
Cybersecurity
Network security, VPN guides, threat detection, and data breach prevention strategies.

9 Quantum-Proof Security Moves Smart Companies Are Making
The digital landscape of 2026 is defined by a silent but accelerating race against time. While quantum computing continues to promise breakthroughs in materials science and pharmacology, it simultaneously poses a fundamental threat to the cryptographic systems that secure the global economy. Most of the encryption currently protecting bank transfers, medical records, and state secrets...

Managed SOC Solutions: 4 Reasons for Real-Time Threat Protection in 2026
The cybersecurity landscape is evolving at an astonishing pace, driven by the relentless advances of technology and the innovative tactics of cyber adversaries. As a consequence, businesses need to be ever more vigilant and proactive in their security approach. Enter the managed SOC solutions, a robust way to counteract the myriad of threats that organisations...

Understanding the New Wave of Cyberattacks
Cyberattacks have been around since before the internet, yet it seems like they’re being talked about much more in recent times. Data breaches that expose millions of people’s credentials and personal details regularly make headlines. Increasingly, so do attacks targeting individuals whose complexity wouldn’t have been possible even five years ago. How are these digital...

Why Frontline Workers Need a Different Approach to Login Security
Frontline workers make up nearly 80% of the global workforce. They run factory floors, stock shelves, manage hospital patients, and keep warehouses moving. Yet most login security systems were built for office employees sitting at personal desks with personal devices. That disconnect creates real problems. Shared terminals, rotating shifts, and time-sensitive tasks make traditional password...

Why Do Hardware Quality and Data Safety Define Modern Cloud Hosting?
Your server is the heartbeat of your operation. Whether you are running a critical database, a corporate VPN, or a high-traffic e-commerce site, downtime or data corruption is not just an inconvenience—it is a reputation killer. While the market is flooded with hosting offers, seasoned administrators know that the real value lies not in the...
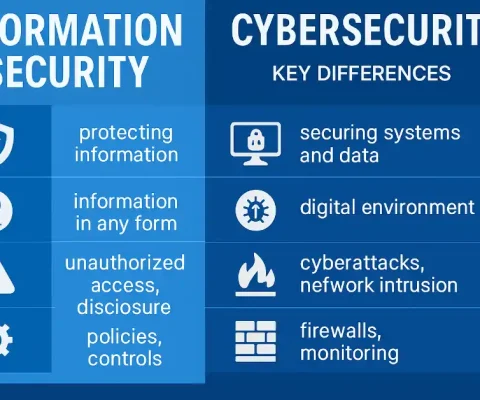
Common Gaps Between Security Policies and Real Threats
Security policies help define how organizations are expected to protect their systems and data. While these rules often reflect best practices and regulatory requirements, real attackers rarely behave as policies assume they do. They adapt quickly, exploit overlooked weaknesses, and take advantage of gaps between documented controls and real-world behavior. To better understand this gap,...

Network Traffic Analysis: How Twitch View Bots Manage Thousands of Concurrent Websockets
To the average internet user, live streaming is magic. A gamer presses a button in California, and milliseconds later, a viewer in Tokyo watches it happen. But for network engineers and system administrators, streaming is a massive exercise in bandwidth management, latency reduction, and persistent connection handling. The infrastructure behind platforms like Twitch is a...

Types of Hackers: White Hat, Black Hat, Grey Hat, and Beyond
When you hear the word “hacker,” what comes to mind? A hooded figure in a dark room, typing furiously on a keyboard, trying to steal your data? That’s only part of the story. The hacking world is far more complex and colorful than Hollywood portrays. Not all hackers are criminals. In fact, many work to...
Tech Headaches: What a Fully Managed Setup Does for You in 2026
It’s 3 PM on a Thursday, and you’re about to close a major deal. Suddenly, the server crashes. Your team can’t access critical files, client communication halts, and a wave of panic sets in. This isn’t just a minor inconvenience; it’s a direct hit to your productivity and bottom line. Sound familiar? These daily “tech...

Network and Security Integration: Shocking Truth About IT Misconfiguration in 2026
Imagine your IT team completes a routine network upgrade, boosting performance across the company. Everyone is happy. But weeks later, you discover that in the process of opening a new port for an application, they unknowingly created a gaping security hole that a hacker used to access your most sensitive customer data. This isn’t a...