
Cybersecurity
Network security, VPN guides, threat detection, and data breach prevention strategies.
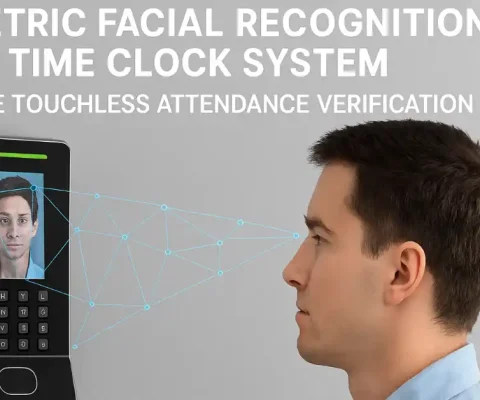
Balancing Privacy and Verification in Employee Attendance Hardware
Inaccurate time tracking is more than a minor administrative headache; it’s a significant drain on your company’s bottom line. For every minute unaccounted for, profitability erodes. Yet, as an operations manager, you face a critical challenge: how do you implement robust employee verification without crossing the line into privacy intrusion? This is the biometric threshold—the...

Protecting Investor Trust Through Streamlined IT and Enhanced Security Protocols in 2026
For any financial services firm, investor trust is the most valuable asset. It’s the bedrock of client relationships, the foundation of firm reputation, and the engine of growth. In today’s digital landscape, that trust is inextricably linked to your technology posture. A single vulnerability or operational failure can have devastating consequences. The stakes have never...

What is Information Security vs Cybersecurity: Key Differences
You’ve probably heard both terms thrown around—information security vs cybersecurity. Many people use them interchangeably. But are they really the same thing? Not quite. While they overlap significantly, understanding the difference is crucial for anyone working in IT, managing business security, or simply trying to protect their digital assets. Let’s clear up the confusion once...

Preventing Ransomware Through Secure Remote Access Design
Ransomware has become one of the most damaging cyber threats facing organizations today. With remote work and cloud-based operations becoming standard, attackers increasingly exploit weak remote access points to infiltrate business networks. Without proper security design, remote connections can quickly turn into costly vulnerabilities. Building a secure remote access infrastructure is now essential for protecting...

Understanding the CIA Triad: Confidentiality, Integrity, and Availability
Every day, billions of pieces of data travel across networks worldwide—from personal emails and banking transactions to corporate secrets and government intelligence. But what keeps this information safe? What prevents hackers from reading your private messages, altering your bank balance, or shutting down critical systems? The answer lies in three fundamental principles that form the...

Cybersecurity Fundamentals 2026: Build Strong Defense in 60 Days
Cybercrime will cost the world $10.5 trillion in 2026. That’s more than the GDP of Japan. Every 39 seconds, a hacker attacks somewhere on the internet. Your business could be next. But here’s the good news: most attacks succeed because of weak fundamentals, not advanced hacking. Fix your basics, and you block 90% of threats....

Why Your Hybrid Team’s Home Office Is the Weakest Link in Your Corporate Security
The shift to hybrid work has been a game-changer for businesses, offering unprecedented flexibility, attracting top talent, and boosting productivity. But this new freedom has a hidden cost: it has fundamentally shattered the traditional concept of corporate security. Your company’s secure perimeter is no longer the four walls of your office; it now extends to...

Vbmejor.com Legitimate or Scam? 2026 Warnings and Real Alternatives
In the ever-evolving world of online gaming, Fortnite remains a powerhouse, captivating millions with its battle royale action, creative modes, and vast array of customizable items. At the heart of Fortnite’s economy lies V-Bucks, the in-game currency used to purchase skins, emotes, and battle passes. With over 650 million registered players worldwide as of 2026...

Audit of Smart Contracts: Does Your Project Really Need It?
In a world powered by Web3 technology, there is no undo feature. Once transactions are executed on the blockchain through a smart contract, they cannot be reversed. Since the code of most smart contracts is publicly accessible (which also means hackers can inspect it), potential vulnerabilities become easier to discover and exploit. This makes Web3...

Cybersecurity Management for E-Commerce Businesses: A Complete Guide
As online shopping continues to expand, cybersecurity has become one of the most critical responsibilities for every e-commerce business. Whether you run a large digital storefront or a small boutique, protecting customer data and maintaining platform integrity are essential to long-term success. Modern cyber threats are sophisticated, and a single vulnerability can damage your reputation,...