Cybersecurity
Welcome to NetworkUstad’s Cybersecurity Hub – your comprehensive resource for staying secure in an increasingly connected world. In today’s digital landscape, cyber threats evolve faster than ever. From sophisticated ransomware attacks to simple phishing scams, businesses and individuals face constant risks. Our cybersecurity section delivers practical, actionable insights to help you build robust defenses and protect what matters most. Whether you’re a security professional, IT administrator, business owner, or someone concerned about digital privacy, you’ll find expert guidance covering everything from fundamental security principles to advanced threat protection strategies. What You’ll Discover: 🔐 Security Fundamentals – Master the CIA Triad, understand information security basics, and build a strong foundation in cybersecurity principles. 🛡️ Threat Intelligence – Learn about different attack vectors, hacker types, malware categories, and emerging cyber threats targeting organizations worldwide. 🔒 Protection Strategies – Explore practical defense mechanisms including encryption, multi-factor authentication, network security, endpoint protection, and access controls. 📊 Compliance & Governance – Navigate regulatory requirements like GDPR, HIPAA, PCI DSS, and industry frameworks such as NIST and ISO 27001. ⚡ Incident Response – Prepare for the inevitable with comprehensive guides on breach detection, containment, recovery, and forensic analysis. 🚀 Emerging Technologies – Stay ahead with insights on AI security, cloud protection, IoT vulnerabilities, blockchain security, and quantum computing threats. 💼 Enterprise Security – Discover strategies for securing hybrid workforces, protecting corporate data, managing third-party risks, and building security-aware cultures. 🎓 Career Development – Explore ethical hacking careers, certification paths (CEH, CISSP, OSCP), and skill development resources. Our articles combine technical depth with practical applicability. We break down complex security concepts into digestible insights, provide real-world examples, and offer step-by-step implementation guides. No unnecessary jargon—just clear, actionable cybersecurity knowledge you can use immediately. From understanding basic threats to implementing enterprise-grade security architectures, NetworkUstad’s cybersecurity content empowers you to make informed decisions and take meaningful action. We cover the full spectrum: network security, application security, data protection, cloud security, mobile security, and everything in between. Security isn’t a one-time project—it’s an ongoing journey. Join thousands of readers who trust NetworkUstad to keep them informed about the latest threats, best practices, and innovative solutions in cybersecurity. Protect your network. Secure your future. Start exploring our cybersecurity resources today.

Cloud Attacks: A Threat to Our Digital Lives
Imagine a city in the clouds, a digital, data-filled metropolis. This revolutionary concept has changed the way we store, access, and share information. But like any bustling city, the cloud has its own dangers, called “cloud attacks.” Cybercriminals lurk in the shadows, seeking to exploit weaknesses and steal our digital treasures. These cloud attacks represent...

Understanding IoT Attacks: Types, Impact, and Prevention
The Internet of Things (IoT) has changed technology. It connects everyday devices to the internet, making life more convenient and efficient. However, this interconnectedness also introduces significant cybersecurity risks. We must know about IoT attacks, their types, and how to prevent them. It’s vital to protect our digital lives. What is an IoT attack? An...

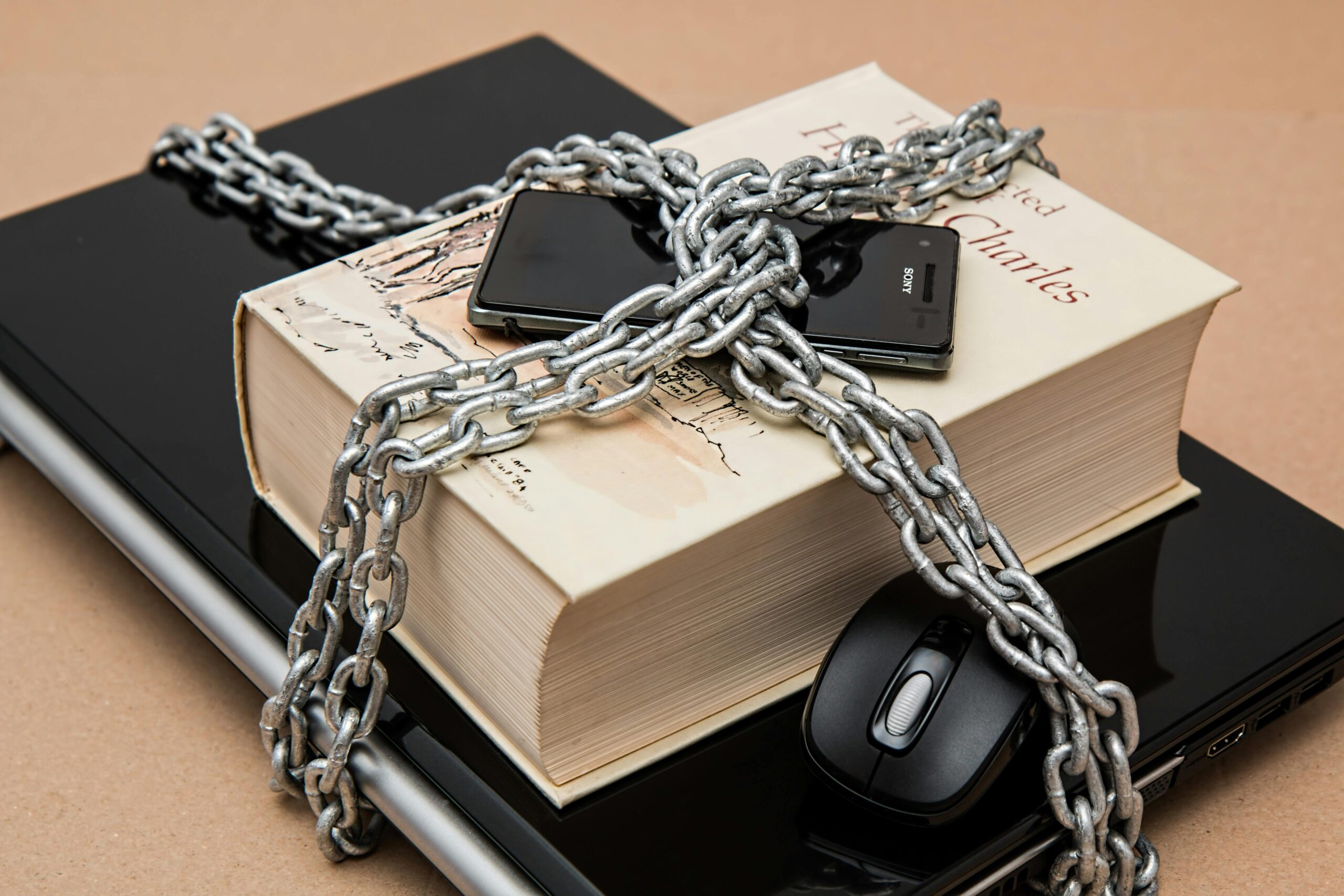
Exploring Data Breaches: Insights into Security Vulnerabilities
Data breaches have become a significant concern in the digital age, affecting organizations of all sizes and individuals. A data breach occurs when unauthorized individuals access sensitive, protected, or confidential data. This can include personally identifiable information (PII), financial records, health data, and corporate information. The implications of data breaches can be far-reaching, leading to...

The Insider Attack: A Silent Danger
Insider attacks pose a grave threat to companies. Current or former employees and contractors with authorized access can wreak havoc undetected. They bypass security and misuse their access. They steal data, sabotage systems, or cause damage. Internal rogues pose a distinct threat, working from inside organizations. Their familiarity with internal processes allows them to strike...
Exploring the Advantages of Proxyium in Data Protection
In a digital age, facts become a valuable asset, requiring robust protection. We traverse the online realm, creating digital trails vulnerable to exploitation. Threats to our privacy and security can manifest identity theft and fraud. Traditional safety features are incomplete to counter cybercriminals’ sophisticated methods. This is where Proxyium emerges. It is a complete privacy...
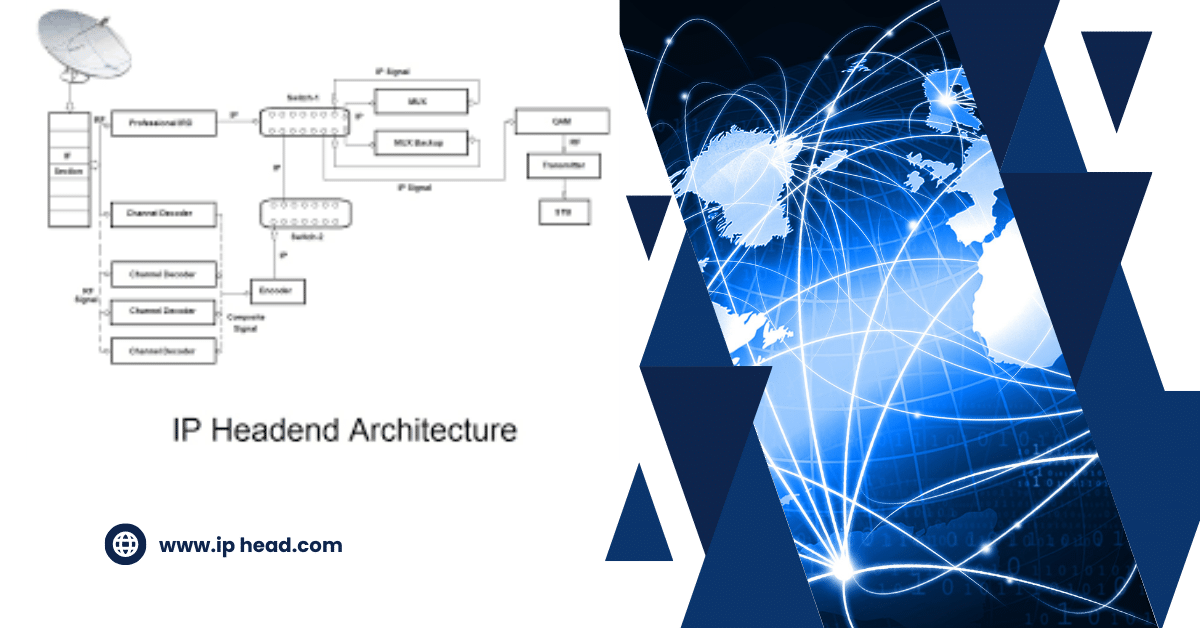
IP Header: Internet Communication
In the vast realm of the internet, communication is a complex dance of data packets, and at the forefront of this intricate performance is the IP header. Serving as the gateway to an Internet Protocol (IP) packet, the IP header is vital in the seamless exchange of information across IP networks. Components of an IP...

8 New Cybersecurity Tools in 2024
E-commerce has ushered in a new business system with a shift to online transactions. Companies operate websites with vast volumes of sensitive data crucial to their survival and are continuously at risk of attack from cybercriminals. Individuals are equally at risk, and cybersecurity innovations are needed to mitigate this challenge. Businesses and individuals should evaluate...

How to Enhance Security at Your Hybrid Organization with Endpoint Detection and Response
In an era where the traditional office boundaries blur into the digital realm, ensuring robust security measures for your organization’s data and assets becomes paramount. The hybrid work model, a blend of remote and on-site work, while offering flexibility and efficiency, also introduces complex security challenges, especially at the endpoints—the frontline in the battle against...

Whoer.net Review: Unlocking Online Privacy and Security
Privacy and security in the digitized world are not political choices for people but necessary ones. With cybersecurity having become a daily activity to defend your data, using products to help you be safe from online crimes is no longer optional. I arrived at Whoer.net, an all-inclusive online service that prevents you from roaming the...
What is Zero-Trust Security?
With traditional cybersecurity methods increasingly becoming obsolete, securing sensitive data has become vital for network security. This is where Zero-Trust Network Access Security turns the conversation. It is a groundbreaking tech solution that provides security and challenges the conventional notion of trust among network users. This security system stands on a zero trust principle. What...