In 1970, the Defense Advanced Research Projects Agency (DARPA) began working to create an open standard network model known as the TCP/IP Model. Subsequently, by 1985, the TCP/IP model started gaining more importance and support from vendors, ultimately replacing the OSI model. The Internet Engineering Task Force (IETF) maintains the TCP/IP model and related protocols.
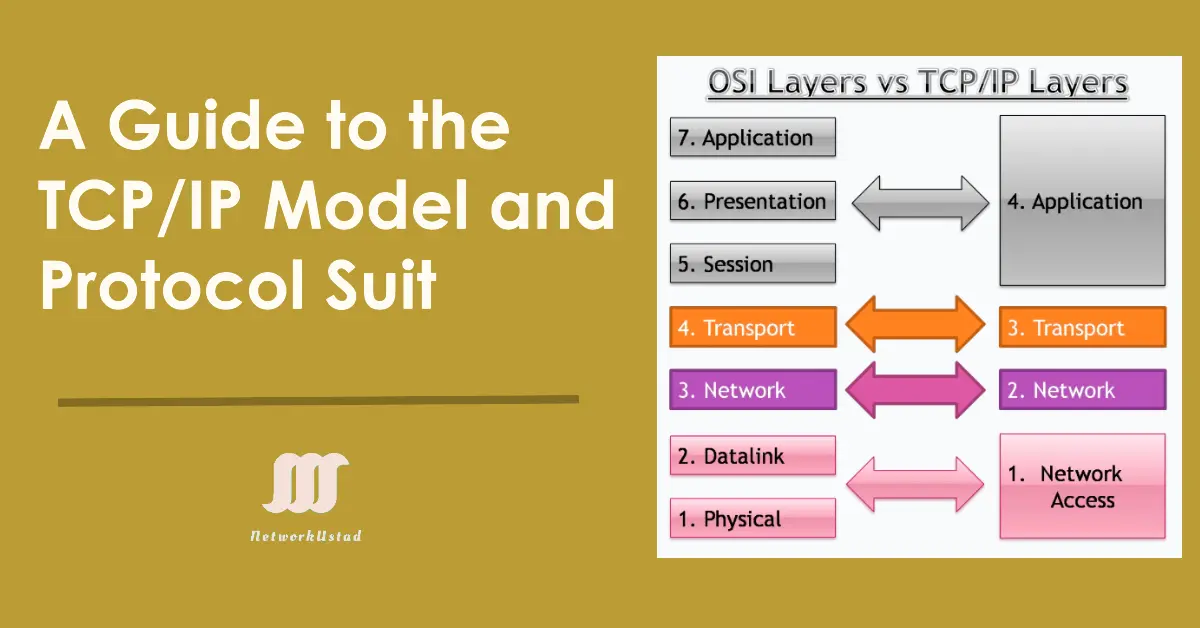
The TCP/IP model was on the development path when the OSI standard was published. The TCP/IP model is not the same as the OSI model. OSI is a seven-layered standard, but TCP/IP is a four-layered standard. The OSI model has been very important in the growth and development of the TCP/IP standard, which is why much OSI terminology is applied to TCP/IP.
Both models are open to standard networking models. However, the TCP/IP model is more accepted today, and the TCP/IP protocol suite is more commonly used. Like the OSI reference model, the TCP/IP model is layered. In this section, we will look at all the TCP/IP model layers and the various protocols used in those layers.
The TCP/IP model is a reduced version of the OSI reference model consisting of the following 4 layers:
- Application Layer
- Transport Layer
- Internet Layer
- Network Access Layer
The functions of these four layers are comparable to the functions of the seven layers of the OSI model. The figure below illustrates the comparison between the layers of the two models.
The following sections discuss the four layers and protocols in those layers in detail.
As we can see, the TCP/IP model does not include presentation and session layers. There is no note that the Network Access Layer in the TCP/IP model combines the functions of the Data Link Layer and Physical Layer.
Application Layer of the TCP/IP model
The application layer is the topmost layer of the TCP/IP model. Located atop the Transport layer, it defines TCP/IP application protocols and outlines how host programs interface with transport layer services to utilize the network.
The Application Layer of the TCP/IP Model encompasses various protocols that perform functions equivalent to those of the OSI model’s Application, Presentation, and Session layers. This layer includes interaction with the application, data translation and encoding, dialogue control, and communication coordination between systems.
Encompassing higher-level protocols such as DNS (Domain Naming System), HTTP (Hypertext Transfer Protocol), Telnet, SSH, FTP (File Transfer Protocol), TFTP (Trivial File Transfer Protocol), SNMP (Simple Network Management Protocol), SMTP (Simple Mail Transfer Protocol), DHCP (Dynamic Host Configuration Protocol), X Windows, RDP (Remote Desktop Protocol), among others, the application layer plays a vital role in network communication. These protocols facilitate diverse functions crucial for effective and seamless network data exchange.
Transport Layer of TCP/IP model
The Transport Layer is the third layer of the TCP/IP model. It is situated between the Application and Internet layers and aims to permit devices on the source and destination hosts to converse. The Transport Layer defines the service level and connection status when transporting data. The main protocols included at the Transport Layer are TCP (Transmission Control Protocol) and UDP (User Datagram Protocol).
The TCP/IP transport layer functions like the OSI transport layer. It is concerned with end-to-end data transportation and establishes a logical connection between the hosts.
TCP is a connection-oriented and reliable protocol that uses windowing to control the flow and provides ordered data delivery in segments. On the other hand, UDP transfers the data without the bells and whistles. Though these two protocols are different in many ways, they do the same function of transferring data and use a concept called port numbers.
Internet Layer of TCP/IP model
Once TCP and UDP have segmented the data and have added their headers, they send the segment down to the Network layer. The destination host may reside in a different network far from the host, divided by multiple routers. The Internet Layer is responsible for ensuring that the segment moves across the networks to the destination network.
The Internet layer packs data into packets known as IP datagrams. These packets contain source and destination address (logical address or IP address) information, which forwards the datagram between hosts and across networks. The Internet layer is also responsible for routing IP datagrams.
Packet switching network depends on a connectionless internetwork layer. This layer is known as the Internet layer. Its job is to allow hosts to insert packets into any network and have them deliver independently to the destination. At the destination side data; packets may seem in a different order than they were sent. The higher layers’ job is to rearrange them to deliver them to proper network applications operating at the Application layer.
The main protocols included at the Internet layer are IP (Internet Protocol), ICMP (Internet Control Message Protocol), ARP (Address Resolution Protocol), RARP (Reverse Address Resolution Protocol), and IGMP (Internet Group Management Protocol).
The Internet layer of the TCP/IP model functions like the Network layer of the OSI reference model. It provides logical addressing, path determination, and forwarding.
Network Access Layer of TCP/IP model
The Network Access Layer is the first layer of the TCP/IP model. It defines details of how data is physically sent through the network, including how bits are electrically or optically signaled by hardware devices that interface directly with a network medium, such as coaxial cable, optical fiber, or twisted pair copper wire. The essential protocols of the Network Access Layer are Ethernet, Token Ring, FDDI, X.25, and Frame Relay.
LAN architecture is the most popular among those listed above Ethernet. Ethernet uses an Access Method called CSMA/CD (Carrier Sense Multiple Access/Collision Detection) to access the media when Ethernet operates in a shared media.
In the CSMA/CD Access Method, every host has equal access to the medium and can place data on the wire when the wire is free from traffic or in an idle position when a host wants to put data on the wire. It will check the wire to determine whether another host uses the medium.
If traffic is already in the medium, the host will wait; if there is no traffic, the data will be placed in the medium. However, if two systems place data on the medium simultaneously, they will collide, destroying the data if it is destroyed during transmission. This data will need to be re-transmitted. After the collision, each host will wait for a small interval, and the data will be re-transmitted again.
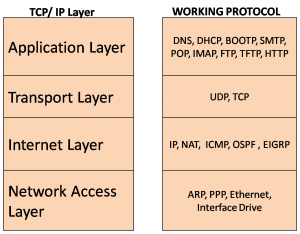
The TCP/IP protocol Suite includes many protocols, as shown in the Figure below. Each layer has its working protocol. Application-layer protocols include the Domain Name System(DNS), host configuration protocols such as Dynamic Host Configuration Protocol (DHCP) and Bootstrap Protocol (BOOTP), Email protocols (POP, SMTP, and IMAP), file transfer protocols, and the HyperText Transfer Protocol. The Transport Layer includes the Transmission Control Protocol (TCP) and User Datagram Protocol (UDP).
The Internet layer working protocols are Internet Protocol (IP), Network Address Translation (NAT), Internet Control Messaging Protocol (ICMP), and routing protocol. The Network Access Layer includes Address Resolution Protocol (ARP), Point to Point Protocol (PPP), Ethernet, and Interface Drives.
The lower-layer protocols in the network access layer deliver the IP packet over the physical medium. Standards organizations, such as IEEE, have developed these protocols.
The Protocol suite is implemented as a TCP/IP stack on both the sending and receiving hosts to provide end-to-end application delivery over a network. The Ethernet protocols transmit the packet over the physical medium used by the LAN.
TCP/IP Communication Process
1. Host-1 sends data using the Hypertext Markup Language (HTML) page to Host-2.
2. The application protocol HTTP header was added to the front of the HTML data, as shown in the figure below. The header has various information, such as the IP header, Ethernet header, TCP header, and the HTTP version the server is using, as well as a status code representing it that has information for the web client.
The application layer protocol HTTP forwards the HTML-formatted web page data to the transport layer (Layer 4 of the OSI Model). The Transport Layer adds a TCP header to the HTTP data and converts it into a segment. In this example, the transport layer handles each conversation between Host-1 and Host-2.
4. Next, the IP information is added to the front of the TCP information and converted to the packet segment. IP assigns the source and destination IP addresses.
5. The Ethernet protocol, known as a data link frame, adds information to both ends of the IP packet. This frame is delivered to the nearest router along the path towards the web client. This router removes the Ethernet information, analyzes the IP packet, determines the best path, inserts the packet into a new frame, and sends it to the next neighboring router towards the destination. Each router removes and adds new data link information before forwarding the packet.
6. This data is transported through the internet through media and intermediary devices.
At the receiving end, the client receives the data link frames that contain the data. Each protocol header is processed and then removed in the opposite order it was added. After eliminating all headers, the user receives and sees the original data, as shown in the figure below.