
Preventing Ransomware Through Secure Remote Access Design
Ransomware has become one of the most damaging cyber threats facing organizations today. With remote work and cloud-based operations becoming standard, attackers increasingly exploit weak remote access points to infiltrate business networks. Without proper security design, remote connections can quickly turn into costly vulnerabilities. Building a secure remote access infrastructure is now essential for protecting sensitive data, maintaining business continuity, and preventing ransomware-driven disruptions. Understanding How Ransomware Exploits Remote Access Remote access technologies allow employees and administrators to connect to systems from anywhere. While this flexibility supports business continuity, it also introduces new attack surfaces if security controls are weak….

Amazon A+ Content Mastery: Proven Strategies to Drive Sales & Build Customer Loyalty in 2026
Amazon hosts over 9.7 million sellers in 2026. Competition for customer attention has never been fiercer. Basic product listings no longer cut it. Sellers now rely on Amazon A+ Content Services to stand out in crowded categories and hold buyer attention longer. A+ Content gives listings a clear edge. It turns plain product pages into visual stories that guide decisions. This guide shares proven strategies for creating high-converting A+ Content. It highlights methods that support sales growth while strengthening buyer trust. Common mistakes are also covered to help avoid costly missteps. These strategies work for startups and established brands alike….

Understanding the CIA Triad: Confidentiality, Integrity, and Availability
Every day, billions of pieces of data travel across networks worldwide—from personal emails and banking transactions to corporate secrets and government intelligence. But what keeps this information safe? What prevents hackers from reading your private messages, altering your bank balance, or shutting down critical systems? The answer lies in three fundamental principles that form the backbone of information security: the CIA Triad. No, we’re not talking about the Central Intelligence Agency. In cybersecurity, CIA stands for Confidentiality, Integrity, and Availability—three pillars that protect information from unauthorized access, tampering, and disruption. Whether you’re a business owner, IT professional, or someone concerned…
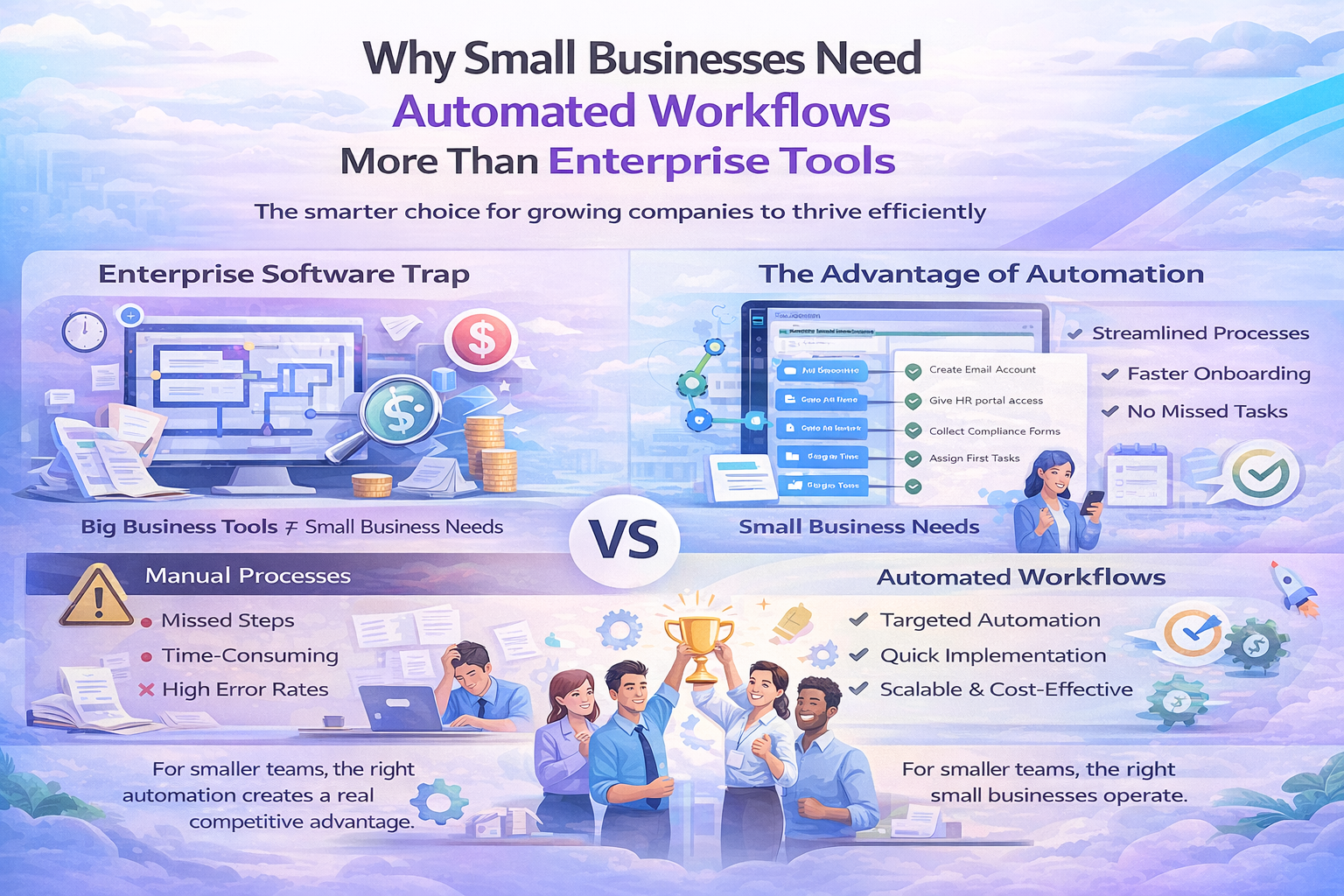
Why Small Businesses Need Automated Workflows More Than Enterprise Tools
There’s a pattern that repeats across growing companies. They hit a point where manual processes start breaking. Tasks get missed. Information lives in too many places. People spend more time coordinating than actually working. The instinct is to buy enterprise software. Big platforms with endless features that promise to solve everything. It rarely works out that way. The enterprise software trap Large-scale business tools are built for large-scale businesses. They assume you have dedicated IT staff, months for implementation, and budgets that match Fortune 500 companies. When a 30-person company tries to adopt these systems, the mismatch becomes obvious fast….

EazeeSign Launches to Simplify Digital Signature Online with User-Friendly Platform
The solution enables businesses and individuals to sign documents securely from anywhere. New Delhi, Delhi, India, January 2026 – Small businesses and remote teams need a way to finalize agreements quickly without the delays of printers or scanners. EazeeSign is launching now to fix the slow paperwork process that holds people back from finishing their work. The current shift toward remote operations demands tools that are fast and reliable. Paperwork usually slows down business. You print a file. You sign it with a pen. You scan it back to a computer. This old method takes too much time. It wastes…
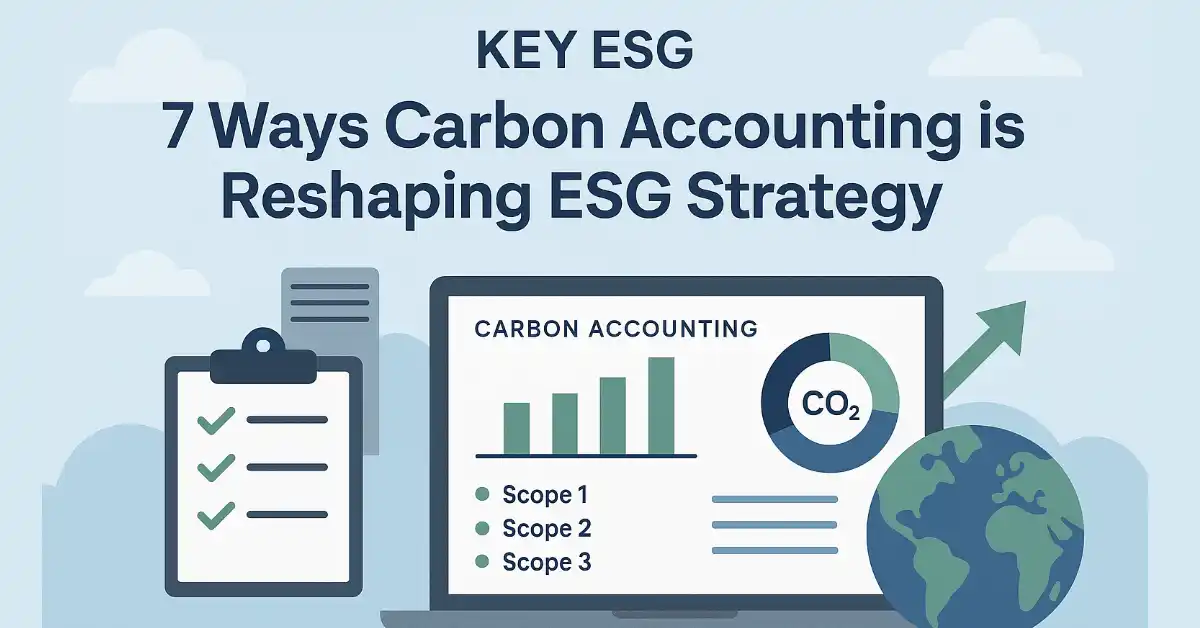
7 Ways Carbon Accounting Is Transforming ESG Strategy for Tech Companies
Carbon accounting has become a core requirement for tech companies facing increasing ESG scrutiny from regulators, investors, and customers. As digital infrastructure scales, so does the complexity of tracking and managing emissions across operations and value chains. Platforms like KEY ESG enable tech companies to take a data-driven approach to carbon accounting by centralizing emissions data, supporting Scope 1, 2, and 3 measurement, and aligning reporting with leading regulatory frameworks. With accurate, auditable data in place, carbon accounting moves beyond compliance and becomes a strategic driver of ESG performance. Below are seven ways carbon accounting is reshaping ESG strategy across…

Securing Digital Content Marketplaces: Lessons From Network Automation Tools
Digital content marketplaces have become integral to today’s economy, offering platforms for creators and consumers alike to exchange digital goods. As these marketplaces grow, so do the security challenges they face. Securing these platforms against cyber threats requires innovative solutions, one of which is the application of network automation tools. These tools not only streamline operations but also enhance security protocols, drawing lessons from their use in various sectors. Understanding the intricacies of these tools and their applications can significantly bolster the defense mechanisms of digital content platforms. The Mileage Tracking space includes platforms like mileage tracker that serve this…

Renewable Energy Systems: How Modern Technologies Are Powering a Sustainable Future
Energy needs are growing across homes, businesses and industries. At the same time, concerns about climate change, fuel costs and long-term availability of resources are becoming harder to ignore. This has led to a clear shift in how power is produced and consumed. Instead of relying only on conventional sources, many organisations and governments are turning to cleaner alternatives. At the centre of this shift are renewable energy systems. These systems use natural sources like sunlight and wind to generate power in a more responsible way. What makes them truly effective today is not just the energy source, but the…

The Ultimate Guide to Building a Remote Team with Latam Developer
Remote work has completely changed how tech teams come together and grow, especially on a global scale. If you’re in charge of hiring, quality and efficiency are always top of mind — but finding great people without blowing up your budget is still a serious challenge. That’s where Latam developers come in. They bring real technical chops, work in time zones that actually overlap with the U.S., and don’t cost a fortune. Latin America’s tech scene has exploded lately, too. There are way more remote-ready pros than there were just a few years ago, and the region is now a real player…

Bonus Stocks List That can Add Extra Value to Your Portfolio
If you spend any time tracking the stock market, you will eventually hear people talk about bonus shares. Someone mentions a bonus announcement, another shares a bonus stocks list, and suddenly there is curiosity around what it actually means for you as an investor. At the same time, you may also notice chatter around other events like an upcoming IPO this week, which adds to the noise. This article is here to slow things down and explain bonus stocks in a clear, friendly way. You will understand what bonus shares are, why companies issue them, how a bonus stocks list…

Understanding Your True Earning Potential: The Power of Modern Salary Calculators
Salary Calculators In today’s complex economic landscape, understanding your actual take-home pay has never been more important. Whether you’re negotiating a new job offer, planning a career move, or simply trying to budget effectively, knowing the difference between your gross salary and what actually lands in your bank account is crucial. This is where advanced salary calculation tools have become indispensable for professionals worldwide. The Gap Between Gross and Net salaries When you receive a job offer stating an annual salary of $80,000 or €60,000, that figure rarely reflects what you’ll actually receive. Taxes, social security contributions, health insurance premiums,…

Why AI Apps Fail Without Strong UX and the Strategic Shift Business Leaders Must Make
AI adoption continues to accelerate across enterprises, yet a large share of AI-powered applications fail to reach sustained usage. Organizations invest heavily in AI app development, but many products struggle to justify the AI app development cost after launch. The issue rarely stems from weak models or infrastructure. It stems from poor UI UX design that fails to translate intelligence into usable value. B2B users evaluate AI applications through interaction, not algorithms. When interfaces confuse users or disrupt workflows, adoption drops regardless of technical sophistication. For founders and technology leaders, UX now plays a direct role in ROI. Without strong…

Digital Transformations in Logistics in 2026
Logistics usually does its job quietly. When deliveries arrive on time and shelves stay stocked, no one gives it much thought. Packages arrive, shelves stay stocked, factories keep buzzing. This year is changing that. Suddenly, logistics is center stage. Every kind of company—factories, retailers, importers—leans hard on digital logistics now. It’s the only way to handle messy supply chains, climbing costs, and one disruption after another. This isn’t about looking cool or chasing the latest tech. It’s survival. The old ways just don’t cut it anymore. Supply chains are too fragile now, and honestly, the days of juggling endless phone…

Password Tool Features That Support Regulatory Accountability
Ensuring regulatory accountability is one of the top priorities for organizations working with sensitive data. Password tools are a valuable support in different sectors. Reliable password management solutions aid organizations in their ability to follow existing policies, as they come with features to meet security needs, access controls, and an audit trail. This article discusses these features for businesses to fulfill their responsibilities and keep private data secure. Strong Encryption for Data Protection Your passwords remain secured with encryption, which saves them in unreadable formats, making it difficult for an unauthorized user to gain access. Many regulators compel organizations to…
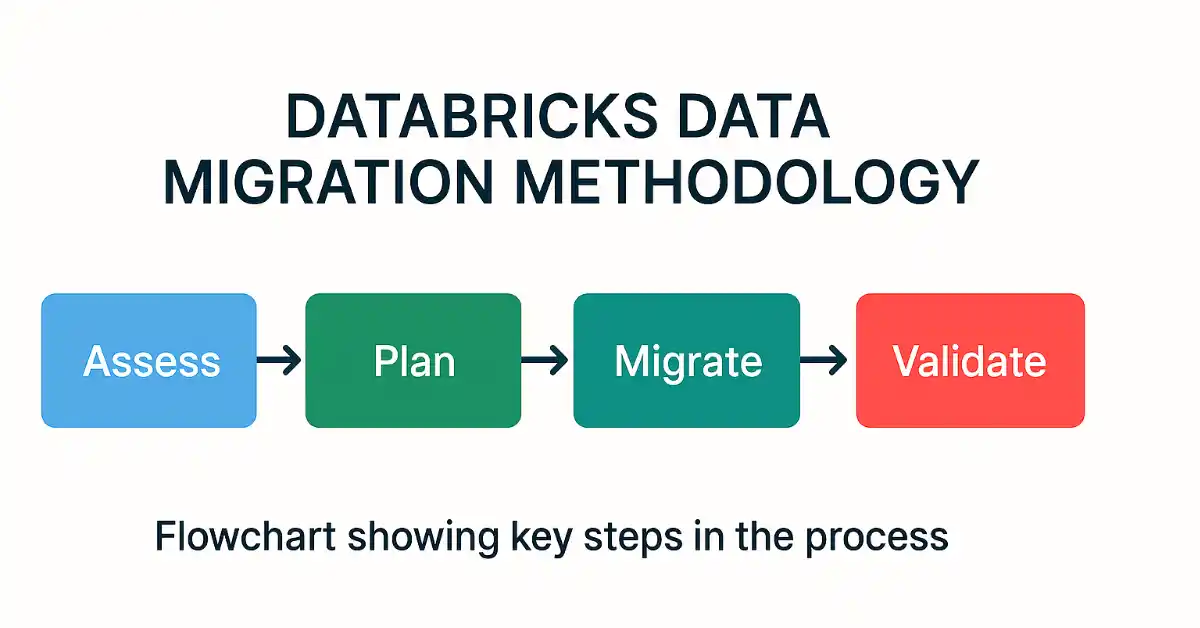
Best Practices for Data Migration Consulting: A Practical Guide for Successful Transitions in 2026
Data migration is one of the most difficult as well as risky tasks in the context of IT transformation being conducted in modern enterprises. It does not matter if an organization is transferring its data to the cloud, updating its outdated systems, or merging data from two or more locations after a merger; even the slightest mistakes during migration can result in data loss, improper usage of the data, and even non-compliance with regulations. This is the reason organizations choose data migration consulting experts in order to have a smooth transaction through planning, the migration process, and the verification of…