Search Results
Showing results for "business" (3310 articles found)

How to create content for social media
In today’s marketing tactics, content development is essential. Even though almost 90% of all businesses participate in some form of content marketing, only a small percentage can create viral material that consumers share. Content cannot achieve its actual function without this degree of involvement.In the last several years, the role of social media in marketing...
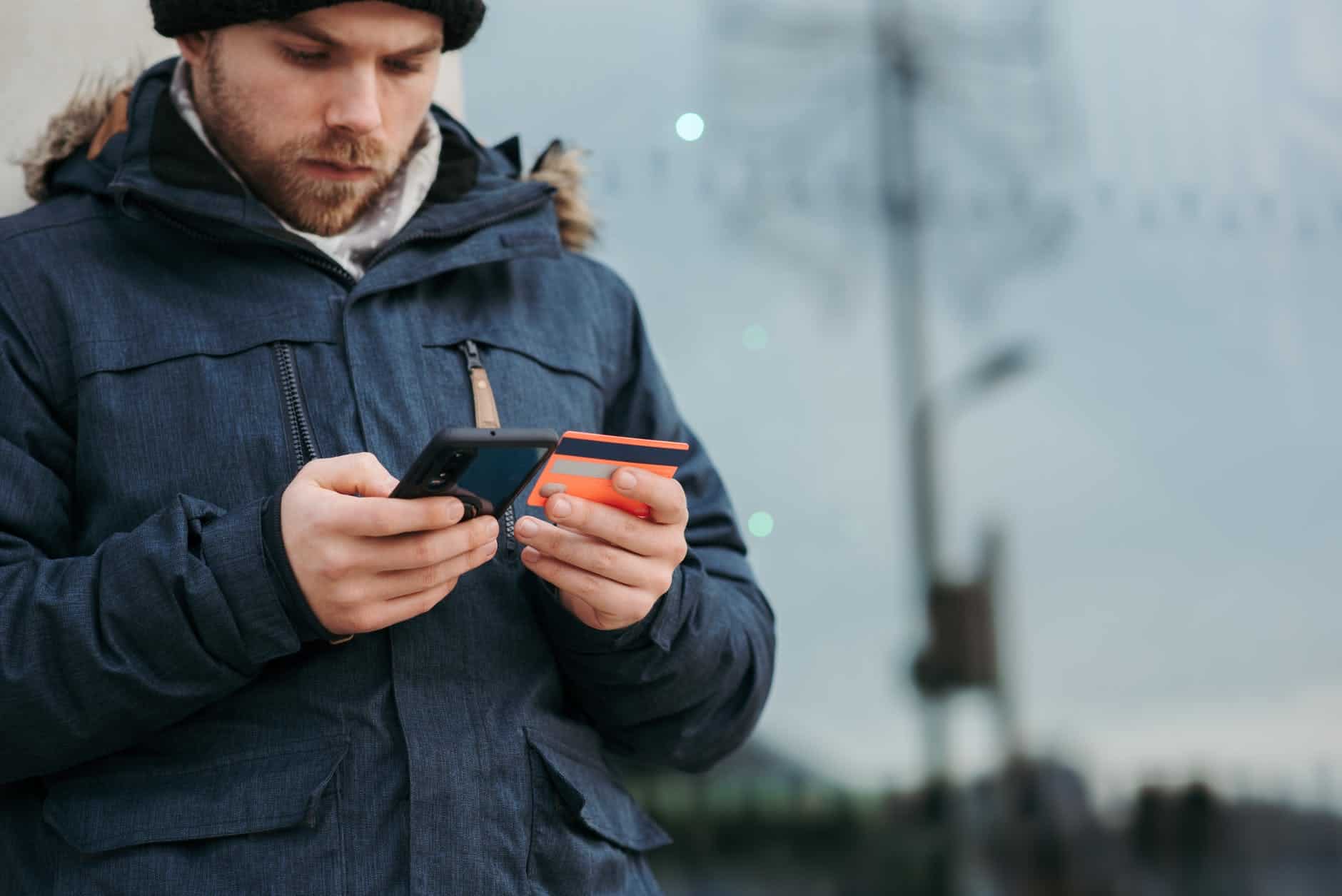
5 Strategies to Avoid Getting into Credit Card Debt
Flexible spending, enticing rewards, cash backs, and avoiding short-term financial shortages are some of the best things about credit cards. But they can be expensive enough when the convenience becomes a huge wall of credit card debt. No one really wants to get into debt. It is one of the things that occur without your...

Top Tax Advantages of Buying a Home
When you planned to buy your home, you probably did not think ahead about your taxes. The good news is that buying a house helps you with your taxes. Buying a new home offers a few advantages to renting. The federal government offers numerous personal tax deductions on homeownership but no credits. What’s the difference?...

Vlone What Makes It the Best Online Clothing Store
Internet shopping is now more widespread in current generations. People prefer to shop online instead of visiting physical establishments. As the COVID-19 disease outbreak spreads, more people can shop online. It is because of its numerous advantages. When you buy something online, you can view it before buying it, and you won’t have to stand...

Top Advantages of Rush-Hour Package Delivery Services
Each one of us has a lot of tasks that we want to complete on time. We are finding ways to complete them with the help of the latest innovations in technology. Paperwork, contracts, and mail packages are no exception to this situation. If you want quick delivery services for your packages, you can receive...

Python for Cybersecurity: Why Is It Better?
Cybersecurity is an international concern. Everyone wants to prevent high-profile breaches as much as possible, and Python is helping ethical hackers achieve that. According to various studies and sources, including cybersecurity reports and statistics, here are some alarming numbers: Here are some updates in 2024 on hacking and cyber attacks ¹: Remember that these numbers...

Hidden Instagram SEO Tips – Must Know About
Instagram is the third most popular social media platform after Facebook and YouTube, with over one billion monthly users. The app is the second most popular on the Apple Store. Your rivals will have a field day if your social media management approach does not include Instagram. Instagram is a visual platform. Posting on Instagram...

Online Threats: Why Do You Need a Reliable Online Converter?
When it comes to your employees’ Internet usage, don’t underestimate the potential for harm to your company. Due to the serious nature of many online threats, even one unmonitored employee on a single unmanaged system can wreak havoc on a company’s internal network, erase crucial data irreversibly, and ultimately jeopardize the company’s ability to conduct...

Criminal Records – Investigating the Process of Running a Criminal Check
How often have you turned on the news hoping to see the weather report but then being told about “real-life crime?” We are constantly being bombarded with horror stories, no matter where we turn these days. But, unlike a gripping book we can’t stop reading, these stories are all around us. Criminals are targeting us...

Creative Ways to Decorate With Uvanti Christmas Lights
Personalized Christmas Lights brings true life to a house during Christmas. Each year they are the best accessory for the holiday season. Every color imaginable. Almost indestructible. A Christmas light taillight is a great Christmas holiday home lighting system for the whole family. You can even use them at the office and be just as...