Yasir Ali
Yasir Ali is a technology product reviewer with 9 years of hands-on experience testing networking equipment and consumer electronics. Certified in ITIL with a degree in Electrical Engineering. Has evaluated 400+ products.Complementing his technical skills, Yasir earned an MBA from the Virtual University of Pakistan, equipping him with valuable insights into business strategy, leadership, and management. This blend of expertise allows him to tackle IT challenges with both technical precision and strategic vision. As a regular contributor to NetworkUstad.com, Yasir writes clear, engaging blogs on Cisco certifications, networking essentials, cybersecurity, and emerging technologies. His approachable style inspires thousands of aspiring IT professionals, making complex topics accessible and empowering the next generation of network engineers.

The Digital Backbone of Modern Manufacturing: How Swiss Precision Powers Industry 4.0
Manufacturing’s Fourth Revolution and the Rise of Ultra-Precision Machining The narrative of modern manufacturing is one of relentless evolution—from mechanization and mass production to automation and, now, the era of smart, connected factories known as Industry 4.0. While discussions of this fourth industrial revolution often center on big data, artificial intelligence, and IoT sensors, a...
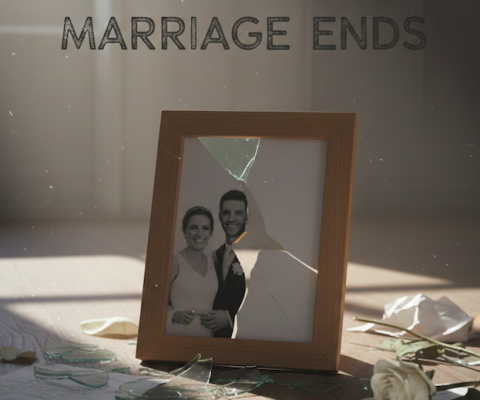
Understanding Divorce Proceedings: What to Expect When Marriage Ends
Divorce represents one of life’s most challenging transitions, affecting not just the couple involved but often children, extended family, and financial futures. Understanding the legal process can help individuals navigate this difficult period with greater confidence and clarity. The Legal Framework of Divorce Every state maintains its own divorce laws, creating significant variations in how...

The Hidden Costs of Data Loss: How Professional Backup and Recovery Services Save Businesses in 2026
Data loss is one of the most disruptive events a business can experience. Whether caused by hardware failure, cyberattacks, human error, or system crashes, losing access to essential files can halt operations instantly. Customer records, financial data, internal documents, and proprietary systems are critical to daily workflows, and when they disappear, productivity and trust are...

How a Boat GPS Improves Trip Planning and Route Accuracy
Planning a boating trip involves more than choosing a destination. Safe and enjoyable trips depend on knowing where you are going, how long it will take, and what conditions you may encounter along the way. Without accurate navigation, even familiar routes can become stressful or risky, especially when conditions change. For Australian boaters navigating rivers,...

Bitcoin Investing in 2026 Expert Insights on the Crypto Market in France
Bitcoin Investing in 2026: The French Perspective As the world of cryptocurrency continues to evolve, platforms like Arbitrox are part of a broader ecosystem where Bitcoin remains at the forefront of the digital financial revolution. Looking ahead to 2026, investors and market observers are increasingly focused on what the future holds for Bitcoin, particularly within...

Understanding Your True Earning Potential: The Power of Modern Salary Calculators
Salary Calculators In today’s complex economic landscape, understanding your actual take-home pay has never been more important. Whether you’re negotiating a new job offer, planning a career move, or simply trying to budget effectively, knowing the difference between your gross salary and what actually lands in your bank account is crucial. This is where advanced...

Why AI Apps Fail Without Strong UX and the Strategic Shift Business Leaders Must Make
AI adoption continues to accelerate across enterprises, yet a large share of AI-powered applications fail to reach sustained usage. Organizations invest heavily in AI app development, but many products struggle to justify the AI app development cost after launch. The issue rarely stems from weak models or infrastructure. It stems from poor UI UX design...

Solar Panel Recycling: The Essential Path to a Truly Sustainable Energy Future
Solar Panel Recycling is becoming one of the most important conversations in renewable energy as solar power adoption accelerates worldwide. Solar Panel Recycling sits at the intersection of clean energy innovation and responsible waste management, ensuring that the environmental promise of solar power does not create a hidden waste crisis decades down the line. As...

How Often Should You Change Your Oil?
Regular oil changes are one of the most important maintenance tasks for keeping your vehicle in top condition. Engine oil lubricates moving parts, reduces friction, prevents overheating, and protects vital components from wear. Many drivers often ask, how often should I change my oil? Typically, most modern vehicles need an oil change every 5,000–10,000 miles,...

3 Types of Effective Muscle Pain Relievers You Should Know About
As people grow older, everyday movement may feel different, especially when muscle stiffness or general soreness becomes more common, yet many still stay active with the right support. Simple activities like getting out of bed, climbing stairs, or reaching for items may feel harder than they once did. Choosing the right muscle pain reliever plays...