
Cybersecurity
Network security, VPN guides, threat detection, and data breach prevention strategies.
How to Integrate Fortinet with Your Systems
In today’s world, cybersecurity is a top priority for any business, big or small. Fortinet is a leading provider of cybersecurity solutions that help businesses protect their networks, devices, and data from cyber threats. Fortinet offers a wide range of products and services that cater to different cybersecurity needs, including firewall, VPN, antivirus, and more....

Advantages of security license plate recognition
Installing security cameras is the most effective method for monitoring your home, company, and workplace while you are absent. The purpose of security camera installation should always be to deter criminal activity and increase safety by preventing thefts, break-ins, and damage. The residential camera installation provides peace of mind knowing that your property is being...
Benefits of Using an IP Information Tool for Increasing Online Security
Do you worry about the safety of your online accounts? It’s not surprising that many people are looking at methods of digital identity protection in light of the rising number of cyber threats. An internet protocol information tool might be helpful in this endeavor. Using this technology, you can learn crucial information about your network...

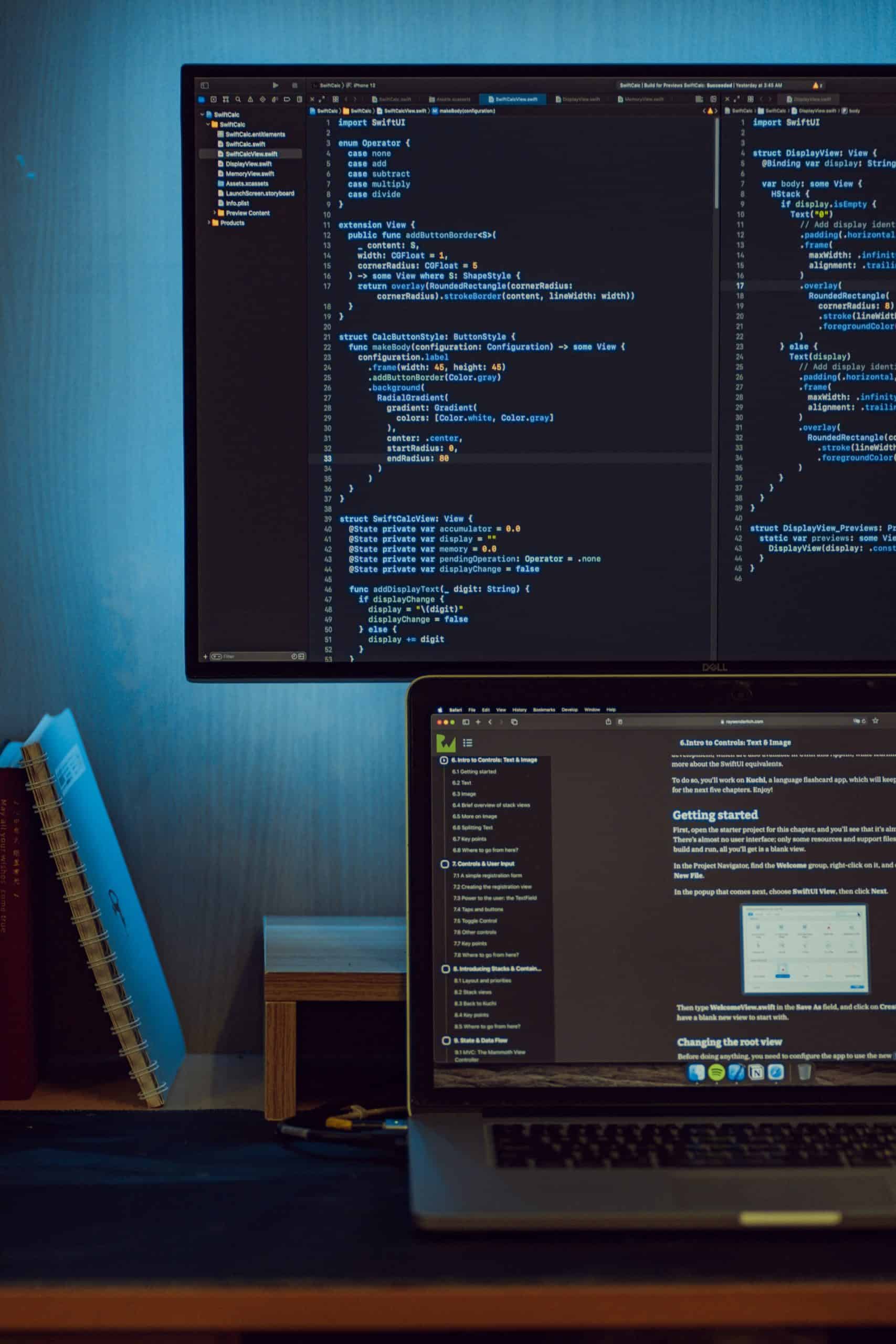
Best 5 Coding Platforms for Engineers
Engineers use coding platforms to develop, compile, and deploy applications. These platforms provide the tools necessary for engineers to create software, webpages, and other digital products. The platforms discussed in this article typically include support for multiple programming languages as well as additional resources such as text editors and debugging tools. With the right platform,...

Keeping Your Remote Team Safe from Cyberterrorism
As a result of the COVID-19 pandemic, many companies were forced to shift their operations to be remote rather than in-person. While the pandemic has since lessened in severity, many companies are opting to keep remote working options available for employees. While this can be beneficial in several ways, it can also come with its...

Looking into some industries that are revolutionizing cybersecurity
The world of cybersecurity is constantly evolving, with new industries and technologies emerging to address the increasing security threats faced by organizations and individuals. In this article, we will take a closer look at some of the industries that are revolutionizing cybersecurity and why Bitcoin Baccarat may be a better option. Why Is Bitcoin Baccarat...

Melbourne’s IT Security Experts: Total Protection for Your Business
Unified Threat Management Unified Threat Management (UTM) is a comprehensive approach to IT security that integrates multiple security functions into a single solution. This approach provides a centralized way to manage and monitor all security aspects of a network, including firewall, anti-virus, anti-spam, intrusion detection, and more. By combining these functions, UTM helps to simplify...

Don’t Get Hacked – Trust Glassons for Cyber Security
Don’t risk being hacked and losing important personal and financial information. Trust Glassons for cyber security and keep your online presence safe and secure. Our comprehensive security solutions protect against many cyber threats, including viruses, malware, and phishing attacks. With Glassons, you can have peace of mind knowing that your digital world is protected. Don’t...

Cybersecurity for individuals and how to protect yourself online.
In today’s digital age, cybersecurity is more important than ever. With increasing personal information being shared online, individuals must take steps to protect themselves from cyber-attacks. Cybersecurity protects internet-connected systems, including hardware, software, and data, from attack, damage, or unauthorized access. In this article, we will discuss some essential steps that individuals can take to...

The Evolution of Computer Vision: Past, Present, and Future Developments
Computer vision, the branch of artificial intelligence that enables computers to interpret and understand visual information, has come a long way since its early days. From simple image processing to complex deep learning algorithms, CV has undergone significant advancements over the years. In this article, we will delve into the history of computer-vision, examine the...