
Technology
AI, cloud computing, blockchain, and emerging technologies shaping the IT landscape.

How to Choose a Gaming Laptop: Expert Tips for the Best Pick
Discover essential strategies for selecting a gaming laptop that boosts your play with key specs and expert advice.

Best Smartwatches for Fitness: Expert Picks and Features
Discover top smartwatches that enhance fitness tracking with key features and expert insights for optimal health gains.

Common Cyber Threats in 2026: Risks and Defenses
Explore the top cyber threats of 2023, backed by data from Verizon and IBM, with expert insights and practical mitigation strategies to protect your digital assets effectively.

AI Ethics and Challenges: Key Issues and Solutions
Explore AI ethics principles, historical evolution, major challenges like bias and privacy, and practical strategies to build responsible AI systems for a fairer future.

How to Build a Simple AI Model: Step-by-Step Guide
Discover a practical guide to building simple AI models with Python tools, real examples, and expert tips to avoid common pitfalls and achieve quick results.

Top AI Tools for Beginners: Essential Guide 2026
Discover beginner-friendly AI tools like ChatGPT and Teachable Machine to kickstart your journey with practical guides and expert insights for easy adoption.

How to Set Up Two-Factor Authentication: Complete Guide
Discover step-by-step instructions to enable two-factor authentication on email, social media, and banking apps. Boost your security with expert tips and stats to prevent breaches effectively.
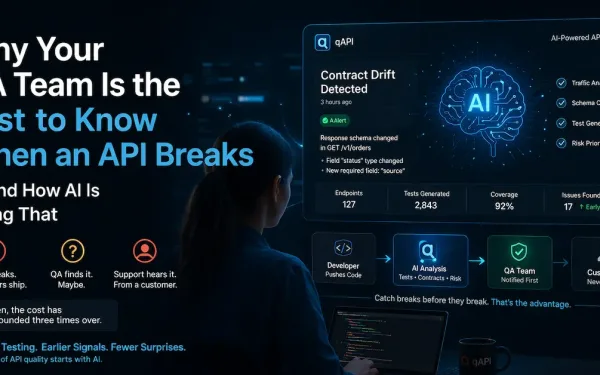
Why Your QA Team Is the Last to Know When an API Breaks — And How AI Is Fixing That
There’s a pattern most engineering teams know but nobody likes to say out loud. The API breaks. The developer who shipped it doesn’t notice. The QA team finds it — maybe. The support team definitely finds it, because a customer told them. By then, the cost of that break has compounded three times over. This...

Essential Guide to Gadgets and Hardware Innovations
Discover the evolution, key components, and troubleshooting tips for gadgets and hardware. Gain practical insights to optimize devices and embrace future trends for enhanced daily efficiency.

Mastering Software Development: Trends, Tools, and Best Practices
Explore the evolution, methodologies, and emerging trends in software development with expert insights, stats, and practical tutorials to boost your skills and efficiency.