
How AI and Personalized Video Are Changing Customer Engagement
AI-powered personalization is shifting customer engagement from broad campaigns to interactions that adapt to each person’s context, intent, and timing. Research from McKinsey reports that most consumers expect personalization and become frustrated when it is missing, and it also finds that faster-growing companies derive substantially more revenue from personalization than slower-growing peers. Personalized video adds a human layer that text and static creative often cannot replicate. In a field experiment documented by the MIT Initiative on the Digital Economy, generative AI-enabled personalized video ads increased engagement by multiple percentage points compared with baselines, while also reducing production costs enough to…

How to Connect Your Smartphone to Your Car: 4 Proven Methods + A Practical Upgrade Path to Wireless
Connecting your phone to your car should make driving safer and simpler—hands-free calls, turn-by-turn navigation on the dash, and easy music control. The best method depends on what your vehicle actually supports. In this guide, you’ll learn four reliable ways to connect a smartphone to a car system: Bluetooth, USB, built-in Apple CarPlay/Android Auto (wired), and an upgrade to wireless CarPlay/Android Auto (when your car already supports the wired version). We’ll compare convenience, stability, and features so you can pick the option that matches your daily routine—short trips, commuting, or long drives. You’ll also get a quick compatibility checklist and step-by-step setup instructions for the…

Business Expansion Made Simple: Understanding Loan Costs Before You Borrow
Business expansion is a natural progression for enterprises seeking to grow, remain competitive, and meet rising customer demand. Whether it involves scaling operations, opening new locations, upgrading equipment, or hiring additional staff, expansion often requires a significant financial commitment. While internal savings may support smaller upgrades, they are not always enough for larger growth plans. In such situations, a Business Loan becomes a practical funding option. However, borrowing is a long-term financial responsibility. Understanding the true cost of a Business Loan before committing is essential for effective planning, stable cash flow, and sustainable business growth. Why Businesses Rely on Loans…

How Screening Software Identifies High-Risk Customers
For businesses that care about security and compliance, identifying which customers are high risk will always be high on their priority list. This is where screening software plays a crucial role. By conducting automated checks and performing comprehensive data analysis, these tools improve monitoring efforts and reduce the time spent on manual tasks. In this article, we will explain how screening software identifies high-risk customers. What Is Screening Software? Customer screening software is a type of digital tool that scans customer data for indicators that show risk. These programs regularly scan databases, track transactions, and check facts against lists supplied…

When “Just a Small Thing” Turns Into a Big Theft Case
Sometimes it starts with something that feels almost… ordinary. A coworker says a package went missing. A store manager points at a camera and suddenly acts like the footage is a slam dunk. A friend insists the police are “just asking questions,” so there’s no need to worry. And then, in the blink of a morning, there’s handcuffs, a booking photo, and that weird silent ride in the back of a patrol car. Here’s the part people don’t expect: theft cases aren’t just about what was taken. They’re about intent, valuation, how the evidence was gathered, what was said in…

How to Make Bitcoin the Core of a Balanced Crypto Portfolio
Bitcoin (BTC) often acts as a crypto portfolio anchor because of its fixed 21 million supply, deep liquidity, and long-running network. When building that core position, the way you get started matters. Many people accumulate gradually rather than all at once, using simple on-ramps that don’t require heavy setup. In that context, the option to buy btc via credit card can make sense—it allows small, flexible purchases without committing to a single exchange, which is helpful for steady, long-term accumulation instead of trying to time the market. Despite volatility, BTC’s predictable scarcity, strong security (record hashrate), and Lindy effect make…

Customer Portal Development for Scalable B2B Self-Service Experiences
Many B2B companies slowly start feeling that their old way of handling support just doesn’t work anymore when the number of customers increases. Emails stack up, phone calls take longer, and teams spend most of their day answering the same basic questions instead of focusing on real issues. The actual volume starts to slow them down and work stays undone. That’s when companies start investing in customer portal development, as a practical way to build a place where clients can log in, check information, manage requests, and handle simple tasks without waiting for someone to respond. Enabling Seamless Self-Service Capabilities…
Wave Plastic Surgery Arcadia Review: Costs, Services & Patient Experience
Wave Plastic Surgery Arcadia has gained attention as a cosmetic surgery provider in Southern California, attracting patients seeking modern aesthetic procedures in a professional setting. Known for offering a range of surgical and non-surgical treatments, Wave Plastic Surgery Arcadia serves individuals looking for facial rejuvenation, body contouring, and advanced cosmetic enhancements. Understanding costs, services, and patient experience is essential before scheduling a consultation. Located in Arcadia, California, the clinic benefits from proximity to the greater Los Angeles area while offering a more private and localized setting. Patients researching Wave Plastic Surgery Arcadia often want transparency regarding pricing, recovery expectations, and…
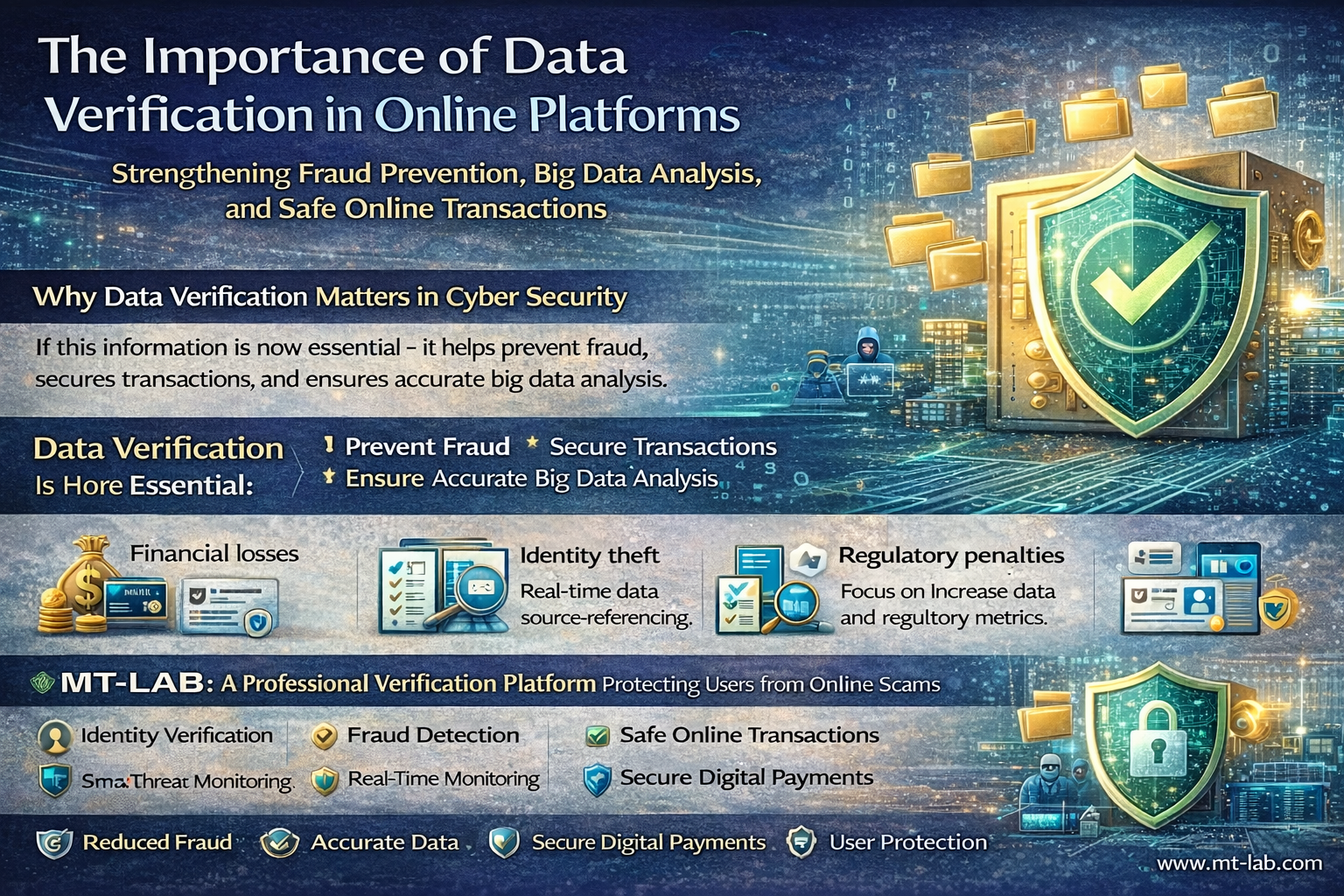
The Importance of Data Verification in Online Platforms
In today’s fast-paced digital economy, online platforms process the billions transactions daily. Data moves in a continuous flow across networks. This includes e-commerce purchases, fintech transfers, digital identity checks, and marketplace interactions. But, as digital convenience increases, so does cybercrime. Fraudsters exploit weak verification systems, manipulate data, and target vulnerabilities in online platforms. This is where data verification becomes a critical pillar of cybersecurity strategy. Data verification is now essential. It helps prevent fraud, secures transactions, and ensures accurate big data analysis. Why Data Verification Matters in Cyber Security Online platforms depend on data from users. This includes payment detaills,…

Best AI Lip Sync Tools of 2026
AI-powered lip sync technology has rapidly evolved from experimental software into a core part of modern digital content creation. In 2026, creators, marketers, agencies, and even enterprise teams rely on AI lip sync tools to produce realistic talking videos, localized content, AI avatars, and dynamic social media clips—without expensive production setups. If you’re looking for the Best AI Lip Sync Tools of 2026, this carefully ranked list highlights the most powerful, reliable, and creator-friendly platforms available today. We’ve evaluated each tool based on realism, workflow efficiency, scalability, pricing, and overall creative flexibility. Let’s dive in. 1. Magic Hour – The…
Creating a Balanced Family Life Through Routine and Support
Balancing work, personal responsibilities, and family life can be overwhelming for many parents. In a world that constantly demands attention, maintaining a healthy family dynamic requires thoughtful planning and support. In 2026, these challenges have intensified due to evolving work trends like hybrid models and AI-driven productivity demands. According to ongoing insights from the U.S. Surgeon General’s Advisory (last reviewed February 19, 2025), parents continue to face higher stress levels—33% report high stress in the past month compared to 20% of other adults, with 48% feeling completely overwhelmed most days versus 26% among non-parents. The APA’s Stress in America 2025…

Bearish Candlestick Patterns That Matter: How to Confirm Reversals and Filter False Signals
Candlestick patterns are usually the first thing beginners learn. They look simple: a few candles form a shape, and suddenly there’s a reversal signal. But in real trading, especially on lower timeframes, most of those patterns fail. The market is full of noise, fakeouts and traps that catch early entries. Bearish patterns can be powerful when they appear at the right spot with confirmation. The key isn’t just spotting the pattern, it’s knowing when it’s likely to work and when it’s just noise. In this guide we’ll cover the bearish candlestick patterns that actually matter, how to confirm them properly,…

SIEM Event Correlation: Detecting Complex Attacks Faster
Most security breaches don’t announce themselves. There’s no single moment where alarms blare and screens flash red. What actually happens is far quieter. A login attempt fails a few times. Someone accesses a file they don’t usually touch. An outbound connection goes somewhere slightly odd. Each of these events sits in a log somewhere, tagged as low severity, and gets ignored That’s exactly what attackers count on. Event correlation inside a SIEM platform is the mechanism that changes this dynamic. It’s how security teams stop looking at individual data points and start seeing the full picture of what’s happening across their environment. What SIEM Actually Does Security Information and Event Management (SIEM) is a platform that collects log and event data from across your environment. Firewalls, endpoints, cloud workloads, Active Directory, web proxies it all flows in. The system stores it, normalizes it, and makes it searchable. But storage and search aren’t what makes SIEM valuable. What matters is what happening when the…
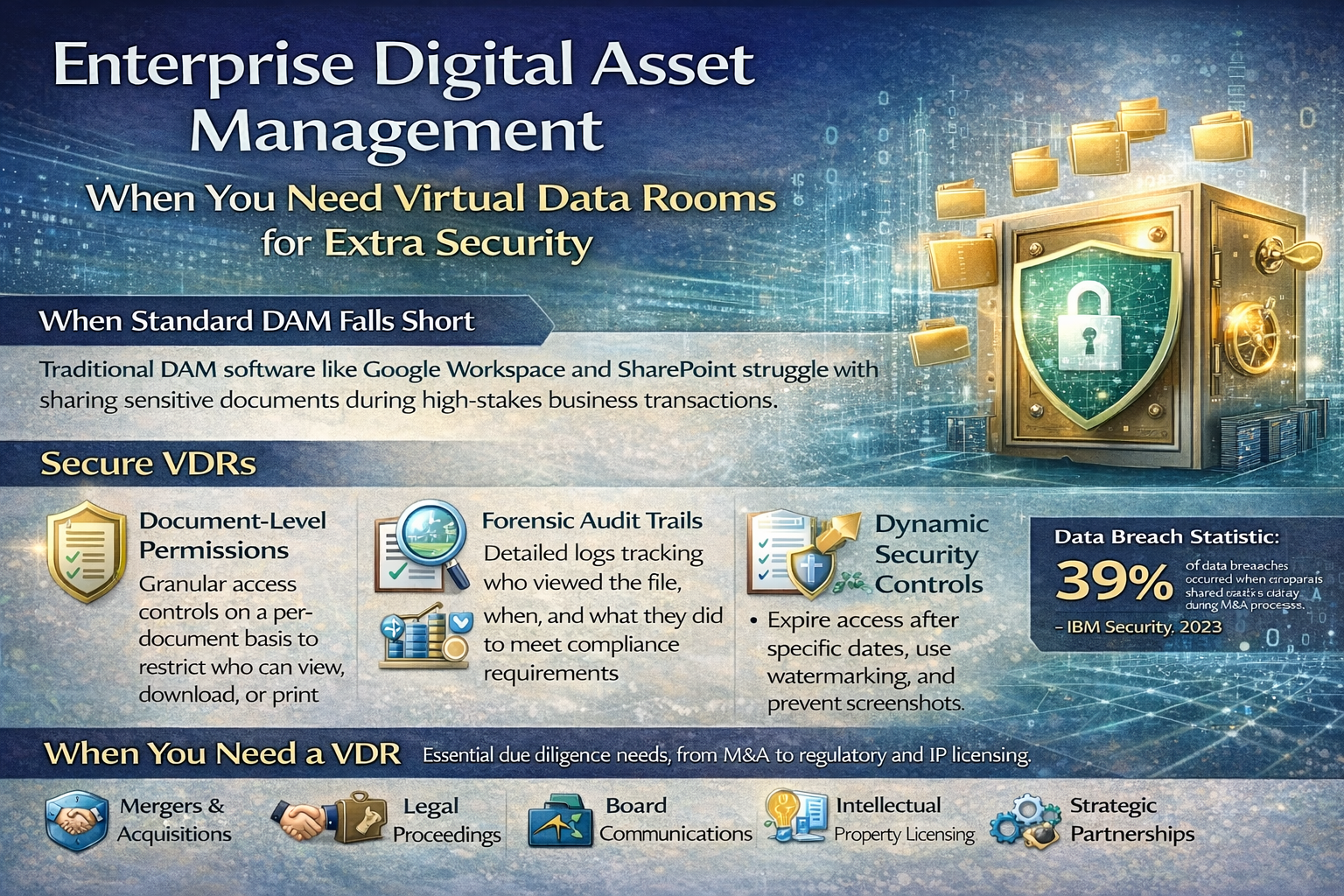
Enterprise Digital Asset Management: When You Need Virtual Data Rooms for Extra Security
Most enterprises begin their digital asset management with standard solutions like Google Workspace or Microsoft SharePoint. These tools handle collaboration and file organization effectively. But when stakes rise—during M&A negotiations, legal proceedings, or sensitive IP transfers—standard cloud storage exposes critical vulnerabilities that can cost millions or derail major transactions. Where Standard DAM Falls Short Traditional digital asset management systems excel at cataloging files and coordinating teams. However, they weren’t designed for sharing sensitive information with external parties during high-stakes business transactions. Consider a typical acquisition scenario. You need to share financial statements, customer lists, and IP documentation with potential buyers….
How Artificial Intelligence is Transforming Risk Management
Traditionally, the practice of risk management was one of quarterly audits, static spreadsheet analysis, and data analysis based on historical trends. This was the world of the past, a world in which software was installed from a CD-ROM and stayed that way for years at a time. But the world has changed dramatically since then. In the present day, it’s common for businesses and individuals alike to rely on a multitude of SaaS applications and web browser extensions in order to operate. This interconnected web of tools represents an unprecedented level of convenience but also an unprecedented level of risk…