Search Results
Showing results for "business" (3532 articles found)

Understanding the Potential of a SpaceX IPO: What Investors Need to Know
The prospect of an IPO has captured global attention, reflecting the company’s innovation and ambition. A SpaceX IPO would mark one of the most anticipated public offerings in recent history, potentially reshaping the investment landscape and giving a wider range of investors access to a pioneering aerospace venture. SpaceX has consistently disrupted the aerospace industry...

VAT Deduction in Poland – Key Rules Every Entrepreneur Should Know
VAT deduction is one of the key elements of the Polish tax system that allows entrepreneurs to significantly reduce the actual costs of running a business. Although the general principle of VAT deduction seems straightforward, in practice it often raises numerous questions and doubts. This applies both to domestic companies and to foreign entities conducting...

Why Frontline Workers Need a Different Approach to Login Security
Frontline workers make up nearly 80% of the global workforce. They run factory floors, stock shelves, manage hospital patients, and keep warehouses moving. Yet most login security systems were built for office employees sitting at personal desks with personal devices. That disconnect creates real problems. Shared terminals, rotating shifts, and time-sensitive tasks make traditional password...

Voice AI and Network Security: Protecting Real Estate Data in a Connected World
The Hidden Risks of Voice AI in Real Estate In the fast-paced world of real estate, where every client detail can clinch a deal, voice AI emerges as a quiet revolution. Picture an agent weaving through city traffic, fresh from a property showing. A quick spoken note captures the buyer’s thoughts—”loved the spacious kitchen, but...
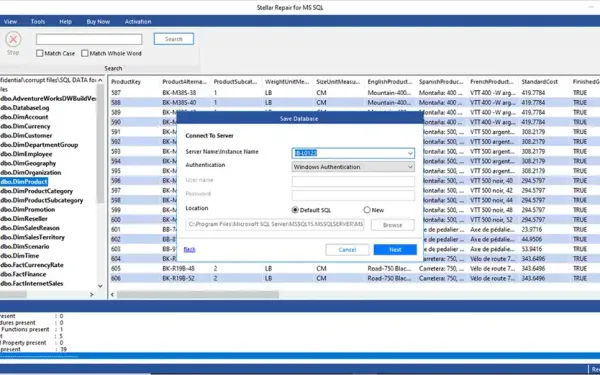
Comprehensive Review: Stellar Repair for MS SQL Technician
Version: 11.0.0.0Developer: Stellar Information Technology Private LimitedLicense Type: Single System (Technician Edition)Supported Platforms: Windows Server 2022/2019/2016/2012/2008/2003 and Windows 11/10/8.1/8/7 (64-bit only) Executive Summary Stellar Repair for MS SQL Technician is a comprehensive 3-in-1 software package designed for IT admins and database administrations. This software helps them reduce SQL downtime after a server crash, logical consistency...

How Can a UI/UX Design Agency Help with Digital Transformation?
Digital transformation sounds big. And abstract. New tools. New platforms. New ways of working. But for most companies, it comes down to something simpler. Can people actually use what’s being built? This is where a leading web and mobile UI/UX design agency plays a practical role. Not by “modernizing screens,” but by helping organizations turn messy...

Top network and data center events of 2026
Ready to travel to gain hands-on experience with new networking and infrastructure tools? Tech conferences – in person and virtual – give attendees a chance to access product demos, network with peers, earn continuing education credits, and catch a celebrity keynote or live entertainment. Check out our calendar of upcoming network, I&O, and data center conferences, and let us know…
Cisco extends AgenticOps model across networking, security, observability products
At the Cisco Live EMEA event going on in Amsterdam this week, Cisco unveiled a range of updates across its networking and security portfolio that are aimed at helping customers tap agentic AI technologies to more effectively run their enterprise infrastructure. “Agentic AI orchestrates workflows, moves data, communicates with other agents, and makes decisions autonomously. This represents a fundamental shift…
SSHStalker botnet brute-forces its way onto 7,000 Linux machines
A newly discovered botnet is compromising poorly-protected Linux servers by brute-forcing weak SSH password login authentication. Researchers at Canada-based Flare Systems, who discovered the botnet, got into its staging server and believe at least 7,000 servers had been compromised by the end of January, half of them in the US. The botnet’s weapons include exploits for unpatched Linux vulnerabilities going…
Cost is driving enterprises to rethink virtualization, but most aren’t ready yet
Enterprises are rethinking their virtualization strategies in the wake of Broadcom’s changes to VMware licensing, but most are not yet ready to make needed changes. That’s according to a new survey by HPE, which found that two-thirds of enterprises are planning material changes to their virtualization strategy within the next two years as they assess virtualization alternatives. There’s been plenty…