Network Management is critical for businesses, IT teams, and even CCNA students learning the ropes. Two fundamental approaches—in-band and out-of-band (OOB) management—determine how administrators monitor, configure, and troubleshoot devices.
This guide’ll break down these concepts, compare their pros and cons, and explore real-world use cases. By the end, you’ll understand when to use each method and how modern trends like automation and cloud tools are changing the game.
In-band management interfaces and ports
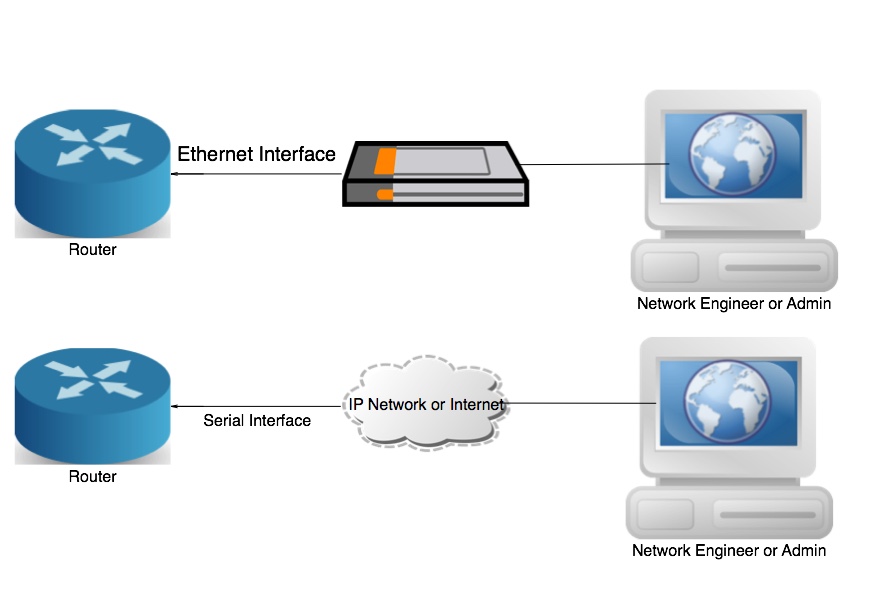
The Image above illustrates the in-band Network Management. In-band router interfaces are the LAN (i.e., Gigabit Ethernet, Fast Ethernet, and Ethernet ) and WAN (i.e., eHWICs) interfaces configured with IP addressing to carry user traffic. Ethernet is the most common LAN connection. DSL and serial ports are the standard WAN connections. In-band manages devices locally through the network, using a telnet and SSH connection to a router. The SNMP-based tools are also used to manage devices using in-interfaces.
It is a usable method of managing a network. In-band network management is not enough for an extensive network because, in case of a fault in the network, it is tough for the network administrator to reach the affected devices and resolve the problem. Therefore, an alternate or secondary management method requires determining the problem or accessing the source of the problem. The second method is Out-of-Band Management (OBM) interfaces.
How It Works
In-band management relies on existing network infrastructure:
- Protocols like SSH, Telnet, or HTTP/HTTPS.
- Traffic shares bandwidth with regular user data.
- Requires the network to be operational for access.
Common Protocols & Ports (CCNA Focus)
For CCNA students, here are the key protocols and ports used in in-band management:
- SSH (Port 22): Secure remote access for CLI configuration.
- SNMP (Port 161): Monitors device performance (e.g., CPU usage).
- HTTP/HTTPS (Port 80/443): Web-based interfaces (e.g., Cisco WebUI).
- NETCONF (Port 830): Modern API-driven configuration.
(Example: Use ssh admin@192.168.1.1 to access a Cisco router via in-band.)
Out-of-Band Interfaces and Ports
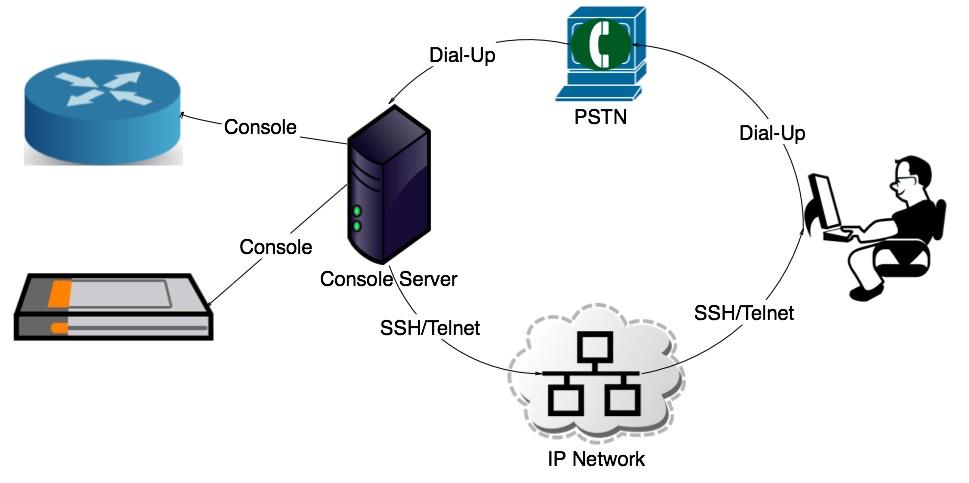
The above Diagram illustrates the Out-of-Band Network Management. Suppose a device, such as a switch or a router, has a problem, and traffic cannot flow through the network. The administrator needs an alternate path to reach the network nodes and diagnose the problem even when the network is down. In that case, this situation needs Out-of-band access to the network. All Management ports, including console and AUX ports, are types of out-of-band access interfaces. Out-of-band access refers to a dedicated management channel for configuration and management.
Out-of-band management offers a helpful alternative for accessing network nodes when needed. It encompasses a variety of manageable equipment and smart devices that might not be directly connected to the data network. This includes valuable items like uninterruptible power supplies, PSTN, PBX phone systems, and intelligent thermal controls.
For large and critical networks, in-band management interfaces are not enough. These networks need a secure remote connection, a network access path to manage and troubleshoot when the device is not on the network, the device is not network manageable, or the data network is down.
How It Works
OOB creates a “backdoor” for administrators:
- Physical serial cables, dedicated management ports, or 4G/5G modems.
- Operates independently of the production network.
- Critical for emergencies (e.g., total network failure).
OOB in Modern Networks (Cloud & Automation)
Today, OOB isn’t just about serial cables. Examples include:
- Cloud-Based OOB: AWS Systems Manager or Azure Serial Console for remote access.
- Automation Tools: Platforms like Ansible or Terraform use OOB to deploy configurations during outages.
In-Band and. Out-of-Band: Pros and Cons
Let’s compare the two approaches side-by-side:
| Factor | In-Band | Out-of-Band |
|---|---|---|
| Cost | Lower (uses existing infrastructure) | Higher (requires dedicated hardware) |
| Complexity | Simpler setup | More complex (separate channels) |
| Reliability | Depends on network health | Works during outages |
| Security | Vulnerable to network attacks | More secure (isolated) |
Security Implications
- In-Band Risks: Hackers who breach the primary network can hijack management traffic (e.g., SNMP vulnerabilities).
- OOB Advantages: Acts as a “secure air-gapped” channel. For example, hospitals use OOB to protect medical devices from ransomware.
When to Use In-Band or OOB
In-Band Use Cases
1. Routine maintenance (e.g., updating switch configurations via SSH).
2. Small networks with limited budgets.
3. Monitoring traffic flows with SNMP.
OOB Use Cases
1. Disaster recovery (e.g., rebooting a frozen router via a serial console).
2. Large data centers requiring 24/7 uptime.
3. Secure environments (e.g., government networks).
Hybrid Approaches
Many organizations now combine both methods:
- Use in-band for daily tasks (cost-effective).
- Deploy OOB for emergencies (e.g., Cisco’s Integrated Management Controller).
Modern Trends in Network Management
Cloud-Based OOB
Tools like AWS Outposts or ZPE Systems’ Nodegrid allow remote OOB access via the cloud. Benefits:
- No on-site hardware required.
- Global access (fix a Tokyo router from New York).
Automation & DevOps
- Ansible: Automate OOB recovery tasks (e.g., reboot devices via Redfish API).
- Terraform: Deploy network configurations during outages.
Zero Trust Security
OOB supports Zero Trust by isolating management traffic. Example: Google’s BeyondCorp uses OOB for secure access.
Practical Guide for CCNA Students
Lab Setup Recommendations
- In-Band Practice: Configure a VLAN on a Cisco switch using SSH.
- OOB Practice: Use a USB-to-Serial adapter to access a router’s console port.
Key Commands to Learn
ssh -l admin 10.0.0.1(In-band access).show running-config(View settings).reload(OOB reboot via console).
Cost Comparison: DIY vs. Enterprise Solutions
| Solution | Cost | Best For |
|---|---|---|
| DIY Serial Console | 50−50−100 | Students/SMBs |
| Cisco IMC | $2,000+ | Large enterprises |
| Cloud OOB (e.g., AWS) | Pay-as-you-go | Hybrid networks |
Real-World Case Studies
Case 1: Hospital Network Downtime
A Boston hospital used OOB to restore MRI machines during a ransomware attack. Management traffic stayed isolated, preventing further spread.
Case 2: E-Commerce Site Recovery
An online retailer used AWS Systems Manager (OOB) to reboot crashed servers during Black Friday, saving $1M in lost revenue.
Conclusion
In-band and out-of-band management serve different purposes. While in-band is cost-effective for daily tasks, OOB is a lifesaver during crises. For CCNA students, mastering both is key to becoming a versatile network engineer.
FAQs
What is the primary difference between in-band and out-of-band network management?
In-band uses the main data network for management traffic, while out-of-band relies on a separate, dedicated channel.
Why is out-of-band management considered more secure?
It isolates management traffic from the primary network, reducing exposure to data-path vulnerabilities.
Can in-band and out-of-band management be used together?
Yes, hybrid setups combine both for redundancy and flexibility during network failures.
What industries benefit most from out-of-band management?
Industries requiring high uptime, like finance, healthcare, and cloud services.