encryption

Best VPN Services Reviewed: Top Picks for Secure Online Protection
Discover the best VPN services reviewed with in-depth analysis, expert insights, and setup guides to enhance your online privacy and security effectively.

Understanding the CIA Triad: Confidentiality, Integrity, and Availability
Every day, billions of pieces of data travel across networks worldwide—from personal emails and banking transactions to corporate secrets and government intelligence. But what keeps this information safe? What prevents hackers from reading your private messages, altering your bank balance, or shutting down critical systems? The answer lies in three fundamental principles that form the...
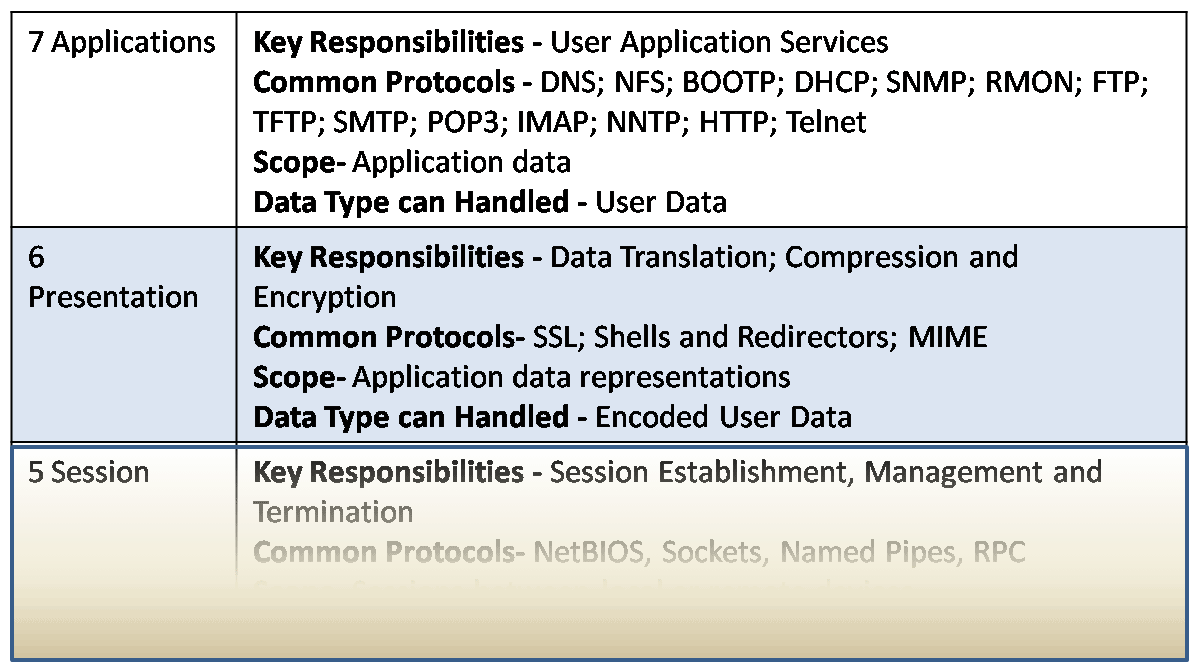
OSI Model, including its 7 Layer Introduction
As the importance of computers grows, vendors recognize the need for networking with them. They produced a variety of protocols whose specifications were not made public. Hence, each vendor had different ways of networking computers, and these ways were not compatible with each other. This means that the computers of one vendor could not be...