
Cybersecurity
Network security, VPN guides, threat detection, and data breach prevention strategies.
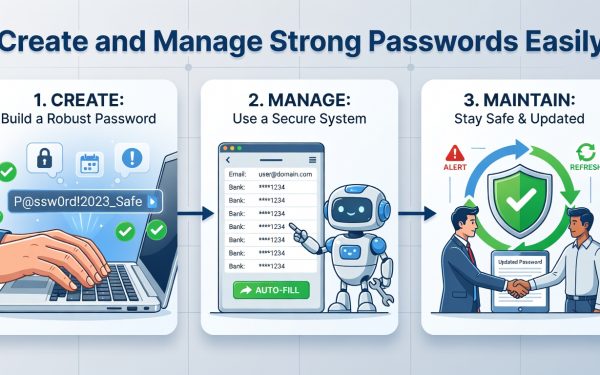
Create and Manage Strong Passwords Easily
This guide teaches beginners how to use password managers like Bitwarden to generate and store secure passwords, avoiding common cyber threats.

Best VPN Services Reviewed: Top Picks for Secure Online Protection
Discover the best VPN services reviewed with in-depth analysis, expert insights, and setup guides to enhance your online privacy and security effectively.
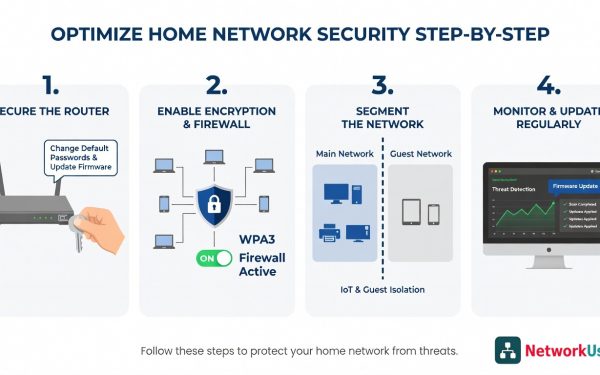
Optimize Home Network Security Step-by-Step
Discover how to assess, update, and secure your home network to prevent hacks and ensure safe online activities, all explained simply.

Common Cyber Threats in 2026: Risks and Defenses
Explore the top cyber threats of 2023, backed by data from Verizon and IBM, with expert insights and practical mitigation strategies to protect your digital assets effectively.

How to Set Up Two-Factor Authentication: Complete Guide
Discover step-by-step instructions to enable two-factor authentication on email, social media, and banking apps. Boost your security with expert tips and stats to prevent breaches effectively.

Essential Cybersecurity Best Practices for 2026 Protection
Discover proven cybersecurity best practices to safeguard your organization from rising threats, including access controls, training, and emerging AI trends for long-term security.

Why UK SMBs Are Still Losing to Ransomware — and What Actually Works
Ransomware attacks on UK small and medium businesses rose 67% between 2022 and 2024, driven by efficient RaaS models that make SMBs prime targets. These organizations face vulnerabilities from weaker defenses and limited recovery options, leading to average payments of £85,000 and total costs over £250,000. Practical controls can significantly reduce risks for teams without dedicated security expertise.

AI Trends in Cybersecurity 2026: Key Insights and Strategies
Discover how AI is revolutionizing cybersecurity with machine learning threat detection, real-world case studies, and implementation best practices to reduce breach costs by up to $1.76 million.

Best AI Tools for Cybersecurity 2026: Expert Guide
Discover top AI tools enhancing threat detection and response in cybersecurity. Gain insights from stats, case studies, and implementation tips for robust protection.

How to Implement Zero Trust Architecture: A Complete Guide
Discover a step-by-step approach to implementing Zero Trust Architecture, backed by stats and expert insights, to strengthen your cybersecurity defenses against modern threats.