Subnetting involves a trade-off: borrowing more host bits increases subnets but reduces hosts per subnet. For example, a /16 network with 16 host bits can be subnetted to /22 (64 subnets, 1022 hosts) or /28 (4096 subnets, 14 hosts), guiding network design as of June 2025.
We consider either the host requirement or the network requirement for subnetting. The table below displays the details for subnetting a /16 network. You can examine how there is an opposite relationship between the number of hosts and the number of subnets.
| Prefix Length | Subnet Mask | Subnet in Binary | Available Networks | Usable Hosts per Network |
|---|---|---|---|---|
| /17 | 255.255.128.0 | NNNNNNNN.NNNNNNNN.nHHHHHHH.HHHHHHHH 11111111.11111111.10000000.00000000 | 2¹ = 2 | 2¹⁵ − 2 = 32,766 |
| /18 | 255.255.192.0 | NNNNNNNN.NNNNNNNN.nnHHHHHH.HHHHHHHH 11111111.11111111.11000000.00000000 | 2² = 4 | 2¹⁴ − 2 = 16,382 |
| /19 | 255.255.224.0 | NNNNNNNN.NNNNNNNN.nnnHHHHH.HHHHHHHH 11111111.11111111.11100000.00000000 | 2³ = 8 | 2¹³ − 2 = 8,190 |
| /20 | 255.255.240.0 | NNNNNNNN.NNNNNNNN.nnnnHHHH.HHHHHHHH 11111111.11111111.11110000.00000000 | 2⁴ = 16 | 2¹² − 2 = 4,094 |
| /21 | 255.255.248.0 | NNNNNNNN.NNNNNNNN.nnnnnHHH.HHHHHHHH 11111111.11111111.11111000.00000000 | 2⁵ = 32 | 2¹¹ − 2 = 2,046 |
| /22 | 255.255.252.0 | NNNNNNNN.NNNNNNNN.nnnnnnHH.HHHHHHHH 11111111.11111111.11111100.00000000 | 2⁶ = 64 | 2¹⁰ − 2 = 1,022 |
| /23 | 255.255.254.0 | NNNNNNNN.NNNNNNNN.nnnnnnnH.HHHHHHHH 11111111.11111111.11111110.00000000 | 2⁷ = 128 | 2⁹ − 2 = 510 |
| /24 | 255.255.255.0 | NNNNNNNN.NNNNNNNN.nnnnnnnn.HHHHHHHH 11111111.11111111.11111111.00000000 | 2⁸ = 256 | 2⁸ − 2 = 254 |
| /25 | 255.255.255.128 | NNNNNNNN.NNNNNNNN.nnnnnnnn.nHHHHHHH 11111111.11111111.11111111.10000000 | 2⁹ = 512 | 2⁷ − 2 = 126 |
| /26 | 255.255.255.192 | NNNNNNNN.NNNNNNNN.nnnnnnnn.nnHHHHHH 11111111.11111111.11111111.11000000 | 2¹⁰ = 1,024 | 2⁶ − 2 = 62 |
| /27 | 255.255.255.224 | NNNNNNNN.NNNNNNNN.nnnnnnnn.nnnHHHHH 11111111.11111111.11111111.11100000 | 2¹¹ = 2,048 | 2⁵ − 2 = 30 |
| /28 | 255.255.255.240 | NNNNNNNN.NNNNNNNN.nnnnnnnn.nnnnHHHH 11111111.11111111.11111111.11110000 | 2¹² = 4,096 | 2⁴ − 2 = 14 |
| /29 | 255.255.255.248 | NNNNNNNN.NNNNNNNN.nnnnnnnn.nnnnnHHH 11111111.11111111.11111111.11111000 | 2¹³ = 8,192 | 2³ − 2 = 6 |
In this lesson, we will discuss subnetting based on the host requirement. We will jump right into the examples for better understanding. The examples we will be talking about will seem to be the same as the ones we did in the earlier lesson, but there is a most important twist that makes them special.
Let’s suppose we have purchased the address 192.168.100.0 with the subnet mask 255.255.255.0 and are required to break that address into 62 hosts per network. The number of hosts required in the subnet will determine how many bits must be left in the host portion. Remember that two of the addresses cannot be used, so the usable number of addresses can be calculated as 2h-2. Unlike network-based subnetting, host-based subnetting starts with the required hosts (e.g., 62) to determine the mask, focusing on right-to-left bit allocation.
Convert the number of hosts to binary
Required Host – 62 (So convert 64 into binary)
62 = 111110
Reserve bits in the subnet mask and find the increment
S, we need 6 bits in the host portion of the address. The difference is that we convert the number of hosts per network back to binary instead of the number of networks. We already learned that “1s” represent the network and 0s represent the hosts in the subnet mask. Also, remember we are still subnetting and focusing on the host rather than the network requirement. So, the binary of 62 takes up to 6 bits, right? Now, examine the default subnet mask before subnetting and the subnet mask after adding ones in the places of borrowed bits position places.
255.255.255.0=11111111.11111111.11111111.00000000
255.255.255.192=11111111.11111111.11111111.110000000
So, the new subnet mask is 255.255.255.192 or /26. So, 62 hosts need 6 bits in the host portion. Also, note that instead of going from left to right as we did with the network requirements, I went from right to left because that’s where my 0s exist. We know that we can get 30 hosts per sub-network.
Use the increment to find the network ranges.
Our focus is just on the 0s in subnetting, on the host requirement-based. So, let’s now find the network ranges. Our increment is 64 because the lowest network bit converted back to a decimal number is 64.
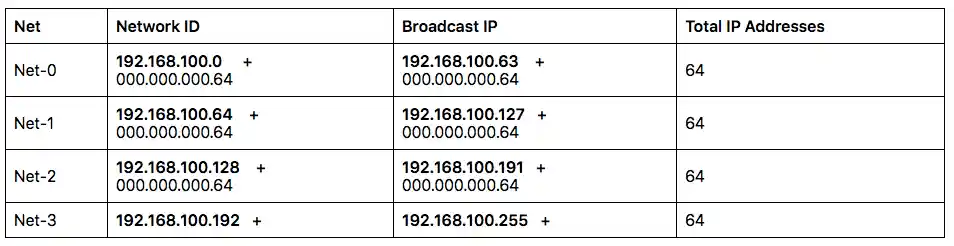
We know that the first and last addresses of each sub-network aren’t usable, so we have exactly 62 usable hosts per network.
Conclusion – Subnetting on host requirements
The exploration of subnetting based on host requirements offers a practical approach to designing efficient and scalable networks, tailored to the specific needs of devices rather than just network segmentation. By prioritizing host counts—such as achieving 62 usable addresses per subnet with a /26 mask—network administrators can optimize address allocation while maintaining performance, a critical skill for CCNA and CCNP professionals.
The trade-off between host capacity and subnet numbers underscores the importance of careful planning, especially as networks evolve toward IPv6 adoption as of June 30, 2025. Leveraging tools like Cisco IOS commands (ip subnet-zero, show ip interface brief) and techniques such as VLSM ensure flexibility and accuracy. Best practices, including verifying ranges and avoiding overlaps, empower administrators to build robust infrastructures that meet current demands and anticipate future growth.
FAQs
What is host-based subnetting and how does it differ from network-based subnetting?
Host-based subnetting prioritizes the number of hosts per subnet (e.g., 62 with a /26 mask) by determining the required host bits, while network-based subnetting focuses on the number of subnets, adjusting host capacity accordingly—a key distinction for CCNA learners.
How do I calculate the subnet mask for 62 hosts on a /24 network?
Calculate 2^h-2 ≥ 62, requiring 6 host bits (2^6-2 = 62), resulting in a /26 mask (255.255.255.192), a fundamental skill for subnetting as of June 30, 2025.
What is the trade-off when subnetting based on host requirements?
More host bits increase the number of addresses per subnet (e.g., 126 with /25) but reduce the number of subnets (e.g., 2), requiring a balance for efficient network design.
How can VLSM enhance host-based subnetting in large networks?
VLSM allows variable subnet sizes (e.g., /26 for 62 hosts, /28 for 14 hosts) within a single network, optimizing address use and supporting complex CCNP designs as of June 2025
What Cisco IOS commands can verify host-based subnet configurations?
Use show ip interface brief to check assigned IPs and ip subnet-zero to enable all-zero subnets, ensuring accurate host allocation on routers.
How does host-based subnetting apply to IPv6 networks?
IPv6 uses fixed /64 subnets with 18 quintillion host addresses, adapting host-based concepts to allocate large host pools, relevant to modern networks.
What are common pitfalls to avoid in host-based subnetting?
Avoid insufficient host bits (e.g., /27 for 62 hosts) or overlapping subnets; troubleshoot with show running-config to correct misconfigurations effectively.