Data Protection

Practical Cybersecurity Strategies For RIAs Start With Control
Registered Investment Advisors can strengthen cybersecurity through access management and technical safeguards without massive budgets. Key practices include unique accounts, multi-factor authentication, and least-privilege access to reduce risks and ensure compliance. Focus on control for reliable, visible security aligned with regulations.

Business data protection guide for small businesses
This guide highlights key data protection risks for small businesses, including cyber attacks and lost devices. It emphasizes mapping data flows and adopting habits like password managers, multi-factor authentication, and regular software updates to safeguard operations.
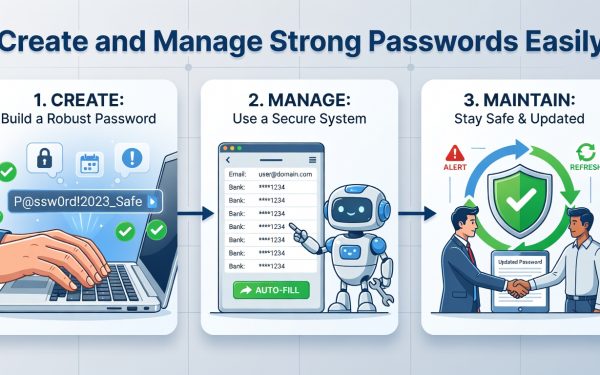
Create and Manage Strong Passwords Easily
This guide teaches beginners how to use password managers like Bitwarden to generate and store secure passwords, avoiding common cyber threats.

Essential Cybersecurity Best Practices for 2026 Protection
Discover proven cybersecurity best practices to safeguard your organization from rising threats, including access controls, training, and emerging AI trends for long-term security.

Why UK SMBs Are Still Losing to Ransomware — and What Actually Works
Ransomware attacks on UK small and medium businesses rose 67% between 2022 and 2024, driven by efficient RaaS models that make SMBs prime targets. These organizations face vulnerabilities from weaker defenses and limited recovery options, leading to average payments of £85,000 and total costs over £250,000. Practical controls can significantly reduce risks for teams without dedicated security expertise.
How Cloud Computing Is Changing Cybersecurity Practices
Cloud computing enhances efficiency but introduces new cybersecurity challenges in distributed environments. The shared responsibility model divides security duties between providers and users, emphasizing the need for expertise to avoid vulnerabilities like misconfigurations. Professionals are increasingly pursuing online advanced education to build specialized skills.

Understanding the CIA Triad: Confidentiality, Integrity, and Availability
Every day, billions of pieces of data travel across networks worldwide—from personal emails and banking transactions to corporate secrets and government intelligence. But what keeps this information safe? What prevents hackers from reading your private messages, altering your bank balance, or shutting down critical systems? The answer lies in three fundamental principles that form the...

Tips to Level Up Physical Data Centre Security
Securing data warehouses and server rooms is equally important as securing the physical infrastructure of your data centres. Many businesses and IT leaders are concerned about the cybersecurity threats, as they are constantly evolving. Beyond firewalls and encryption, there are also many other things that require your attention. The data centre’s physical security is the...

Cybersecurity in 2025: Why Proactive Defense Matters More Than Ever
In today’s interconnected digital landscape, cybersecurity has become a critical priority for individuals, businesses, and governments alike. With the rise of remote work, IoT, and AI-driven automation, the threat surface has expanded rapidly — and so have the risks. From ransomware attacks on hospitals to sophisticated phishing campaigns targeting employees, cyber threats are no longer...

Harnessing Effective Data Leakage Prevention Tools to Safeguard Your Digital Assets
In the digital epoch where information is tantamount to currency, safeguarding digital assets has become crucial for entities of every calibre. Data breaches not only result in substantial financial losses but also erode customer trust and damage brand reputation. As such, it is pivotal for organisations to invest in robust data leakage prevention tools to...