Every spanning tree switched network or broadcast domain has a switch designated as the root bridge. It serves as the reference point for all spanning-tree-enabled switches. The spanning tree algorithm determines which redundant paths to block. It is selected as an election process.
The figure below illustrates the bridge ID (BID) fields. BID is a unique identity when the switch is part of a network. It is a 64-bit field divided into three parts: the 4 4-bit Bridge Priority field, the 12 12-bit Extended System ID field, and the switch’s 48-bit MAC address. The Bridge Priority field is configurable, while the MAC address is unique among all switches. The sum of these two ensures a unique Bridge ID.
Root Bridge election
When switches boot, they all assume they are the root and start sending configuration BPDUs every 2 seconds (Hello Time). Each BPDU contains the sender’s Bridge ID and the Root ID it currently believes is the best. The adjacent switches receive the BPDU frames and read the root ID information from them. If the root ID of the BPDU sending switch is lower than the root ID on the receiving switch, the receiving switch updates its root ID, identifying the adjacent switch as the root bridge.
It doesn’t need to be the adjacent switch. It could be any other switch in the broadcast domain. The switch then sends new BPDU frames with the lower root ID to the adjacent switches. Finally, the switch with the lowest BID is selected as the root bridge for the spanning tree instance.
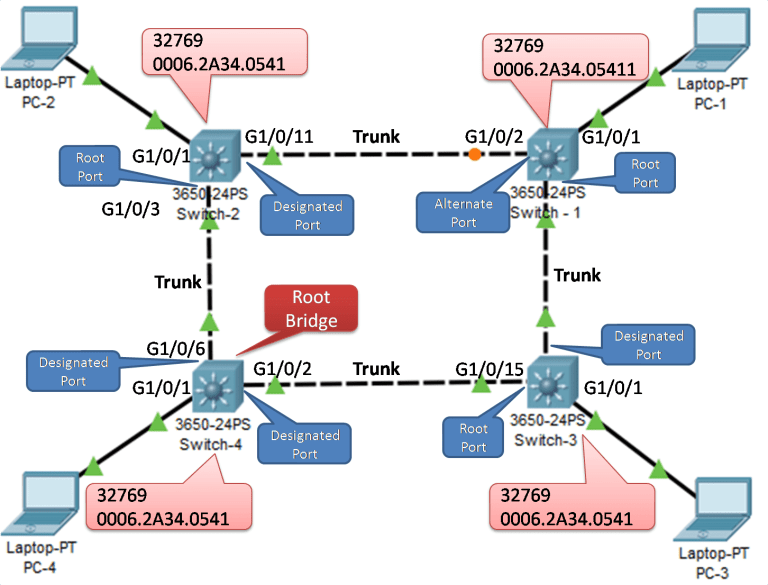
Now, look at the election process from another angle. Before manually configuring the bridge priority, all the switches have a default priority. Therefore, it is a tie based on priority. The switch with the lowest MAC address will become a root bridge. In the figure below, switch-3 is elected as the Root-Bridge because the bridge priority ID is the default, which is 32769; so, the switches elect the root-bridge based on the MAC address. The switch-3 is the lowest MAC address, so all the root-bridge ports become in the forwarding state, i.e., designated ports.
Root Bridge Behavior in Modern STP Variants
| Feature | Classic STP (802.1D) | RSTP (802.1w) | MSTP (802.1s) |
|---|---|---|---|
| Root Election Logic | Same BPDU comparison | Fully backward compatible | Same logic, multiple instances |
| Convergence Time | 30-50 seconds | Less than 6 seconds | Depends on instance mapping |
| Typical Use | Legacy networks | Most modern campuses | Large environments with many VLANs |
| CCNA/CCNP Focus | Election & port states | Port roles & proposal/agreement | Instance-to-VLAN mapping |
Use MSTP when you want multiple spanning-tree instances to achieve VLAN load balancing across uplinks.
FAQs
What is a root bridge in Spanning Tree Protocol?
The root bridge is the elected reference switch in an STP-enabled network or broadcast domain. It serves as the central point for path calculations, ensuring redundant links are blocked to prevent loops. All other switches direct traffic toward it via root ports.
How does the STP root bridge election process work?
Switches boot and send BPDU frames every 2 seconds with their Bridge ID. Receivers compare root IDs; the lowest wins and propagates. Ties at default priority (32768) break by lowest MAC address, electing the root for the topology.
What components make up the Bridge ID for root election?
Bridge ID is 64 bits: 16-bit configurable priority (default 32768), 16-bit extended system ID (for VLANs in PVST+), and 48-bit MAC address. Priority decides first; MAC breaks ties, ensuring unique root selection in Cisco networks.
Why is manual configuration of the root bridge recommended?
Default election relies on MAC addresses, often placing the root on access switches, causing suboptimal paths and higher latency. Manually set lower priority on core switches for efficient traffic flow and better LAN performance in CCNA labs.
What happens to ports on the root bridge after election?
All root bridge ports become designated ports in forwarding state, allowing full traffic flow. No blocking occurs on the root, as it has no root port itself. This ensures it’s the optimal hub for spanning tree calculations.
About This Content
FAQs
-
Enable BPDU Guard on edge ports and use root guard on critical switches.