Cybersecurity
Welcome to NetworkUstad’s Cybersecurity Hub – your comprehensive resource for staying secure in an increasingly connected world. In today’s digital landscape, cyber threats evolve faster than ever. From sophisticated ransomware attacks to simple phishing scams, businesses and individuals face constant risks. Our cybersecurity section delivers practical, actionable insights to help you build robust defenses and protect what matters most. Whether you’re a security professional, IT administrator, business owner, or someone concerned about digital privacy, you’ll find expert guidance covering everything from fundamental security principles to advanced threat protection strategies. What You’ll Discover: 🔐 Security Fundamentals – Master the CIA Triad, understand information security basics, and build a strong foundation in cybersecurity principles. 🛡️ Threat Intelligence – Learn about different attack vectors, hacker types, malware categories, and emerging cyber threats targeting organizations worldwide. 🔒 Protection Strategies – Explore practical defense mechanisms including encryption, multi-factor authentication, network security, endpoint protection, and access controls. 📊 Compliance & Governance – Navigate regulatory requirements like GDPR, HIPAA, PCI DSS, and industry frameworks such as NIST and ISO 27001. ⚡ Incident Response – Prepare for the inevitable with comprehensive guides on breach detection, containment, recovery, and forensic analysis. 🚀 Emerging Technologies – Stay ahead with insights on AI security, cloud protection, IoT vulnerabilities, blockchain security, and quantum computing threats. 💼 Enterprise Security – Discover strategies for securing hybrid workforces, protecting corporate data, managing third-party risks, and building security-aware cultures. 🎓 Career Development – Explore ethical hacking careers, certification paths (CEH, CISSP, OSCP), and skill development resources. Our articles combine technical depth with practical applicability. We break down complex security concepts into digestible insights, provide real-world examples, and offer step-by-step implementation guides. No unnecessary jargon—just clear, actionable cybersecurity knowledge you can use immediately. From understanding basic threats to implementing enterprise-grade security architectures, NetworkUstad’s cybersecurity content empowers you to make informed decisions and take meaningful action. We cover the full spectrum: network security, application security, data protection, cloud security, mobile security, and everything in between. Security isn’t a one-time project—it’s an ongoing journey. Join thousands of readers who trust NetworkUstad to keep them informed about the latest threats, best practices, and innovative solutions in cybersecurity. Protect your network. Secure your future. Start exploring our cybersecurity resources today.
System and Network Defence
This article centers on the management of cybersecurity operations, encompassing activities such as designing, building, operating, and continuously enhancing an organization’s overall security capacity. The initial line of defense revolves around ensuring the physical security of network equipment. In parallel, there exist dedicated application security measures designed to safeguard software integrity. It’s crucial to acknowledge...
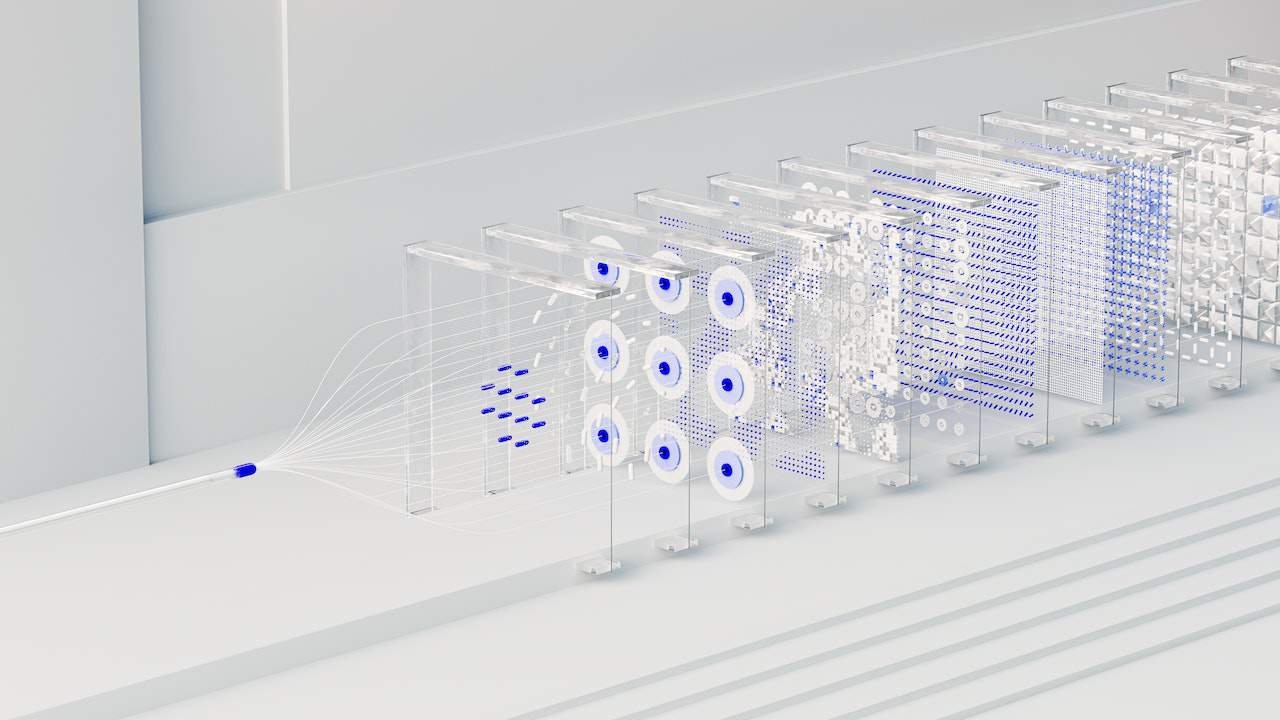
Network Defence: Principles of Defence-in-Depth Networking
? Cybersecurity analysts must be ready to face a wide array of threats. Their primary duty is safeguarding an organization’s network assets. To achieve this mission, they must initially pinpoint: Identify Assets ? As organizations grow, so does their array of assets. Consider the multitude of assets that a large organization must safeguard – a...
Defending the Digital Realm: A Comprehensive Review of OWASP
In an era where digital threats loom large and cybersecurity breaches continue to make headlines, safeguarding web applications is a paramount concern. Among the countless organizations dedicated to enhancing web application security, OWASP (Open Web Application Security Project) stands as a beacon of knowledge, collaboration, and innovation. Introduction Established in 2001, OWASP has evolved into...

8 Cybersecurity Concerns and How to Solve Them
Whether you’re running a business or just trying to have a normal life in 2023, you need to understand cybersecurity concerns. After all, you’re putting your personal information online and using tools susceptible to flaws, mistakes, data loss, and worse. While the platforms in question are doing their best to protect you, your safety is,...

Join a Comprehensive Cyber Security Boot Camp for Practical Skill Development
Due to the rising number of open positions and the acute lack of workers with the necessary technical, ethical hacking (penetration testing), and cybersecurity abilities, there is a huge need for cybersecurity specialists right now. All of this is fantastic for prospective cybersecurity analysts. However, you must have the necessary credentials before you may find...

The Role of Attack Surface Management in Reducing Cyber Risks for Businesses
Living in a connected, constantly online world certainly has its ups and downs. With the rise of remote work, online enterprise, and a stronger reliance on the internet in general, there are more cyberthreats facing businesses and individuals alike. Some network or data entry points are at high risk for these threats. Commonly known as...

9 Skills You Should Have to Work In Cybersecurity
With the rise of cyber threats globally, the need for proficient cybersecurity professionals has never been more pronounced. The modern world hinges on digitized systems and data protection, so there’s a high demand for individuals equipped with the right cybersecurity skills. Cybersecurity is crucial for a lot of parties, including but not limited to individuals,...
Unlocking the Power of PDFs with WeClick4PDF
Introduction: Weclick4pdf files have become essential to our lives in the constantly changing digital world. PDFs offer a dependable and consistent way to communicate and save documents across numerous devices and platforms, including corporate reports and educational resources. However, even though they are useful, working with PDFs may occasionally take work, particularly when trying to...

CRPF VPN Login Exclusive: Secure Access for Central Reserve Police Force Personnel (Updated 2025)
In today’s digital era (September 21, 2025), cybersecurity is paramount for India’s Central Reserve Police Force (CRPF), tasked with VIP protection, anti-insurgency operations, and Left-Wing Extremism (LWE) containment. As the official site states, the CRPF’s mission is to “empower the government to maintain the rule of Law, Public Order, and Internal Security” through proactive training...
Building a Successful Custom Software Development Team: Tips and Best Practices
To build a successful custom software development team, partnering with reputable custom software development companies can offer significant rewards. Currently, the victory of any business often depends on the efficiency and effectiveness of its software development team. Creating a successful custom software development team needs the best custom software developers with best strategy, planned decision-making, and...