
Networking
CCNA tutorials, Cisco guides, and enterprise networking insights for IT professionals.
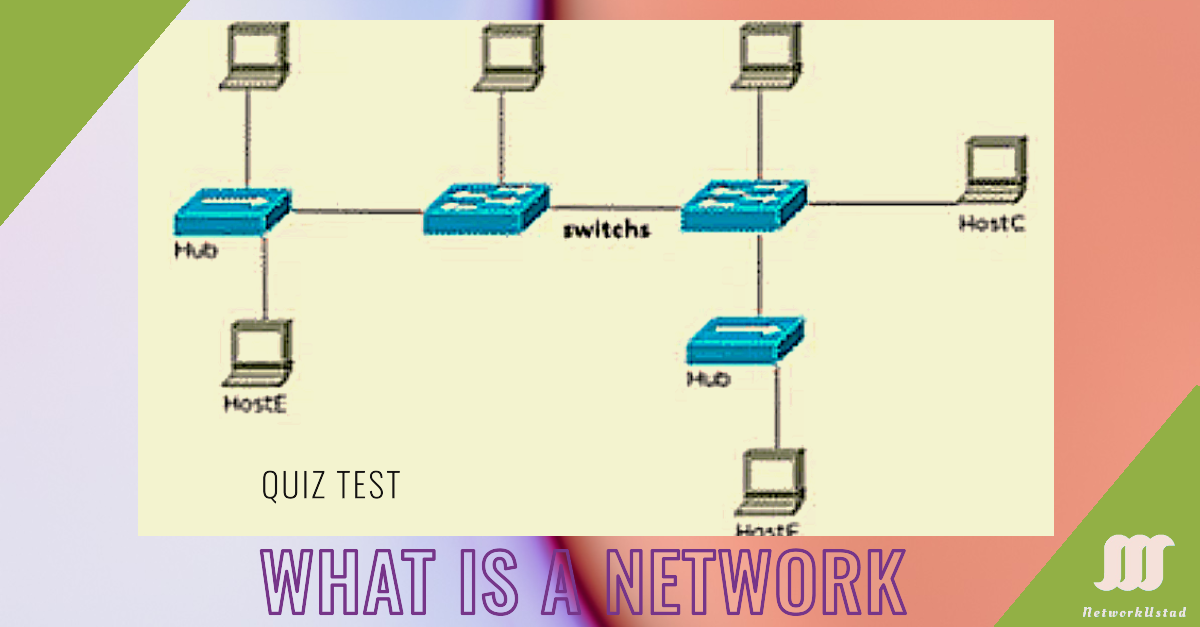
Quiz What is a Network – CCNA (200-301)
What is a Netowrk? Self-Assessment What is a Netowrk? Self-Assessment Submit Answers Reset Test If you feel week yourself in the topic visit What is a Network? – Exclusive Definitions
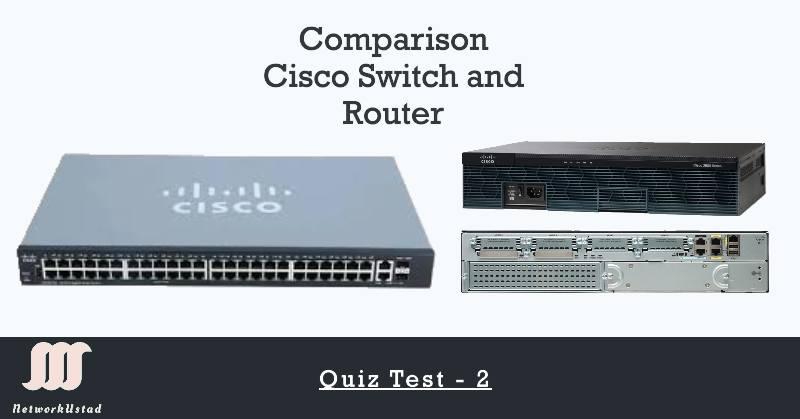
Quiz Comparing Switch and Router – CCNA (200-301)
Submit Answers Reset Test If you feel your self weak in the subject, visit Comparing Switch and Router: A Comprehensive Guide

Quiz Test – 3 Basic Network Component CCNA
Think You Know the 3 Basic Network Components? Prove It with the following quiz test. Submit Answers Reset Quiz
A Complete Guide to Pi123: Benefits, Features, and Security Concerns
Staying ahead of the curve is crucial in the rapidly evolving technological landscape. Pi123, a revolutionary solution, aims to redefine your digital experience. At its core, Pi123 is a dynamic platform designed to enhance user interaction with technology. Benefits of Pi123 In the bustling landscape of today’s digital era, safeguarding your information is crucial. At...
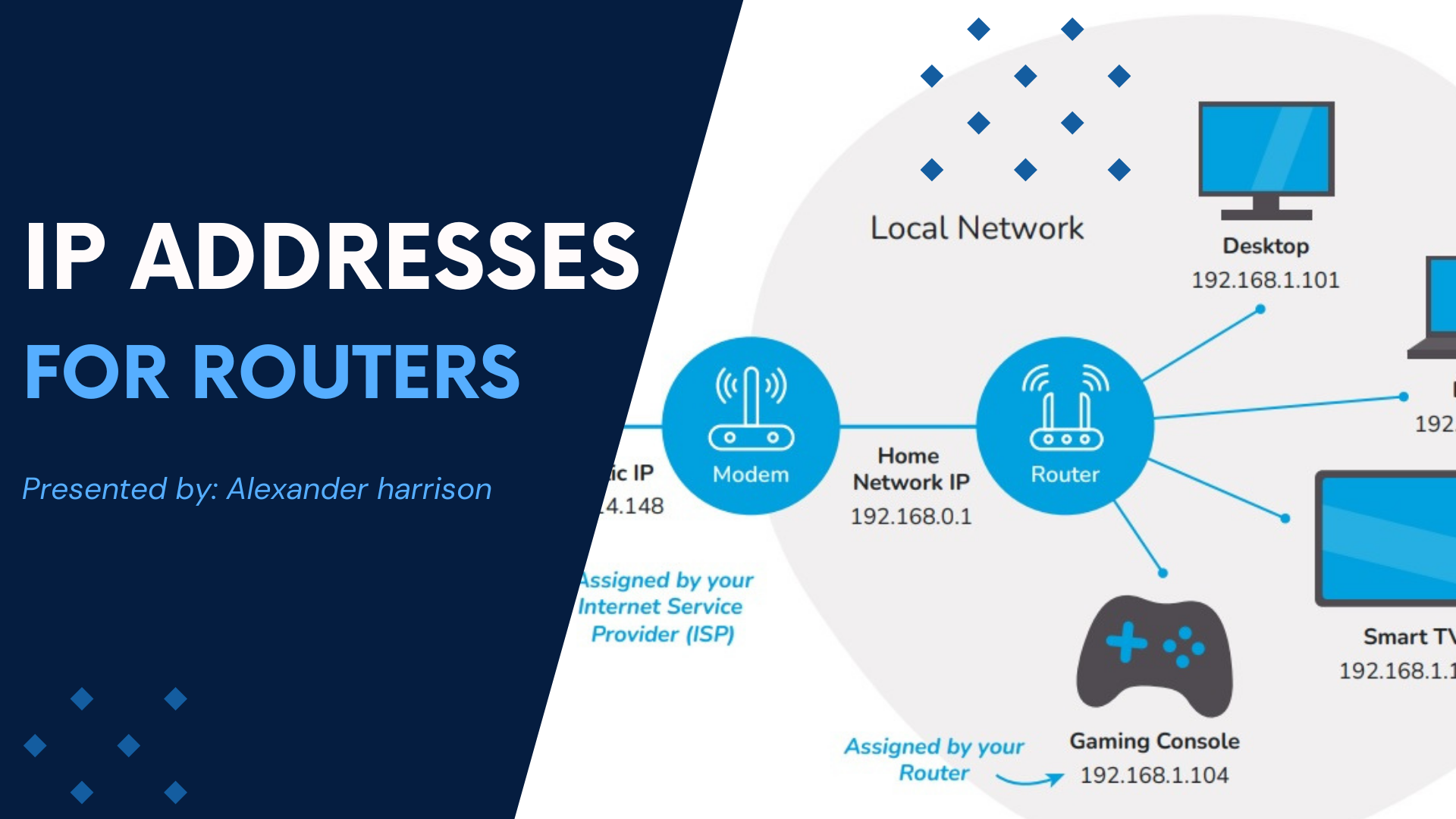
Understanding IP Addresses for Routers
In today’s digital world, the Internet is our lifeline. A vital piece of its infrastructure is the IP address. Picture sending a letter without an address; chaos would reign. Just like that, IP addresses guide data packets to their rightful destinations. This article dives into the essentials of IP addresses for routers. We’ll unpack their...

Exploring Ring Network: A Journey from Token Passing to Modern Applications
Imagine a group of friends passing a ball around in a circle. Each person receives the ball, does something with it, and then passes it to the next person. This simple idea mirrors the basic principle of a ring network in computer science. A ring network is a type of network topology where devices are...

Choosing the Best Proxy Server Location
In today’s digital age, the term “proxy server” is often discussed. It’s key to privacy, internet freedom, and better web browsing. A proxy is, at its core, an intermediary. It sits between your device and the internet. Its benefits depend on the server’s location and functionality. Choosing the right proxy server location is vital for...
The Future of ASP.Net Hosting: Trends and Innovations to Watch
Explore the future of ASP.Net hosting by delving into the latest trends and innovations shaping the industry. From enhanced security measures to improved scalability and performance, this guide covers the cutting-edge technologies and strategies that will define ASP.Net hosting in the coming years. Stay ahead of the curve and ensure your hosting solutions are future-proof with insights into emerging developments and best practices.

Revolutionizing Your Business’s Internet Usage
Internet Usage, feature of people’s modern and personal professional lives. The threshold has long been crossed where businesses are making the most online tools, to the point where now it is possible for businesses to operate only in a digital capacity. Your business might not go quite that far, but it’s an interesting thought experiment...

An error occurred while preparing the installation of macOS Sierra
Installing macOS Sierra is exciting. The update brings new features and improvements. But you might see, “An error occurred while preparing the installation.” This sounds serious, but it’s not. With the right steps and patience, you can fix it. Some troubleshooting gets you back on track to enjoy your new operating system. Understanding the Problem...