Search Results
Showing results for "business" (3533 articles found)

5G fixed wireless access use cases continue to grow
FWA delivers wireless broadband internet to remote regions, temporary setups and other locations not suitable for wired networking. 5G has supercharged its growth.

AI-Powered Route Optimization Tools for Smart Logistics
The world of moving goods is changing fast. In the United States, logistics companies face a tough road every single day. Costs are going up, and traffic in our major cities is getting worse. To stay ahead of the game, businesses are now turning to Route Optimization Tools. These tools use smart technology to find...

Campus Hacks That Grow Your Bank Account: A Guide for National and International Students
As a student, whether national or international, you are probably used to operating on a tight budget. Between tuition, textbooks, food, and socializing with friends and fellow students, it often feels like there isn’t enough money to cover everything that you need and want. However, despite the initial feeling of not having enough, there are...
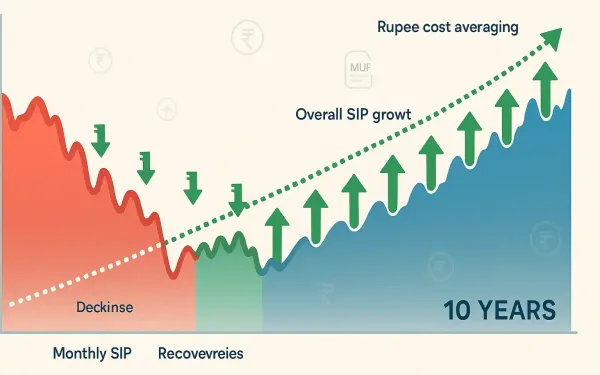
How SIP Returns Change with Market Volatility: A Data-Driven Study
A Systematic Investment Plan, or SIP, allows you to invest a fixed amount of money every month. Many people use SIPs to invest in equity mutual funds. The markets experience price changes that result in upward and downward movements. The price changes that occur in financial markets are referred to as market volatility. When markets...

Enhancing Enterprise Network Security With HTTPS Proxies
How does your team handle visibility when most of your traffic uses TLS? If you work in a large firm, enterprise network security is likely a top priority for your department. Modern threats hide inside encrypted packets, making them hard to find. We often use tools like HTTPS proxies to look inside these streams. But...

The 5 Best Outreach Link-Building Companies in 2026
Link building has gotten pickier. Editors want real value, search engines watch patterns, and buyers want proof that a link did more than look pretty in a report. That is why outreach is back in the spotlight: it is slower than bulk placements, but it tends to hold up better over time. For teams comparing...

9 Quantum-Proof Security Moves Smart Companies Are Making
The digital landscape of 2026 is defined by a silent but accelerating race against time. While quantum computing continues to promise breakthroughs in materials science and pharmacology, it simultaneously poses a fundamental threat to the cryptographic systems that secure the global economy. Most of the encryption currently protecting bank transfers, medical records, and state secrets...

Managed SOC Solutions: 4 Reasons for Real-Time Threat Protection in 2026
The cybersecurity landscape is evolving at an astonishing pace, driven by the relentless advances of technology and the innovative tactics of cyber adversaries. As a consequence, businesses need to be ever more vigilant and proactive in their security approach. Enter the managed SOC solutions, a robust way to counteract the myriad of threats that organisations...

Costing 101: A Contractor’s Guide to Accurate Project Estimates
TL;DR Accurate project costing decides whether you make a profit or face losses. As a contractor, you deal with fluctuating material prices, labour shortages, site delays and compliance costs. A small estimation error can wipe out your margins. If you want predictable profits and better control over cash flow, you need a structured costing system....

Top SaaS SEO Agencies in New York
Which SEO agencies deliver the best results for SaaS companies in New York? New York City has established itself as one of the world’s premier SaaS hubs, with a thriving ecosystem spanning fintech, adtech, enterprise software, legal tech, and media technology. For SaaS companies competing in this high-stakes environment, organic search is a critical growth...