Cybersecurity
Welcome to NetworkUstad’s Cybersecurity Hub – your comprehensive resource for staying secure in an increasingly connected world. In today’s digital landscape, cyber threats evolve faster than ever. From sophisticated ransomware attacks to simple phishing scams, businesses and individuals face constant risks. Our cybersecurity section delivers practical, actionable insights to help you build robust defenses and protect what matters most. Whether you’re a security professional, IT administrator, business owner, or someone concerned about digital privacy, you’ll find expert guidance covering everything from fundamental security principles to advanced threat protection strategies. What You’ll Discover: 🔐 Security Fundamentals – Master the CIA Triad, understand information security basics, and build a strong foundation in cybersecurity principles. 🛡️ Threat Intelligence – Learn about different attack vectors, hacker types, malware categories, and emerging cyber threats targeting organizations worldwide. 🔒 Protection Strategies – Explore practical defense mechanisms including encryption, multi-factor authentication, network security, endpoint protection, and access controls. 📊 Compliance & Governance – Navigate regulatory requirements like GDPR, HIPAA, PCI DSS, and industry frameworks such as NIST and ISO 27001. ⚡ Incident Response – Prepare for the inevitable with comprehensive guides on breach detection, containment, recovery, and forensic analysis. 🚀 Emerging Technologies – Stay ahead with insights on AI security, cloud protection, IoT vulnerabilities, blockchain security, and quantum computing threats. 💼 Enterprise Security – Discover strategies for securing hybrid workforces, protecting corporate data, managing third-party risks, and building security-aware cultures. 🎓 Career Development – Explore ethical hacking careers, certification paths (CEH, CISSP, OSCP), and skill development resources. Our articles combine technical depth with practical applicability. We break down complex security concepts into digestible insights, provide real-world examples, and offer step-by-step implementation guides. No unnecessary jargon—just clear, actionable cybersecurity knowledge you can use immediately. From understanding basic threats to implementing enterprise-grade security architectures, NetworkUstad’s cybersecurity content empowers you to make informed decisions and take meaningful action. We cover the full spectrum: network security, application security, data protection, cloud security, mobile security, and everything in between. Security isn’t a one-time project—it’s an ongoing journey. Join thousands of readers who trust NetworkUstad to keep them informed about the latest threats, best practices, and innovative solutions in cybersecurity. Protect your network. Secure your future. Start exploring our cybersecurity resources today.

The Human Firewall: Empowering Employees to Combat Cyber Threats
As technology advances and becomes increasingly integrated into our daily lives, organizations must recognize the importance of a robust cybersecurity strategy. While traditional cybersecurity measures focus on protecting the organization’s technical perimeter, the human firewall emphasizes the role of the employees in preventing cyber threats. This method considers employees as the first line of defense,...

Exploring Trendzguruji.me Cyber Trends
Friends, I am a reader of cybersecurity, so I searched for some cybersecurity information and then read about terendzguruji.me. I have found many well-written articles about this platform and gathered all its information. I have found many beautiful articles covered by this trendzguruji.me on different big blogs, like the following. Comprehensive Guide to Computer Awareness...

Mastering Remote Access in IoT: A Technological Revolution
In our ever-connected world, the Internet of Things (IoT) is a technological juggernaut, seamlessly integrating smart devices into our lives. IoT devices have dramatically reshaped our daily existence from intelligent thermostats fine-tuning our home climate to wearable health trackers monitoring our well-being. At the heart of this IoT revolution lies the concept of remote access,...
Unleashing the Power of IoT: A Comprehensive Expedition into the World of the Internet of Things
In the whirlwind of today’s tech-driven cosmos, the term “IoT” echoes through the digital corridors. But what’s the real deal with IoT, and how does it shape our lives? Gear up for an exhilarating journey as we embark on an expedition through the captivating universe of the Internet of Things (IoT), unearthing its essence, applications,...

Using Intrusion Detection Systems and Firewalls to Keep Your Digital Fortress Safe
The security of our online actions and data is critical in this day and age of digital technology. Given the increasing sophistication of cyber attacks, it is imperative to implement robust security measures. Firewalls and intrusion detection systems (IDS) are two crucial components of this security framework. In this comprehensive book, we will delve into...
Network Defence – Access Control Concepts
Zero Trust Security Zero trust represents a comprehensive strategy for securing access across various domains such as networks, applications, and environments. This method ensures the protection of access rights for users, end-user devices, APIs, IoT devices, microservices, containers, and more. It safeguards an organization’s workforce, workloads, and workplace. The fundamental principle underlying the zero-trust approach...

Cisco Umbrella: Revolutionizing Online Security
In today’s fast-paced digital world, where information flows seamlessly across borders and networks, the importance of cybersecurity cannot be overstated. Businesses and individuals alike rely heavily on the internet for communication, transactions, and accessing data. However, with this increased reliance on the digital realm comes a heightened risk of cyber threats. This is where Cisco...
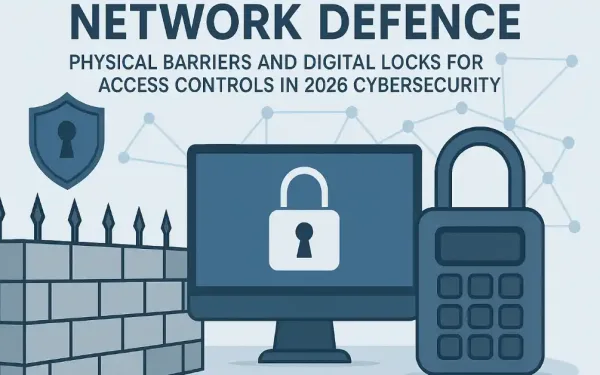
Network Defence – Physical and Logical Access Controls
Physical access controls refer to tangible measures put in place to obstruct any direct physical interaction with systems. The primary objective is to hinder unauthorized individuals from obtaining physical entry to facilities, machinery, and other assets within an organization. To illustrate, physical access control governs who is permitted to enter or exit, specifies the locations...
Cybersecurity Evolution: Investigating the Next-Generation Firewall
Protecting networks and sensitive information has become a top priority in today’s digitally driven society. Traditional firewalls are finding it difficult to keep up with the tremendous rate at which cyber threats are developing. The “next-generation firewall” (NGFW) comes into play in this situation. We will go into the complexities of NGFWs in this post,...

The Advantages of Hiding an IP Address with a VPN
In today’s digital culture, the theory of privacy has experienced a major transformation. As the online world becomes closer and closer, our digital footprint automatically grows, making us way more defenceless to threats online. Our IP address, a special identifier that says a lot about us – who we are and what we do online,...