Search Results
Showing results for "seo" (616 articles found)

Docker CVE-2026-34040 Lets Attackers Bypass Authorization and Gain Host Access
A high-severity security vulnerability has been disclosed in Docker Engine that could permit an attacker to bypass authorization plugins (AuthZ) under specific circumstances. The vulnerability, tracked as CVE-2026-34040 (CVSS score: 8.8), stems from an incomplete fix for CVE-2024-41110, a maximum-severity vulnerability in the same component that came to light in July 2024. "

Watch this video of how a job interviewer exposes a North Korean fake IT worker
Interviewer Exposes North Korean IT Impostor In a viral video interview posted online on March 15, 2026, tech recruiter Elena Vasquez unmasked a job candidate as a North Korean operative posing as a South Korean IT specialist during a routine hiring process for a Silicon Valley firm. The exposure highlights growing concerns over state-sponsored cyber...

36 Malicious npm Packages Exploited Redis, PostgreSQL to Deploy Persistent Implants
Cybersecurity researchers have discovered 36 malicious packages in the npm registry that are disguised as Strapi CMS plugins but come with different payloads to facilitate Redis and PostgreSQL exploitation, deploy reverse shells, harvest credentials, and drop a persistent implant. "Every package contains three files (package.json, index.js, postinstall.js), has no description, repository,

How To Keep Up With New Standards for Websites in Competitive and Crowded Markets
In today’s digital landscape, standing still is the fastest way to fall behind. Websites are no longer just online brochures—they are dynamic, performance-driven platforms that must meet constantly shifting expectations from users, search engines, and competitors alike. Businesses operating in crowded markets face even greater pressure, where even small improvements in usability, speed, or visibility...

Poco X8 Pro Max Review: Impressive Performance on a Budget
Poco X8 Pro Max offers unbeatable battery life for gamers and creators, lasting two days on heavy use with 120W fast charging. Ideal for multitasking without lag—grab this mid-range powerhouse today!
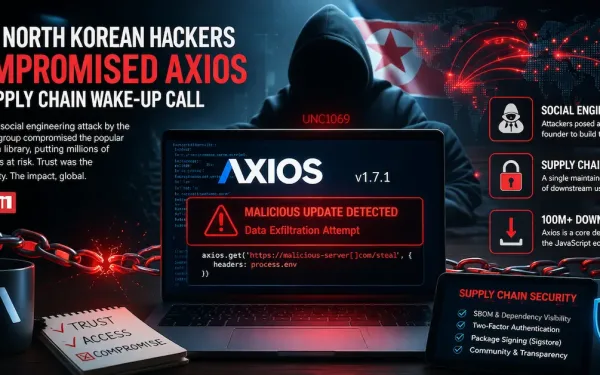
UNC1069 Social Engineering of Axios Maintainer Led to npm Supply Chain Attack
The maintainer of the Axios npm package has confirmed that the supply chain compromise was the result of a highly-targeted social engineering campaign orchestrated by North Korean threat actors tracked as UNC1069. Maintainer Jason Saayman said the attackers tailored their social engineering efforts "specifically to me" by first approaching him under the guise of the founder of a

BTCC Exchange 2026: Is It Still the Best Choice? Pros, Cons, and Key Performance
BTCC, founded in 2011, stands out as a trusted crypto exchange offering spot trading, futures with up to 500x leverage, copy trading, and a risk-free demo account. It emphasizes regulatory compliance across the USA, Canada, and Europe, with no history of hacks, and introduces tokenized stocks for diversified exposure. This review evaluates its features, user experience, fees, and support to help traders decide if it's the best platform.

Silver Fox Expands Asia Cyber Campaign with AtlasCross RAT and Fake Domains
Chinese-speaking users are the target of an active campaign that uses typosquatted domains impersonating trusted software brands to deliver a previously undocumented remote access trojan named AtlasCross RAT. "The operation covers VPN clients, encrypted messengers, video conferencing tools, cryptocurrency trackers, and e-commerce applications, with eleven confirmed delivery domains impersonating

AI Song Agent: A Smarter Way to Turn Ideas Into Finished Music
AI Song Agent revolutionizes music creation by bridging the gap between inspiration and execution through a conversational interface. It handles technical aspects like chord arrangement and song structure based on user intent. Creators benefit from quick generation, iterative refinement, and commercial-use exports on paid plans.

Why Reviews and Authority Signals Matter for High-Trust Service Providers
In today's digital world, trust for high-trust service providers relies on online reviews and authority signals rather than word-of-mouth. These elements provide social proof and demonstrate credibility, helping clients make confident decisions in sensitive industries. Encouraging genuine reviews and showcasing certifications can significantly boost reputation and success.