Yasir Ali
Yasir Ali is a technology product reviewer with 9 years of hands-on experience testing networking equipment and consumer electronics. Certified in ITIL with a degree in Electrical Engineering. Has evaluated 400+ products.Complementing his technical skills, Yasir earned an MBA from the Virtual University of Pakistan, equipping him with valuable insights into business strategy, leadership, and management. This blend of expertise allows him to tackle IT challenges with both technical precision and strategic vision. As a regular contributor to NetworkUstad.com, Yasir writes clear, engaging blogs on Cisco certifications, networking essentials, cybersecurity, and emerging technologies. His approachable style inspires thousands of aspiring IT professionals, making complex topics accessible and empowering the next generation of network engineers.

Why Jura Coffee Machines Are the Gold Standard for Home Automation
Jura super-automatic espresso machines excel in home automation with Swiss engineering and Pulse Extraction Process for precise coffee. From entry-level E-series to flagship models, they deliver café-quality drinks effortlessly for any user.

What is the Shop App and How Does It Protect User Data?
Is Shop app safe? Yes, with zero breaches, PCI compliance, and 98% fraud blocking. This guide covers stats, expert views, and tips for secure shopping in 2026.

How to Install Screen Protectors Without Bubbles or Dust?
This guide provides a complete solution for applying screen protectors bubble-free. It covers essential preparation with tools like microfiber cloths and dust stickers, precise step-by-step application, and troubleshooting common issues for flawless results.

Why Nigeria’s Ride-Hailing Market Needs a Homegrown Uber Clone App in 2026
Nigeria is a country that never sleeps. From the busy streets of Lagos to the wide roads of Abuja, people are always on the move. By 2026, the way we travel is set to change even more. While big global names are present, there is a massive gap for a local player who truly understands...

How Do Technology Solutions Improve Efficiency in Healthcare Organizations?
Healthcare organizations manage complex operations every day. Patient records, appointment schedules, diagnostic reports, and communication systems require constant coordination. Manual processes and outdated systems can slow operations and create administrative burdens for medical staff. Many institutions adopt IT solutions for healthcare to streamline operations and improve service delivery. Modern digital systems help medical teams manage...
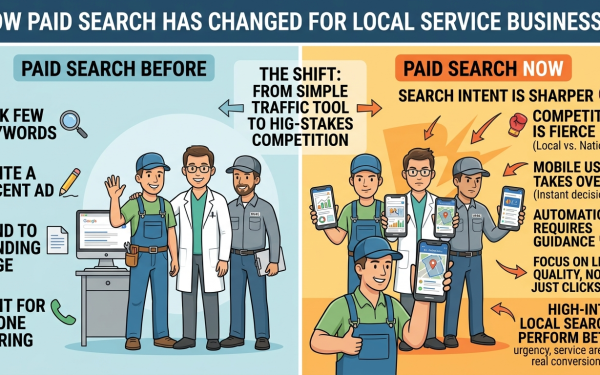
How Paid Search Has Changed for Local Service Businesses
Paid search used to feel pretty simple for local service businesses. Pick a few keywords. Write a decent ad. Send people to a landing page. Wait for the phone to ring. That version of PPC is mostly gone. Now, local paid search is tighter, faster, and far less forgiving. A plumbing company, pest control provider,...

Step-by-Step Guide to Setting Up BambooHR to AD Workflow
Integrating BambooHR with Active Directory enhances employee lifecycle management by automating data synchronization. Begin with defining data mappings for fields like name, email, and status to prevent errors. Configure secure API access in BambooHR to enable efficient, protected data transfer between systems.

What Is the Average Gold Loan Interest Rate and Why Does It Fluctuate?
Gold has always been a trusted financial asset in India, especially in households across Tier 2 to Tier 4 cities and towns where jewellery often serves as a safety net during emergencies. In recent years, the Gold Loan has emerged as one of the most practical borrowing options because it allows people to access funds...

The Frontier of Indian Equities: Why Experts Monitor the Nifty 250 Small Cap Index for Economic Signals
India’s equity sector is evolving quickly as domestic liquidity expands, retail participation grows, and institutional confidence in long-term growth remains strong. While large cap benchmarks dominate mainstream discussions, many experts believe the country’s real economic rhythm is reflected more accurately in the Nifty 250 small cap index. This space captures entrepreneurial activity, early expansion cycles,...

How Much Does It Cost To Build An MVP: A Complete Cost Breakdown
Building a Minimum Viable Product (MVP) is one of the smartest ways to validate an idea without investing heavily upfront. It helps you see how users interact with your concept, what they value, and which features deserve attention later. Many companies partner with a Custom Software Development Company at this stage because experienced teams accelerate...