Networking
Network architecture and protocol deep dives
DisplayPort Cables: A Comprehensive Guide
Digital displays have become so flexible that you must establish the proper connection to ensure optimum performance. DisplayPort cables have become the leading technology for high-definition video and audio transmission, packed with all the newest features. The guide on DisplayPort technology is not just a simple one. It will take you through the world of...
Understanding Triple-Speed Ethernet
Ethernet technology has been a cornerstone of network communications since its inception at Xerox PARC in the mid-1970s. Over the years, Ethernet has evolved significantly, with data transfer rates increasing from the original 2.94 Mbit/s to the latest 400 Gbit/s and even up to 1.6 Tbit/s under development. This evolution has been driven by the...

Host Bus Adapters: Elevating Data Connectivity to New Heights
In today’s digital landscape, where data is generated and consumed at an unprecedented pace, efficient storage and seamless data transfer are critical for businesses and organisations of all sizes. Host bus adapters stand at the forefront of enabling high-speed connectivity between host systems, such as servers, and storage or network devices. This comprehensive guide explores...

Boost Your Networking: Proven Tools & Tech for Seamless Automation
In the technological world of today, where the pace of change is so fast, the effective functioning of networks is one of the most crucial things for organisations of any size. While the complexity of the networking infrastructure is increasing and connectivity is more suggested, manual network management is implemented inefficiently. This is the area...
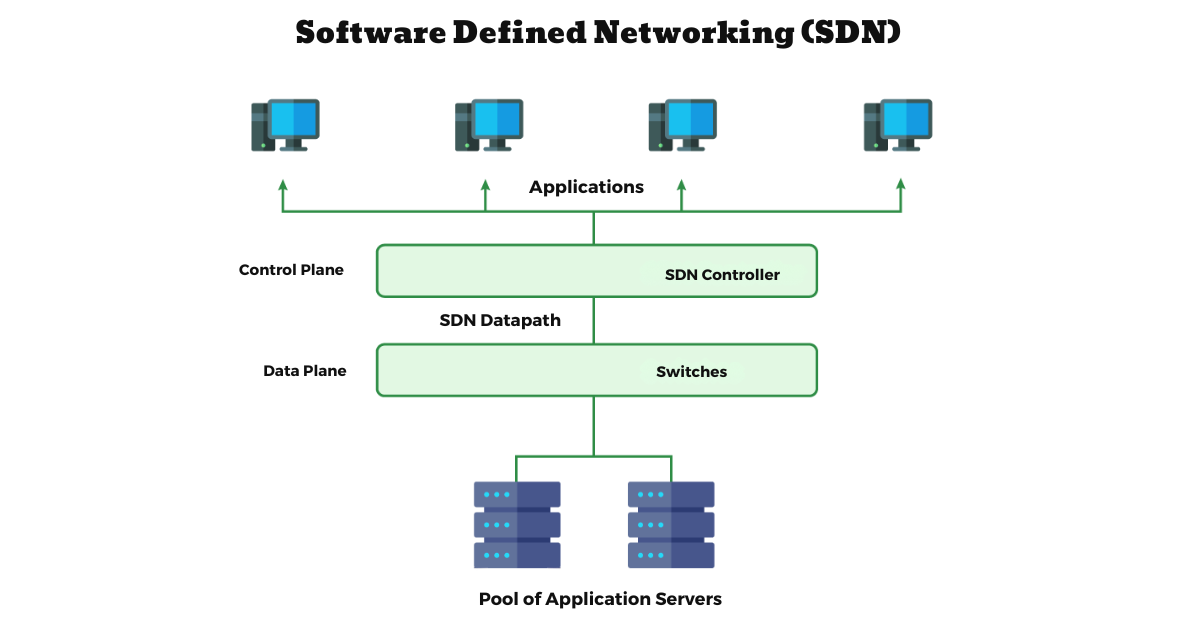
Software-Defined Networking (SDN): The Future of Networking
Digitization keeps marching forward, and network infrastructure seems to follow suit as more and more service providers and enterprise customers demand excellence and resiliency in communication links. Enter Software-Defined Networking (SDN), which stands for soft. What is Software-Defined Networking (SDN)? SDN means the approach of undertaking a new network architecture. In the past, the data...

IP Logging Empowers: Network Forensics Made Easy in 2026
In the era of digitalization, which has invariably made data a new red, protecting the integrity of the network has become an ultimate rule. Advanced IP logging is a sentinel, offering security and a treasure trove of insights. Let’s delve into how this technology can transform your network monitoring experience. The Essence of IP Logging...

Data Center Victories: The Thrilling Wins Empowering Growth in 2026
Today, with an enormous amount of information, data center networks really are the bone and the spine of the information-centered society. They take responsibility for fast and stable data transfer and act as a guaranteed point for a data center, providing high availability and hand-to-hand performance. As we navigate through 2026, the data center industry...

Rotating Proxies: Enhancing Online Anonymity and Efficiency
In the digital age, the ability to remain anonymous and access the internet without restrictions has become a priority for many users and businesses. This is where the concept of rotating proxies comes into play, offering a sophisticated solution to these needs. A proxy acts as an intermediary between a user’s device and the internet,...

IS-IS: The Expert Guide to Your Network Traffic
Let’s take a moment to visualize yourself in a crowded, intricate city landscape, attempting to find the quickest route to your destination. Your best bet would be to rely on a GPS, right? In a similar vein, routing protocols are the GPS of the digital world, directing data traffic over the internet. And, standing tall...

Virtualization in Network Security: Safeguarding Digital Borders with Advanced Strategies
Virtual network security involves designing strategies, protocols, and technologies that actively create virtual obstacles and blocks to prevent cyber-attacks and unauthorized access to virtual networks. Virtual network firewalls level data protection by applying safeguards that guarantee the security of data comprising confidential information, assuring the integrity of the system, and the correct availability of needed...