
Cybersecurity
Network security, VPN guides, threat detection, and data breach prevention strategies.

Practical Cybersecurity Strategies For RIAs Start With Control
Registered Investment Advisors can strengthen cybersecurity through access management and technical safeguards without massive budgets. Key practices include unique accounts, multi-factor authentication, and least-privilege access to reduce risks and ensure compliance. Focus on control for reliable, visible security aligned with regulations.

Business data protection guide for small businesses
This guide highlights key data protection risks for small businesses, including cyber attacks and lost devices. It emphasizes mapping data flows and adopting habits like password managers, multi-factor authentication, and regular software updates to safeguard operations.
4 Best Deepfake Detection Solutions for Enterprise Identity Verification in 2026
Deepfake attacks on identity verification are surging in 2026 with advanced AI tools enabling synthetic identities and impersonation. Legacy systems fail against these dynamic threats, but leading platforms offer robust detection for enterprises. Review the top 4 solutions for fraud prevention and KYC compliance.

Flixer TV Exposed: Risks of This Pirated Streaming Site
Flixer TV offers free movies but packs legal fines, malware, and downtime. Discover risks, stats, and safe alternatives for secure streaming.

How AI Is Redefining Risk Visibility Across Third-Party Networks
AI is transforming third-party risk management by providing continuous, real-time visibility into vendor networks, replacing outdated periodic assessments. Traditional methods create blind spots as vendors evolve, but AI tracks security signals and vulnerabilities dynamically. This shift ensures teams address actual risks efficiently without chasing false alarms.

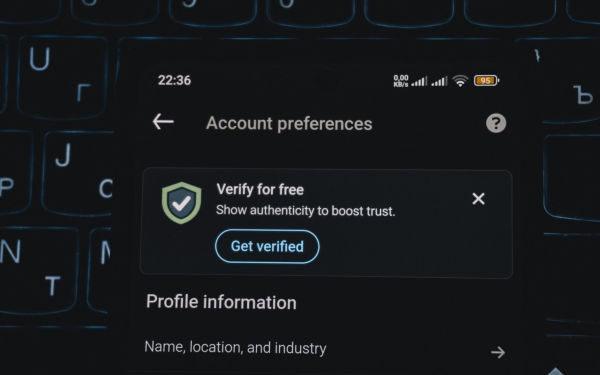
MFA Mastery: Bulletproof Your Accounts in 2026
Stolen passwords cost $4,800 on average—don't be next. This unique guide skips fluff: Scan QR codes, dodge SIM swaps, and add YubiKey power with exact steps pros use to stay unbreakable.

Step-by-Step Guide to Parental Controls for Home Networks
This guide walks you through configuring parental controls to safeguard your family's online experience, covering router access, profiles, and monitoring for better cybersecurity.

Exploring 123movies.go: Risks, Alternatives, and Safe Streaming Tips
Dive into the dangers of 123movies.go and discover secure alternatives for movie streaming, backed by expert insights and data.

Detect and Remove Malware from Your Computer Step-by-Step Guide
This guide equips you with essential steps to spot and eradicate malware, using real tools and strategies to safeguard your device. Avoid common pitfalls and optimize for ongoing protection.

Is Romsfun Safe? Risks, Alternatives, and Expert Insights
Discover if Romsfun poses real dangers for ROM downloads and learn safer options from expert analysis.