As the importance of computers grows, vendors recognize the need for networking with them. They produced a variety of protocols whose specifications were not made public. Hence, each vendor had different ways of networking computers, and these ways were not compatible with each other. This means that the computers of one vendor could not be networked with another vendor’s computers. Slowly, these specifications were made public, and some inter-vendor compatibility was created, but this still represented too many complications. To resolve this compatibility issue, the OSI model was introduced.
OSI Model
In 1977, the International Organization for Standardization (ISO) started working on an open standard networking model that all vendors would support to promote interoperability. This standard was published in 1984 and was known as the OSI Model.
The OSI model has been created to support communication between devices of various vendors. It also promotes communication between disparate hosts, such as hosts using different operating platforms. Keep in mind that you are very unlikely to ever work on a system that uses protocols conforming to the OSI model. But it is essential to know the model and its terminology because other models, such as the TCP/IP model often compared to the OSI model. Hence, the discussion on this model is compared to the discussion on the TCP/IP model.
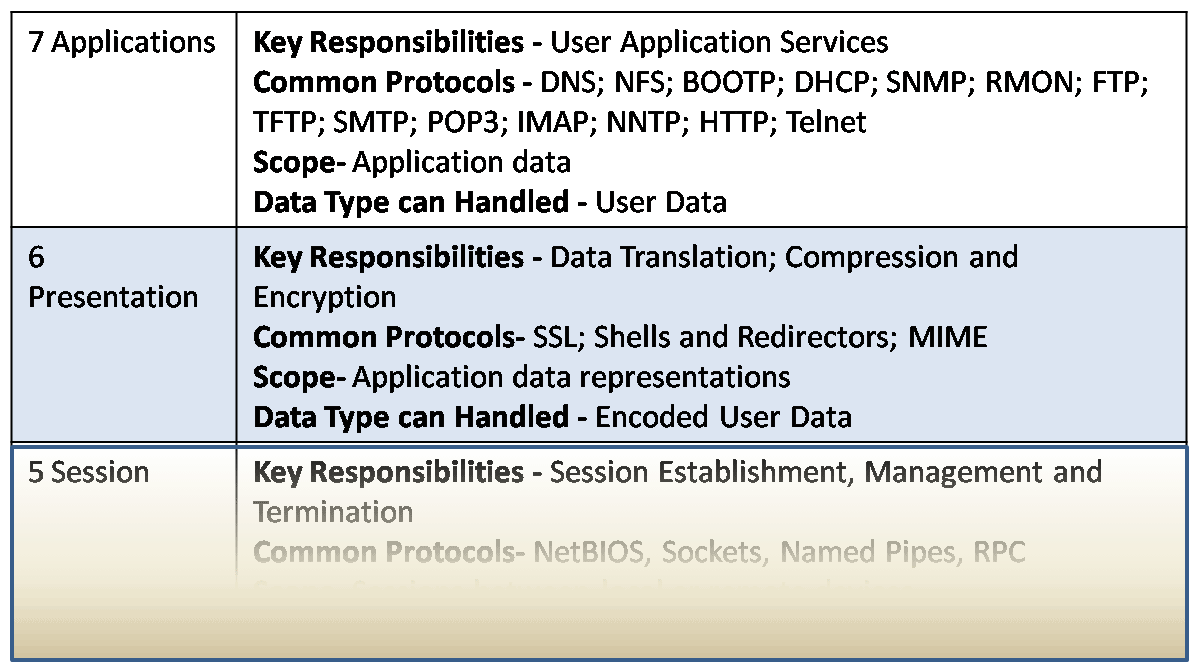
The OSI model, like most other network models, divides the functions, protocols, and devices of a network into various layers. The OSI model has seven such layers that are divided into two groups. The upper layers (Layers 7, 6, and 5) define how applications interact with the host interface, with each other, and with the user. The lower four layers (Layers 4, 3, 2, and 1) define how data is transmitted between hosts in a network. The figure below illustrates the seven layers and a summary of their functions.
The layered approach provides many benefits, some of which are:
- Communication is divided into smaller and simpler components
- Since it is a layered approach, the vendors write to a common input and output specification per layer. The guts of their products function between the input and output code of that layer.
- Changes in one layer do not affect other layers. Hence, development in one layer is not bound by the limitations of other layers. For example, wireless technologies are new, but old applications run seamlessly over them without any changes.
- It is easier to normalize functions when they are divided into smaller parts like this.
It allows various types of hardware and software, both new and old to communicate with each other seamlessly
The following section describes the 7 layers in detail.
Application Layer
This Layer provides an interface between the software application on a system and the network. Remember that this layer does not include the application itself, but provides services that an application requires. One of the easiest ways to understand this layer’s function is to look at how a Web Browser, such as Internet Explorer or Firefox, works in the application.
When it needs to fetch a web page, it uses the HTTP protocol to send the request and receive the page contents. This protocol resides at the application layer used by an application such as IE or FF to get web pages from web servers across the network. On the other side, the web server application, such as Apache or IIS, interacts with the HTTP protocol on the Application layer to receive the HTTP request and send the response back. Read More
Presentation Layer
This layer presents data to the Application layer. The Presentation Layer is also responsible for data translation and encoding. It will take the data from the Application layer and translate it into a generic format for transfer across the network. At the receiving end, the Presentation layer takes in generically formatted data and translates it into the format recognized by the Application layer. An example of this is a JPEG to ASCII translation. The OSI model has protocol standards that define how data should be formatted. This layer is also involved in data compression, decompression, encryption, and decryption.
Session Layer
In a host, different applications or even different instances of the same application might request data from across the network. It is the Sessions layer’s responsibility to keep the data from each session separate. It is responsible for setting up, managing, and tearing down sessions. It also provides dialogue control and coördinates communication between the systems.
Transport Layer
Where the upper layers relate to applications and data within the host, the transport layer is concerned with the real end-to-end transfer of the data across the network. This layer establishes a logical connection between the two communicating hosts, provides reliable or unreliable data delivery, and can give flow control and error recovery. Although not developed under the OSI Model and not strictly conforming to the OSI definition of the Transport Layer, typical examples of Layer 4 are the Transmission Control Protocol (TCP) and User Datagram Protocol (UDP). Read More
Network Layer
To best understand what the Network layer does, consider what happens when you write a letter and use the postal service to send the letter. You put the letter in an envelope and write the destination address as well as your address so that an undelivered letter back to you.
In network terms, this address is a logical address and is unique in the network. Each host has a logical address. When the post office receives this letter. It has to find out the best path for this letter to reach the destination. Similarly, in a network, a router needs to decide the best path to a destination address.
This path determination. Finally, the post office sends the letter out the best path, and it moves from the post office to the post office before finally being delivered to the destination address. Similarly, data is moved across the network mainly by routers before being finally delivered to the destination.
All three functions – logical addressing, path determination, and forwarding – are done at the Network Layer. Two types of protocols are used for these functions – routed protocols for logical addressing and forwarding, and routing protocols for path determination.
There are many routed protocols and routing protocols available. Some of the common ones are discussed in great detail later in the book. Routers function in this layer. Remember that routers only care about the destination network. They do not care about the destination host itself. The task of delivery to the destination host lies on the Data Link Layer. Read More
Data Link Layer
The Network layer deals with data moving across networks using logical addresses. On the other hand, the Data Link layer deals with data moving within a local network using physical addresses. Each host has a logical address and a physical address. The physical address is only locally significant and is not used beyond the network boundaries (across a router).
This layer also defines protocols that send and receive data across the media. You will remember from earlier in the chapter that only a single host can send data at a time in a collision domain, or else packets will collide and cause a host to back off for some time. The Data Link layer determines when the media is ready for the host to send the data and detects collisions and other errors in received data. Switches function in this layer. Read More
Physical Layer
This layer deals with the physical transmission medium itself. It activates, maintains, and deactivates the physical link between systems (host and switch, for example). This is where the connectors, pinouts, cables, and electrical currents are defined. Essentially, this layer puts the data on the physical media as bits and receives it in the same way. Hubs work at this layer. Read More
FAQs
What led to the development of the OSI model, and why was it needed?
The OSI model was developed due to the incompatibility of networking protocols among different vendors. It aimed to create a standardized framework for networking that could promote interoperability.
How does the OSI model function regarding its seven layers?
The OSI model divides network functions, protocols, and devices into seven layers, each with its specific purpose. The upper layers (7, 6, and 5) focus on how applications interact, while the lower layers (4, 3, 2, and 1) handle data transmission.
What are the key benefits of using a layered approach in the OSI model?
The layered approach offers multiple advantages, including simplified communication components, easy normalization, the ability to update one layer independently, and seamless compatibility between various hardware and software.
What is the role of the Application Layer in the OSI model, and how does it support software applications?
The Application Layer acts as an interface between software applications and the network. It provides necessary services for applications, such as using the HTTP protocol for web browsing.
How does the Presentation Layer function, and what are its responsibilities?
The Presentation Layer translates data into a generic format for network transfer and handles data translation, encoding, compression, decompression, encryption, and decryption.
What does the Session Layer do in a network, and how does it manage data from different applications or instances?
The Session Layer keeps data from various sessions separate and manages the setup, maintenance, and termination of sessions while providing dialogue control and coordinating communication between systems.
Could you explain the purpose and functions of the Transport Layer in the OSI model?
The Transport Layer manages end-to-end data transfer across the network, establishing logical connections, providing reliable or unreliable data delivery, and offering flow control and error recovery.
What does the Network Layer handle, and how does it relate to logical addressing, path determination, and data forwarding?
The Network Layer manages logical addressing, path determination, and data forwarding. It ensures data reaches the correct destination, like the postal service delivering a letter.
What role does the Data Link Layer play in network data transmission, and how does it work with physical and logical addresses?
The Data Link Layer deals with data transmission within a local network, using physical addresses for devices. It also determines when the media is ready for data transmission and detects collisions and errors.
How does the Physical Layer function, and what networking aspects does it define and control?
The Physical Layer manages the physical transmission medium, including connectors, cables, and electrical currents. It activates, maintains, and deactivates the physical link between systems.
Before going to the next lessons, take your self-assessment with our free quiz test using the following links.
Quiz 3 Basic Network Component CCNA (200-301)
Quiz Comparing Switch and Router – CCNA (200-301)
Quiz: What is a Network – CCNA (200-301)
Types of Network Self-Assessment Quiz CCNA
Quiz OSI Model, including its 7 layers CCNA