) is a critical feature in Cisco networking, used for security and traffic management. It consists of a set of rules designed to filter network traffic by specifying which users or systems are granted access to network resources and what operations they can perform. ACLs are commonly configured on devices with...
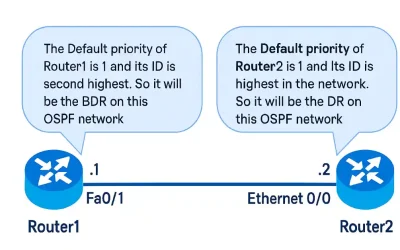
Understanding OSPF Neighbor Adjacencies, DR/BDR Election, and Database Synchronization
If a router interface is configured with OSPF, the router must determine if another OSPF neighbor is on the link. To do this, the router forwards a Hello packet containing its router ID to all OSPF-enabled interfaces as multicast. The OSPF process uses the router ID to recognize every router individually in the OSPF area....

Switch vs. Hub: Overcome Obsolete Tech with Expert Guidance (Updated 2026)
In networking, understanding the differences between a switch and a hub (switch vs. hub) is fundamental for students and networking professionals. While hubs were historically used to connect devices in local area networks (LANs), modern networks rely on switches for efficiency, scalability, and security. This article explores their roles, distinctions, and practical applications, with Cisco-specific...

The functions of the Router Briefly Explained
Routers are the cornerstone of modern networking, enabling seamless communication between devices across local and global networks. For CCNA and CCNP students, understanding the functions of the router is essential for mastering network fundamentals, configuring Cisco devices, and passing certification exams. A router connects multiple networks, determines the best path for data packets, and ensures...
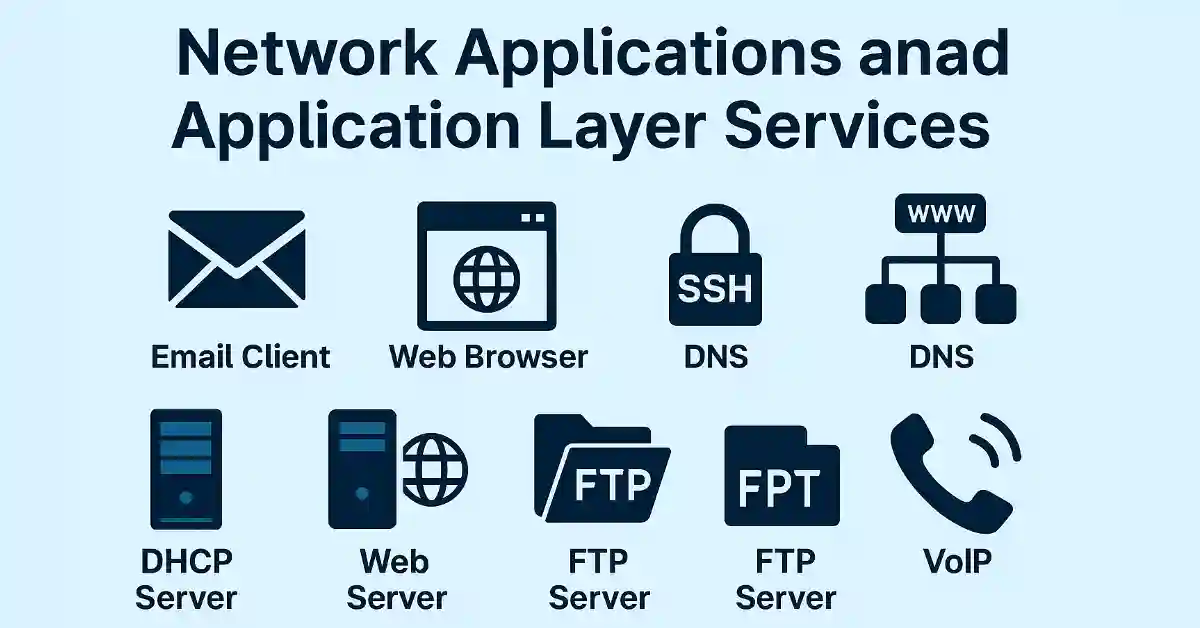
Network Applications and Application Layer Services for CCNA/CCNP Success (Updated 2025)
Network applications and application layer services are critical components of modern networking, forming the backbone of communication in enterprise and cloud environments. For CCNA and CCNP students, understanding these concepts is essential for mastering the application layer of the OSI model, a key topic in Cisco certification exams. Network applications, such as email clients and...
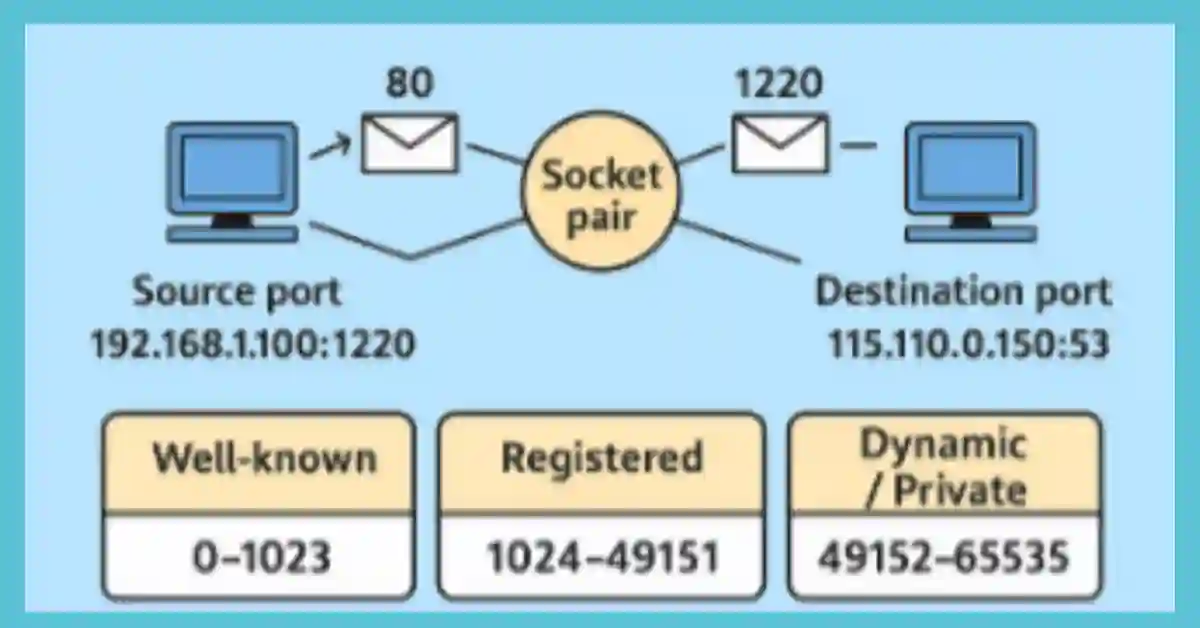
Virtual Port Numbers Explained: Your Gateway to Smarter Networking with our Exclusive Guide 2025
The transport layer uses two port numbers: the source port and the destination port. The source port numbers belong to the originating application on the local host, while the destination port numbers belong to the destination application on the remote host, crucial for 2025 IoT scalability Port numbers resolve the protocol to which incoming traffic...
Understanding Transmission Modes: Simplex, Half-Duplex, and Full-Duplex Explained
Transmission modes define the direction and flow of data between devices in a network, playing a critical role in determining communication efficiency. Whether it’s a one-way broadcast like radio or simultaneous two-way conversations like a phone call, understanding these modes—simplex, half-duplex, and full-duplex—is essential for network design and optimization. This article explores each mode with...