Network Security

Why Internet Connectivity is the Backbone of Live Experiences in 2025
When you think about what makes and breaks a mass event—be it a full trade show, a full tech conference, or a music festival outside—the most obvious things readily spring to mind: the speakers, the lights, the visitors, maybe even the food vans. But talk to any event operations manager in 2025, and you’ll hear...

Virtualization in Network Security: Safeguarding Digital Borders with Advanced Strategies
Virtual network security involves designing strategies, protocols, and technologies that actively create virtual obstacles and blocks to prevent cyber-attacks and unauthorized access to virtual networks. Virtual network firewalls level data protection by applying safeguards that guarantee the security of data comprising confidential information, assuring the integrity of the system, and the correct availability of needed...

Guarding the Digital Fortress: Essential Network Security Tools
With the ever-present risk of cyber threats, organizations need to deploy the most advanced network security tools to protect their digital assets. In this era of cyber warfare, guarding the digital fortress has become increasingly vital. This blog post will explore some of the best network security tools to defend your organization against lurking cyber...

Navigating the Enigma of Digital Network Security
In the swiftly progressing digital expanse, where intertwining network security serve as the vital force for both business transactions and personal exchanges, the interplay between perplexity and burstiness becomes pivotal. The intricacies of the digital tapestry are influenced by the perplexity of network structures and the burstiness of sentence structures. As human writers skillfully intermingle...

Network Security Investigating the Domain of Digital Defence
We live in a world where everything is connected. Network Security Fundamentals are increasing, and there are many hazards to our digital existence. Knowing the various types of network security is essential, whether you’re protecting important company information or personal data. This tutorial will delve into network security, covering everything from firewalls to VPNs. Let’s...

Unveiling the Differences Between Stateful VS Stateless Firewalls for Enhanced Cybersecurity
Introduction In the realm of cybersecurity, firewalls act as gatekeepers that control the flow of data between networks. They establish a barrier between your internal network and potential threats from the outside world. Stateful and stateless firewalls are two primary paradigms that define how this barrier is constructed.Enhance your cybersecurity knowledge by understanding the differences...

How To Make Your Business Information More Secure
Running a business means you have access to a lot of personal information. In addition to your information, you’ll have data regarding your employees, your vendors, and your customers. With so much sensitive information on the line, keeping it secure is essential. There is no “too much” regarding security for your company and its important...
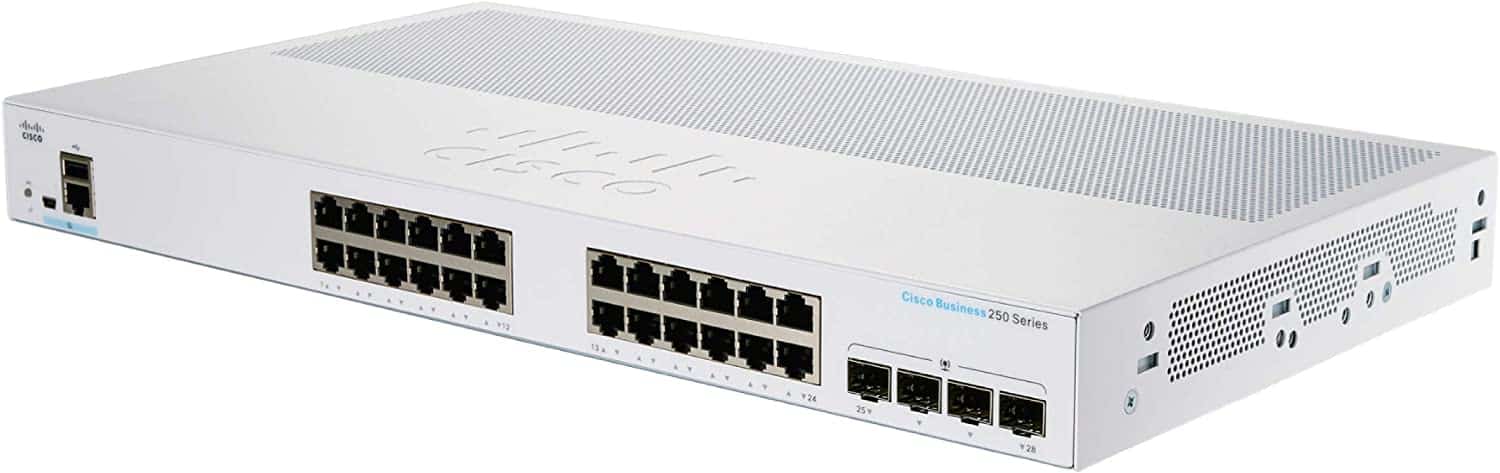
Cisco Business CBS250-24T-4G Smart Switch
Cisco Business CBS250-24T-4G Smart Switch” refers to a specific model of managed Ethernet switch from Cisco Systems, Inc. The “CBS250” designates it as a part of the Cisco Business line of networking equipment, and the “24T-4G” indicates that it has 24 Gigabit Ethernet ports and 4 SFP uplink ports. “Smart Switch” indicates advanced features such...
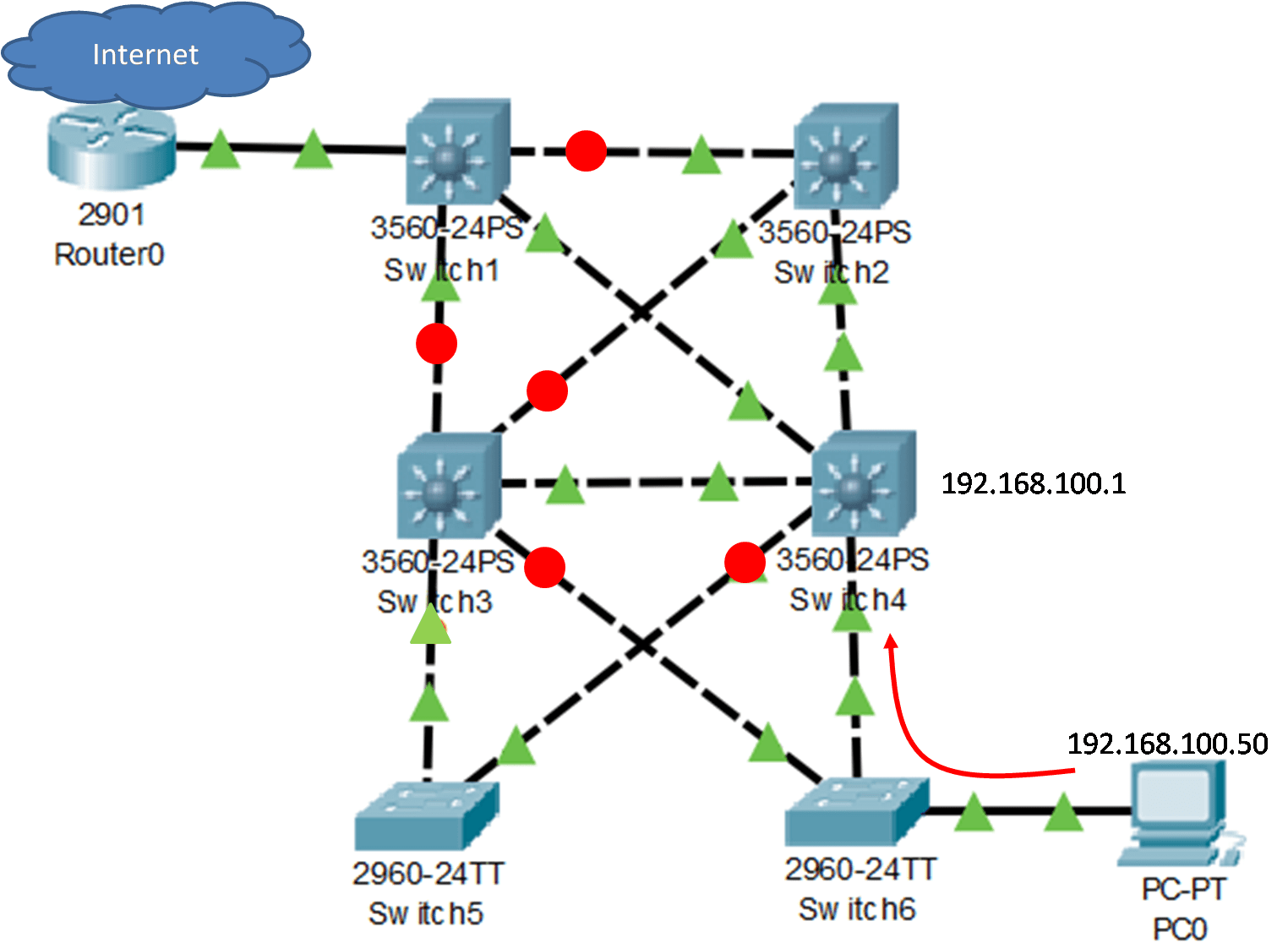
Default Gateway Limitations: Impact on Connectivity and Performance
Hosts at the access layer of a hierarchical network take advantage of the alternate default gateways. If a gateway (router interface) fails, the hosts configured with that gateway are cut off from outside networks. A method is needed to provide alternate default gateways in switched networks where two or more routers are connected to the...
What is Malware and Malicious Software? (Updated 2025)
Updated: October 19, 2025—Includes latest threats and network defenses. Malware, or malicious software, is a program or file designed to disturb computer processes and operations or gain unauthorized entry to the computer system, often via network protocols like RDP or SMB, without the user’s knowledge or permission. Malware has become a common term for all...